- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Certificate Error in Global Protect Portal
- LIVEcommunity
- Discussions
- General Topics
- Re: Certificate Error in Global Protect Portal
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Certificate Error in Global Protect Portal
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-31-2012 04:11 PM
Hi All,
I'm trying to setup the Globalprotect VPN and have followed the (only partially helpful) GlobalProtect-Configuration-4.1.pdf to create certs and set everything up. When I try to connect to the portal site with my browser I get a certificate error - "Error code: sec_error_bad_signature".
It doesn't matter if I conect to the host name or the IP that I defined in the cert, I still get this error.
Does anyone know what the problem could be. Also, is there a way to actually see the certificates?
Thanks,
Kenton
- Labels:
-
Configuration
-
Set Up
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-09-2012 04:16 PM
Hi Kamish,
Thanks very much. I've been working away on this for hours before seeing you post. My last issue was the temptation to select a value for Client Certificate Profile in the Portal Config. Please also note that after I recreated all the certs and started again, I emptied my test client browser cache and purged the certs from the cert personal store.
Works nicely now with PA based CA cert.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-10-2012 01:55 PM
@kamish do you then manually copy the certificates to the browsers on the machines that need to connect to the portal?
Kenton
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-10-2012 02:25 PM
Using GlobalProtect with an external CA could be documented better I suppose. The most common mistake is that the certificate that is issued by the external CA is not imported back into PANOS together with the corresponding private key and certificate chain. Usually you'd import it as a PKCS12 file.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-10-2012 03:17 PM
@mwalter my initial problems were not with a third-party CA. I was using the PA as the CA exactly as per the instructions and it still didn't work, even after sitting down with an SE. It wasn't until we did the single cert solution as documented in this thread that we were able to get it working.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2012 09:09 PM
@jambulo: Thanks! Works for me...
I wonder if PaloAlto is willing to change the documentation if its wrong or outdated. Otherwise, we are all following the wrong documentations.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-11-2012 04:05 AM
Following these changes sorted the issue for me. Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2013 02:09 AM
Hello
I'm trying to use a certificate from our Corporate CA (Windows 2003) with GlobalConnect Gateway and Portal
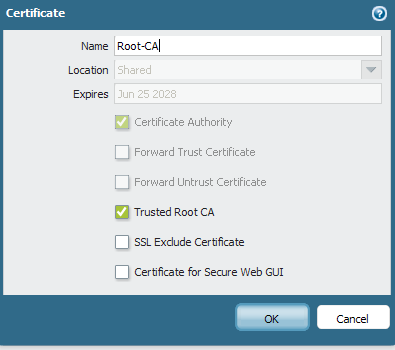
I've loaded the certificate, the private key and the root certificate. I've marked the root certifcate as Trusted Root CA.
I've configured the gateway with the server certificate, but I get this error:
What kind of certificate should I issue ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2013 06:57 AM
SistemasCajamar - Your MS PKI certificate template may not have the proper attributes set, such as client authentication, or IPSec.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-04-2013 10:53 PM
Hi Kanish,
I followed your examples for creating certificates for Global Protect.. But for some reason the portal or connecting via the Global Protect Client do not work.. The Portal just times out and client doesn't produce any errors or authentication window..
It only seems to work when l use the "web-server" local host device certificate within the Firewall.. But l don't want to use this as it is generating CN Host mismatch errors from the Global Protect Client..
We are using PAN OS " 5.0.3 and Global Protect Client 1.2.4
Thanks any help would be appreciated..
SG
- 35137 Views
- 23 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- GlobalProtect MFA with external/USB user certificate in GlobalProtect Discussions
- SAML authentication with cookies won´t work in General Topics
- Portal/Gateway certificate renewals - automation? in GlobalProtect Discussions
- Palo Alto Global Protect clients failing to connect intermittently in GlobalProtect Discussions
- GlobalProtect 6.1.11-175 Connection Issues in GlobalProtect Discussions




