- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Allow only MS Intune and Windows Update - block all internet access
- LIVEcommunity
- Discussions
- General Topics
- Re: Allow only MS Intune and Windows Update - block all internet access
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Allow only MS Intune and Windows Update - block all internet access
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 04:41 AM
HI,
I am after permitting only MS Intune and Windows Update - block all internet access.
I have followed the custom URL filtering as mentioned in the link below:
Created the custom url filter:
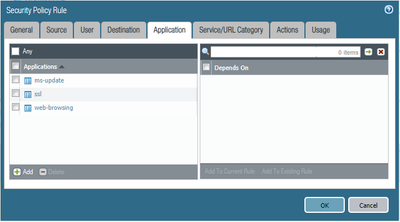
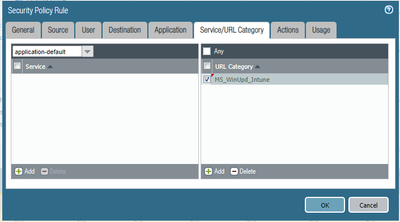
then created a policy allowing - web-browsing, ssl and ms-update
selected correct URL-category::
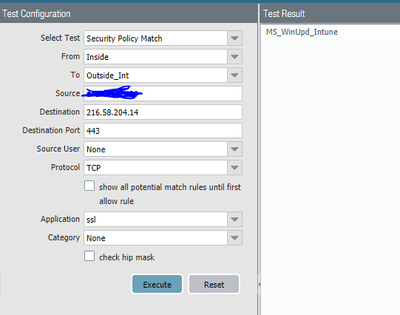
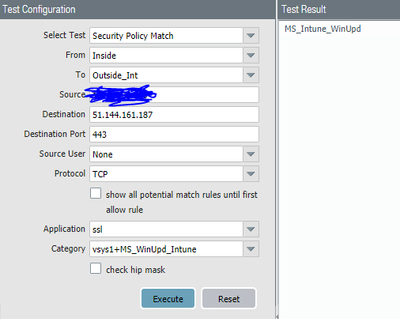
Time to Test: destination IP is for portal.manage.microsoft.com and it hits the correct policy
but when I try with google.com IP address, that also hits the same policy
From the above it seems that google.com will also be allowed?
I dont have an actual host to test the same, hence tested it from the Troubleshooting section of the firewall.
To me it seems that the firewall is permitting any url being accessed over ssl, and ignoring the URL category.
The main reason for using custom URL filter is that I want to use wildcard FQDN.
Can someone suggest why the URL filtering is not taking effect.
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 07:28 AM
Hi @kams19
With that rule theoreticaĺly every IP will match. Because of that you also configured the custom URL category. So when a host tries to connect to google.com, the tcp handshake will succed, but in the TLS handshake, the firewaĺl will see the hostname and from that point on the connection will no longer match your windows update rule and it will be dropped (except if you have some more rules that could match for that connection). In the policy match test, if you choose also the URL category, then the result will show what you actually expected.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 07:39 AM
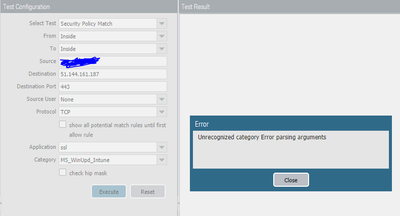
HI @Remo, Thanks for your reply, now I understand the logic behind this. I did select the URL category as you mentioned but I am getting this error now:
Any idea why this should happen?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 08:28 AM
@kams19 it looks like this is a bug. Only the paloalto url categories work and every custom url category leads to this error. I tested with PAN-OS 10.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 08:51 AM
For CLI, PA has mentioned the workaround as per https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PLjeCAG
But that is assuming multi vsys config. My case is single vsys and single virtual router. There is no option on GUI to select vsys and VR.
I believe tomorrow I should have someone on site and I will ask them to connect their laptop to verify this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 09:28 AM
Hi @kams19
Thanks for bringing this to my attention. With this I tried again. So if you manually add "vsys1+" in front of the URL category name, the test works and no longer shows an error. I also tested on a firewall with a single vsys - so there is only vsys1.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 09:34 AM
I dont have ssh connection to the firewall at the moment, trying to get my local laptop firewall sorted.
I dont think there is a way this can be done from GUI?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 09:44 AM - edited 08-13-2020 09:50 AM
What I meant was that you should add "vsys1+" in the GUI. At least in my case it was working in CLI and WebUI.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-13-2020 10:31 AM
ok got it working on the Troubleshooting section-
will see how the policy is applied in action tomorrow and update
- 13946 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Enforce GlobalProtect Access Based on Microsoft Intune Compliance Status in GlobalProtect Discussions
- PAC File for Prisma Access China in Prisma Access Discussions
- Beginner Question Understanding Basic NAT and Traffic Flow in Palo Alto Firewall in General Topics
- How to add Wildcard Domains as a destination for Firewall policy PA1420 in General Topics
- Global Protect Internal Detection in GlobalProtect Discussions