- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
best way to add folders to malware whitelist
- LIVEcommunity
- Discussions
- General Topics
- best way to add folders to malware whitelist
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
best way to add folders to malware whitelist
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-27-2022 06:24 AM
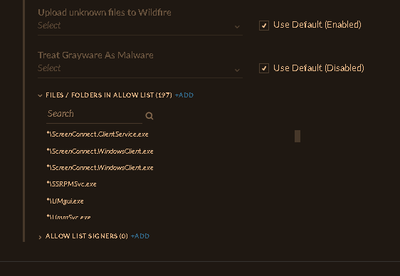
having read the document "Add a New Malware Security Profile", I am not clear as to best and properly entering a path to a folder properly.
this is a paragraph pulled out of the of the webpage.
+Add a file or folder.
Enter the path and press Enter or click the check mark when done. You can also use a wildcard to match files and folders containing a partial name. Use ? to match a single character or * to match any string of characters. To match a folder, you must terminate the path with * to match all files in the folder (for example, c:\temp\*).
My question and concerns are should all paths end with an asterisk (*)?
So this is how i am adding paths into the whitelist.
Is this correct the way or the wrong way to add this path C:\WINDOWS\SYSVOL\staging\? OR should it have an * at end.
C:\WINDOWS\System32\DNS\*.dns OR should it be *\*.dns
C:\Program Files\Microsoft SQL Server\*\Shared\SQLDumper.exe OR should it be *.\sqldumper.exe or does it not matter?
What is the appropriate way to enter files and folders into the malware list.
This C:\Users\*\AppData\Local\Microsoft\OneDrive\ OR that C:\Users\*\AppData\Local\Microsoft\OneDrive\*
This C:\WINDOWS\System32\LogFiles\ OR That C:\WINDOWS\System32\LogFiles\*
This C:\Windows\Veeam\ OR This C:\Windows\Veeam\*
*****Also, does anyone know how to copy all the files/folders in the malware list out of where it is being added into?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-27-2022 03:38 PM
Keep in mind what you're actually wildcarding.
C:\WINDOWS\System32\DNS\*.dns - This would allow anything in that fold path with a .dns extension.
*\*.dns - This would allow literally anything with a .dns extension.
C:\Program Files\Microsoft SQL Server\*\Shared\SQLDumper.exe - This allows anything within that folder path but that one wild carded portion doesn't matter. So C:\Program Files\Microsoft SQL Server\Bob\Shared\SQLDumper.exe would work fine, but C:\Program Files\Microsoft SQL Server\Billy\Bob\Shared\SQLDumper.exe would not.
*.\sqldumper.exe - Again your allowing this executable name to run from anywhere.
I'd be very careful about wildcarding entire paths and executable names outside of the specified path as required. You can't get around this completely without excluding a bunch of hashes, but any exception should be as specific as possible when being created. I absolutely refuse to exclude entire extensions or just the executable name itself, both open up pretty large exception holes in your environment.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-28-2022 05:09 AM
which paths, files dictate whitelisting?
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-28-2022 11:48 AM
So if anyone can explain this observation for me, I would appreciate it. With Cisco AMP, it has the ability to disable AV from running at the running apps by the clock. With Cortex, you have to run cytool disable service reboot . to enable the icon for cortex you do cytool enable service and reboot the computer or server. Anyone know a better way? The reason I ask this is with Cisco AMP, we had anomolies with an upgrade installation of software on 5 of our servers to where i had to goto 20 computers and disable the tray icon for Cisco AMP.
- 4527 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XDR FIM in Cortex XDR Discussions
- Local Analysis Malware and WildFire Malware Alerts in Cortex XDR Discussions
- Malware Scans in Cortex XDR Discussions
- False positive VirusTotal in VirusTotal
- After pushing content from Dev to Prod, we are seeing lot of errors in XSOAR in Cortex XSOAR Discussions