- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect SCEP NDES Dynamic Challenge Failure
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect SCEP NDES Dynamic Challenge Failure
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
GlobalProtect SCEP NDES Dynamic Challenge Failure
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-10-2018 03:42 PM - edited 04-11-2018 07:44 AM
Hi,
I have been attempting to get GlobalProtect configured with SCEP for many days without success. The issue I am facing occurs when I have the SCEP Challenge set to "Dynamic" under "Certificate Management" (on the firewall), which is what I am wanting. But when using the dynamic challenge, the GP clients fail to retrieve a SCEP certificate.
The PA’s SCEP configuration and the automatic SCEP CA certificate retrieval from the root CA are working as intended.
The SCEP server appears to be fine as well. I am access and authenticate to the SCEP server using both the http(s)://<FQDN>/CertSrv/mscep_admin/ and http(s)://<FQDN>/CertSrv/mscep/ URLs via a web browser.
However, when the GP client attempts to request a SCEP cert, I see the following errors in the GP logs:
Debug(8547): GetScepCert...
Debug(8571): GetHttpResponse()...
Debug( 878): PrepareRequest...
Debug( 886): WinHttpOpenRequest...
Debug( 441): CPanHTTPSession::PostRequest: WinHttpSendRequest...
Debug( 452): bResults=1, g_dwStatus = 00000000
Debug( 673): Server gp.domain.com cert chain has been created.
Debug( 687): Server gp.domain.com cert verification passed
Debug( 711): Check server certificate revocation returns TRUE
Debug( 473): CPanHTTPSession::PostRequest: WinHttpReceiveREsponse...
Debug( 485): CPanHTTPSession::PostRequest: WinHttpQueryHeaders...
Debug(1089): m_bUserAuthentication is set to true.
(Debug( 368): Content-length: 163
Info (1099): download data success
Debug(8778): SCEP response status is error
Debug(8782): SCEP response msg is: Unable to generate client certificate
Debug(8533): GetScepCertFromPortal failed
Debug(8483): SCEP retry
I have tested using a “Fixed” password in the SCEP Configuration just to see if there was any difference in the behaviour, and the GP client was able to retrieve a SCEP certificate, so it seems there is an issue with the Dynamic password challenge. As mentioned, I am able to authenticate to the SCEP/NDES server via a web browser using both HTTP and HTTPS, and have a different enrollment challenge password generated for each request.
On the Windows server side, The IIS logs are showing that the request is being denied with a 401 error (authentication). I have attempted to implement MANY different recommendation from days of searching and testing. These include disabling UAC, checking the template/IIS application permissions, and moving NTLM authentication above Authenticate in the IIS Windows Authentication Providers list. I have even completely reinstalled and reconfigured the AD CS components, but I am still experiencing the same issue.
Below are the errors from the IIS logs:
DC01 1.1.1.1 GET /CertSrv/mscep_admin/ - 80 – 2.2.2.2 HTTP/1.1 - - dc01. domain.com 401 1 3221225581 0
DC01 1.1.1.1 GET /CertSrv/mscep_admin/ - 80 – 2.2.2.2 HTTP/1.1 - - dc01. domain.com 401 2 5 0
Below are the errors from the sslmgr.log on the PAs:
Authenticating SCEP Auth cookie in request
Error: pan_scep_get_challenge(pan_scep.c:143): Unable to get OTP from SCEP server, SCEP server might not have OTP enabled :
Error: pan_scep_get_client_cert(pan_scep.c:316): pan_mdm_get_scep_challenge() failed Unable to get OTP from SCEP server
Error: sslmgr_scep_generate_client_cert(sslmgr_scep.c:503): pan_scep_get_client_cert() failed
Error: sslmgr_scep_process_msg(sslmgr_scep.c:654): scep client cert could not be generated : Unable to get OTP from SCEP server
I’m guessing the issue has to do with the PAs attempting to pass the authentication credentials in a way that is not expected by the SCEP server. I can even see that the SCEP service account being locked out occasionally from the failed attempts. I have triple-checked the SCEP service account credentials on the PAs, but they must be correct as the PAs are able to retrieve the SCEP CA certificate using the SCEP Configuration.
I'm at a loss. Any assistance would be appreciated!
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-21-2021 11:47 AM - edited 12-21-2021 11:48 AM
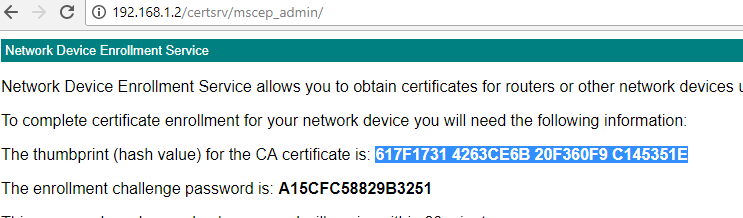
I was having the same problem, finally what did for me was Configuring the CA Certificate Fingerprint in the SCEP profile. Make sure you have the right Finger Print by accessing the CA-SERVER/certsrv/mscep_admin page and login with the configured user. It should show you the CA Certificate FingerPrint. Attaching the Screenshots for reference.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-28-2022 08:41 AM
Hello,
Which certificate did you configure as your "CA certificate" under the "SCEP Server SSL Authentication" setting?
I am experiencing the same issue here setting up SCEP for firewall SSL management access. I am able to get the SCEP server to issue me a certificate successfully using HTTP protocol, however, when I try with HTTPS I get the following error message: Unable to generate SCEP certificate, Certificate CA Retrieval Failed.
Based on the error message in bold above- I think I may be using the wrong CA certificate.
I did a TCP Dump on the management interface and I see TCP and TLS handshaking completed successfully.
Thanks for your help
- 10360 Views
- 3 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Globalprotect Client 6.2.7 disconnects multiple times in GlobalProtect Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- Assign private IP address failed in GlobalProtect Discussions
- Redirecting from 3rd party auth provider back to GlobalProtect Clientless VPN application in GlobalProtect Discussions
- GP Alert - Error code 44 - Invalid authentication cookie in GlobalProtect Discussions