- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Gotoassist coming up as Unknown-TCP
- LIVEcommunity
- Discussions
- General Topics
- Gotoassist coming up as Unknown-TCP
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Gotoassist coming up as Unknown-TCP
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-16-2013 03:58 AM
Hi There,
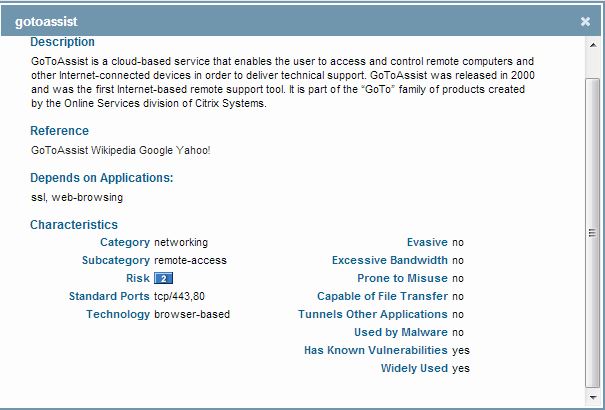
We have a user that is trying to use Gotoassist support with one of our supplier companies. I have created a specific rule that allows for Citrix, web-browsing to the specific websites it needs and gotoassist application itself. However, when it gets to the last step in the connection proccess where it comes up and says "Connecte to GoToAssist Remote Support" that is when I have an issue. Looking at the traffic logs there is a blocked connection using application "Unknown-TCP" to an IP address that shows as Citrix server when i search for it. I have tried to add that IP address to be allowed but then the next time it tries it uses a different IP address. So I added that one and then it uses a different IP address.
Anyway, my question is. Does anyone else have this issue and managed to get around it? If it is coming up as Unknown TCP and the server range is not static I am not sure how I can make a rule to allow for this without allowing a lot of other stuff being allowed I don't necessarily want to be allowed.
Can anyone help with this?
- Labels:
-
App-ID
-
Networking
-
Troubleshooting
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-16-2013 05:48 AM
You could use an FQDN address object for that server, instead of an IP address, if it keeps giving us different IP addresses to connect to. You can create an FQDN address by going under Objects-->addresses--<new address>

The PANFW will resolve the hostname to its IP address, and we should be able to connect to the server.
In addition, gotoassist requires you to have SSL too, please include SSL under the policy too. Usually an Unknown-TCP would mean that the PANFW has seen the entire TCP hanshake complete, but did not see a couple of other packets in that flow to determine the application.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-16-2013 08:16 AM
But would the FQDM work with it is the Gotoassit client trying to communicate with a server, and not a name, therefore not giving me a name to resolve?
And sorry, yes, SSL is enabled in that rule too.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-16-2013 08:45 AM
Thanks for the clarification.
What is the port number for which the traffic is getting marked as an Unknown-TCP ( I hope its not for 80 or 443 ). As mentioned earlier, we would see a traffic marked as "unknown-tcp", if the PANFW doesnt have the signature for that app. If its a different port number ( non-standard), create a custom app for the traffic on that port nunber, and use this custom app under an app override policy. When configuring the app override policy, specify the source zone and source IP as the users' IP, specify the destination zone and leave the destination address blank ( any address ), and configure the underlying protocol ( tcp/udp), the port number and the custom app created above.
You can also create/ modify the existing security policy with source IP as the user's IP, and leave the destination IP to any, and application any, and the action set to allowed, to study the IP addresses and the ports that the client uses to establish a successful connection. You can then lock this rule down to the addresses and the ports based on the traffic log analysis.
Hope that helps!
BR,
Karthik
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-16-2013 09:32 AM
I would also open a ticket so AppID team starts working on a signature update.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-16-2013 10:07 AM
You can goto Tools - Palo Alto Networks Blog and click on Submit App for Content team to develop a signature.
- 5441 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!




