- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Best Practice policy 7.1
- LIVEcommunity
- Discussions
- General Topics
- Re: Best Practice policy 7.1
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2016 09:23 AM - edited 11-08-2016 09:54 AM
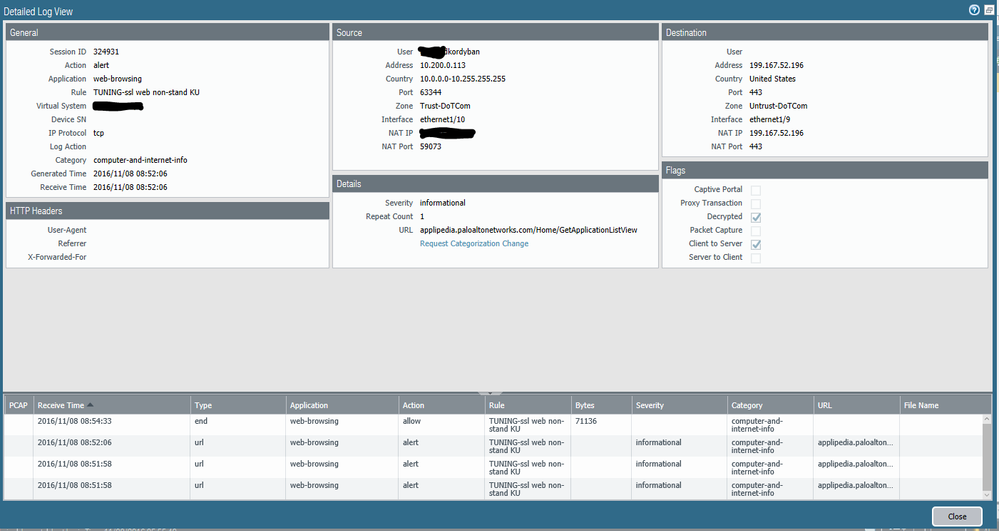
I am attempting to implement best practice internet gateway in the 7.1 admin guide. One on the steps toward the end is creating Temporary tuning rules to see what applications are communicating over non-standard ports. I have rule above the tuning rules allowing for web-browsing and ssl over "application-default" I was surprised on the amount of traffic that was hitting these Temp rules. Having trouble understading logic. Why would browsing to applipedia.paloaltonetworks.com show as application "web-browsing" to port 443?
note:
We do have outbound SSL decryption on. See log attached.
Thanks for you time
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-10-2016 07:26 AM
There is a rule below all of my user rules that specifies access for certain people with just the service being defined as http/https. I will say that I did look through my logs yesterday and 99% of our web-browsing is all just the ssl,web-browsing rule. Only the technology service bureau here actually has access to anything that doens't fall under the ssl,web-browsing rule and it has never been an issue. However, we also don't decreypt any of the traffic for this facility so most applicaitons never get identified.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2016 11:08 AM
Could you post a screenshot of the rules that you have created for tunning. If you create a rule for SSL and Web-Browsing with applicaiton default ports then almost all common web-browsing is going to hit those rules and I would suspect that hardly any of the sites that you visit are using anything but 443 or 80.
As far as web-browsing sometimes coming across over 443 identified traffic I wouldn't be to concerned, I currently have four pages that match that criteria in an enviroment where we don't keep logs long. App-ID is not flawless by any means and while web-browsing is only supposed to be tcp/80 it can get caught up as tcp/443 sometimes.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2016 11:27 AM
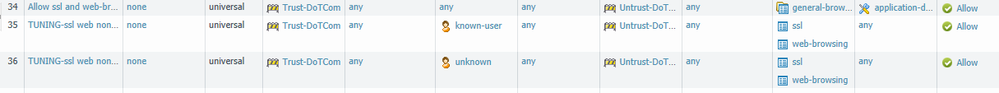
Thanks for the reply. I do have a rule (34) that is configured for web-browsing and ssl (general-browsing app group) above my tuning rules.
I guess implementing the the best practice outlined in the 7.1 guide would never be complete then. I mean if app id doest work correctly then how would you get rid of the tuning (catch all) rules.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2016 01:20 PM
I'm not really saying that App-ID doesn't work, but things sometimes get messed up depending on the website you are visiting and what not; I wouldn't say that you should really worry about it to much as the four pages of logs that I have are all going to one address that is an add network, so clearly if it started to get blocked I wouldn't care.
