- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Application Dependency question (l thought l knew it)
- LIVEcommunity
- Discussions
- General Topics
- Application Dependency question (l thought l knew it)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2017 03:53 AM
Heys,
A bit confused now :0
My policy as below:
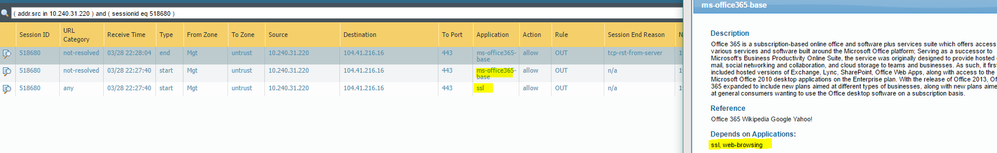
So port 80 is allowed when l attempting to connect to the device over the web browser (Chrome) but after Palo actually identified that this is not a "panos-web-interface" app (based on tcp 3 way handshake and some data) didn't the response to the request. I understood that there is no other way to do it unless you got a sufficient data to identified the app hence fist packet is allow based on destination port and session is created.
Another policy snip:
This may not be the best example but for "http-video" (along with other app`s) my Depends on Applications: web-browsing.
My question is what is classified as a web-browsing (it is purely any web-browser request or something more specific) and what else will be allowed if my policy permit two application: https-video and web-browsing? What if l will be surfing the lnternet over the Chrome doest it means that any web-browsing traffic (requests) is allowed and will be successful ?
Thx,
Myky
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2017 12:45 AM
The child app depends on the parent, because the child can only be identified _after_ the parent has been identified by AppID (the first thing AppID sees is the parent's behavior, so identifies as the parent, then the session starts to send child payload and AppID can change to the child app)
The parent app is sort of the transport layer for the child app
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2017 05:14 AM
any web based application will usually start off as web-browsing (hence the whole dependency thing)
when you start any web based session you'll first have the 3 way handshake, which does not permit you to identify any application short of using port 80, next comes a http get (this is web-browsing)
if all you are getting is an average website, the application will remain web-browsing
if, however, you go into more specific applications (http-video , facebook,.. ) AppID will change the application to what is most accurate
so for an application that has a dependency, it means that there is no way (for AppID) to anticipate the application will become the final application, without first having been the dependency app
hope this makes sense?
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2017 07:41 AM - edited 03-28-2017 07:56 AM
Hello @reaper
Thanks for clearing this up for me. Hmm. I thought in a bit different way. Let's say l do have an app dependent on the web-browsing (assume it is http-video as in out example). For http-video traffic/application to work you must meet both (web-browsing and http-video) criterias however, if you are only meeting one criteria (especially when hitting dependent application only) in our case it is web-browsing traffic will not be permitted (after the firewall clearly identified that the app is pure web-browsing). When the session is created on PA, in the monitoring tab we only able to see a final application as a result of the session id engine scan? When we do > show session id xxxx in the application field the app won't change or it can if l change the application from web-browsing to http-video:
Or it is going to be a completely new session? Hope l am not confusing you or anyone or talking s**t:0
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2017 09:38 AM
The criteria are sequential
At session setup it's the 5 tuples (src zone, src subnet, dst zone, dst subnet, dst port)
Next is 5 tuple + initial app/dependent app/parent app
Next 5 tuple + child app
To get to the child app you need to pass the previous security checks
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2017 11:27 AM
The majority of the sessions that I deny I have log-start and log-end set to yes exactly for this reason. I like to be able to show to people that while we do block certain applications (bittorrent) it takes a quick second to actually id the traffic. That way when I get the lovely copyright notices I can argue with them about the legitimacy of the claim 😉
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2017 02:39 PM - edited 03-28-2017 04:08 PM
Hello again,
Now l can see when enabled "Log at Session Start" that this is the same session ID and can see how the app is changing from parent to the child. Nice explanation!
Do you know if the child app which depends on the application (let's say web-browsing) because it is using the same port 80 (or because it is working in the conjunction/over the web-browsing app). ln our case SSL port 443.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2017 12:45 AM
The child app depends on the parent, because the child can only be identified _after_ the parent has been identified by AppID (the first thing AppID sees is the parent's behavior, so identifies as the parent, then the session starts to send child payload and AppID can change to the child app)
The parent app is sort of the transport layer for the child app
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2017 12:56 AM
Great! Exactly what l wanted to understand. Thanks as always
- 1 accepted solution
- 6214 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- host-insights apps refresh in Cortex XDR Discussions
- SD-WAN with ION's running 6.5.1-b5 performance issues in Prisma SD-WAN Discussions
- Get Application Tags via API in Strata Cloud Manager
- Policy destination field when using URL filtering in Next-Generation Firewall Discussions
- XQL Question - Cortex > Host Inventory > Applications Result View in Cortex XDR Discussions