What applicaitons are actually breaking when you take out the TUNING rules and just run with the Allow ssl and web-browsing rule? Nothing should really break because of it, generally the only time that I run into an issue is when some web-dev decides to use port 85 or some other random site on a production webserver. If you start running into a lot of issues try running a PCAP and see what is actually being sent, you shouldn't really be having any issues with the SSL and Web-Browsing app-ids even when you don't do any decryption.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2016 01:26 PM
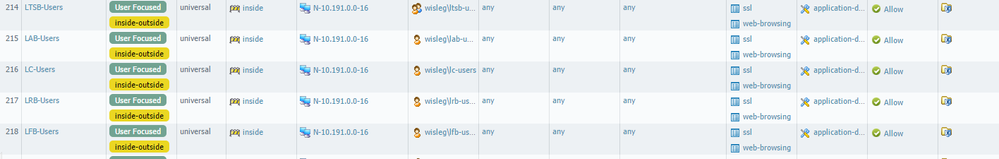
This is what my user rules look like; as you can see I am using ssl and web-browsing as the applicaiton with application-default as the service. I have yet to run into any issues except for a few crappy websites put out by small organizations that use weird ports. We do not recieve any issues with these users at all about not being able to access anything. Run without your TUNING rules and see what brakes, I'm guessing not much and you can create rules for the cases where you actually need access to those websites.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 03:31 AM
Hello Experts
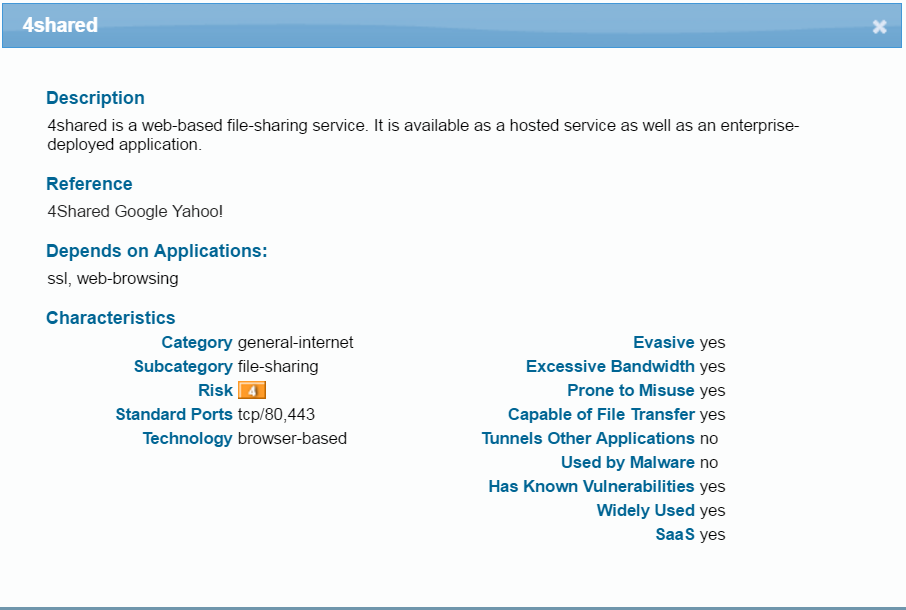
Just want to ask something silly, if user browse www.4shared.com and in policy I only allow SSL, Web-browsing application on application-default then it will work? Because if PA identify deeper applicaiton running on Web-browsing then it will be block as its not allow in policy? Please answer
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 05:57 AM
If you allow SSL and Web-Browsing on the default ports then 4shared will be allowed since it only uses the default ports.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 06:43 AM - edited 11-09-2016 07:03 AM
Hi,
That doesn't seem correct.
Allowing SSL and web-browsing using application defaults won't allow access to http://www.4shared.com.
The application will be identified as 4shared and will be denied by policy if you haven't allowed this application :
Session 22777
c2s flow:
source: 192.168.0.28 [lab-100]
dst: 199.101.134.234
proto: 6
sport: 61604 dport: 80
state: INIT type: FLOW
src user: unknown
dst user: unknown
s2c flow:
source: 199.101.134.234 [untrust]
dst: 172.16.31.170
proto: 6
sport: 80 dport: 24526
state: INIT type: FLOW
src user: unknown
dst user: unknown
start time : Tue Nov 8 21:55:22 2016
timeout : 90 sec
total byte count(c2s) : 5242
total byte count(s2c) : 66
layer7 packet count(c2s) : 11
layer7 packet count(s2c) : 1
vsys : vsys1
application : 4shared
rule : interwebs-1
session to be logged at end : True
session in session ager : False
session updated by HA peer : False
address/port translation : source
nat-rule : NaT to interwebs(vsys1)
layer7 processing : completed
URL filtering enabled : True
URL category : online-personal-storage
session via syn-cookies : False
session terminated on host : False
session traverses tunnel : False
captive portal session : False
ingress interface : ethernet1/2
egress interface : ethernet1/1
session QoS rule : N/A (class 4)
tracker stage firewall : l7 proc
end-reason : policy-deny
Cheers,
-Kim.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 07:01 AM
My appologize, kiwi is correct my logs hadn't updated when I ran a quick test of it
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-09-2016 12:43 PM
@BPry then how come your internet browsing is working with allow only SSL/Web-browsing application, as you post the screen shot of your policies
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-10-2016 07:26 AM
There is a rule below all of my user rules that specifies access for certain people with just the service being defined as http/https. I will say that I did look through my logs yesterday and 99% of our web-browsing is all just the ssl,web-browsing rule. Only the technology service bureau here actually has access to anything that doens't fall under the ssl,web-browsing rule and it has never been an issue. However, we also don't decreypt any of the traffic for this facility so most applicaitons never get identified.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-12-2016 04:24 AM
I want simpler approach to policy mgmt. I am experimenting with just have one rule that allows all risk 1-4 apps. Above that I block all risk 5 apps. Then above that just have individual allow/block rules for stuff that needs "special" consideration ie smtp for allowed senders/svrs, dns to specific safe dns, blocking risk 1-4 apps that we have no use for etc.
- 1 accepted solution
- 7874 Views
- 11 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Getting Started with the Strata Cloud Manager Terraform Provider in Strata Cloud Manager
- NAT policy conversion in Next-Generation Firewall Discussions
- basic network, complex problem (please help) in Next-Generation Firewall Discussions
- On-write file examination / cross-platform examination for Linux in Cortex XDR Discussions
- EDL Performance and Refresh Handling in Panorama in Next-Generation Firewall Discussions