- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Integrate a DMZ with virtual F5 to the PA FW
- LIVEcommunity
- Discussions
- General Topics
- Integrate a DMZ with virtual F5 to the PA FW
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Integrate a DMZ with virtual F5 to the PA FW
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2019 05:56 PM
I would like to add a virtual F5 as a proxy to our exsiting 5220 PA FW. As I have never done a DMZ to a virtual device, I am jsut wondering there a sample scenario or configuration.
If my F5 was a physical device, I will just assign an IP address to my FW interface with zone as DMZ. But if my DMZ device is virtual (setup in the datacenter in the inside network), how would I configure my FW interface?
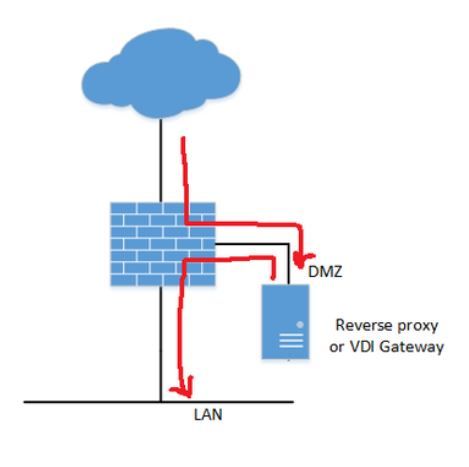
I found this picture from a thread in this community and that is what I'd like to setup, except that the DMZ is virtual. Thank you in advance for any thoughts.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-06-2019 02:45 AM
Cool, someone used my drawing....
this depends on your interpretation of a DMZ.
for me, dedicated cable and switches etc to your datacentre as the DMZ is not classed as trusted.
you may be happy with creating a new vlan through to your F5’s but this will also require a new ip interface, not sure if this can be done on a VF5 as all of ours are appliances.
there are some good network peeps on this forum so they may have better ideas or perhaps i have not fully understood your request.
is your F5 also used for internal users, this info may help others advise...
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-06-2019 07:34 AM
Thanks MickBall for the diagram. Yes my DMZ will be virtual as I only have the virtual version of the F5. The selected traffic that needs to be inspected by the F5 will be gonig from the FW to the F5, back to the FW and ti the internal network. We will be doing a lot of URL translation. That is why we need to use the virtual F5 as the proxy
I guess another way to ask this question is what is the best practice to implement a virtual DMZ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2019 12:31 AM
Could you give more info on the virtual f5 address, what else is it used for, why can it not be changes, also... do you have seperate ip interfaces for real and virtual servers on the f5 itself or just the 1 interface.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2019 07:00 AM
I guess the real question is, do you have your "DMZ" extended into your virtual environment. If so, why not just configure the F5 as if it were a physical device? I'm confused on what exactly your question is.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2019 08:14 AM
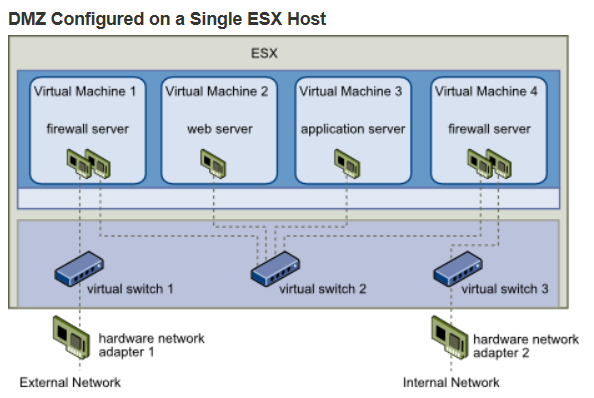
I do not have a virtual DMZ environment and I am just confused about the virtual and physical DMZ. I have not done any virtual DMZ. To me the DMZ is isolated from the intrnal network. But looking at the virtual environment which in my case sits in the datacenter in the internal network. So for the external traffic to traverse the internal network to get to the virtual DMZ seems to me that it is not a true DMZ. Even though the VLAN can isolate the traffic. I am not familiar with the VMWare ESXi so I don't know if they have their own version of secured DMZ.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2019 08:26 AM
Just remember "DMZ" is a loose term. There is no hard definition. It is more a practice of traffic segregation. I have multiple "DMZs" in my environment. Personally I don't even like the term DMZ. It's really comes from quasi dated Firewall Sandwich or DMZ on a stick designs. Once you start East-West traffic filtering, this becomes a very grey area. It's really up to you to decide how you want to segregate your traffic and what you want to call it.
I think you need to sit down, have a serious conversation with your virtualization group, discuss the implications of putting the F5 in their environment, and how you want to segregate this traffic. If there is enough of a security concern, maybe you go so far as to physically segment out a virtual environment for devices like the F5.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2019 08:32 AM
Yes. That makes sense to have a conversation with the virtual team. To me the "DMZ" should be isolated from the internal network. Thanks for all the feedbacks. Appreaciate it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2019 08:52 AM
below is perhaps one way of setting up your virtual DMZ within your data centre.
however...
you will then need to decide, based on your security requirements, how traffic will traverse your network to the untrusted interface of the ESX host.
just seen your comments regarding the virtual team. perhaps you could update when you have the answer...
Good Luck...
- 9160 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Regarding the migration from HDD to SSD for PA-VM running in the Azure environment in Next-Generation Firewall Discussions
- Regarding the migration from HDD to SSD for PA-VM running in the Azure environment in VM-Series in the Public Cloud
- Jira integration errors in Cortex XDR Discussions
- Ideal for Integrate Line Message API from XSOAR in Cortex XSOAR Discussions
- Request for SD-WAN Deployment Documentation in Azure in Advanced SD-WAN for NGFW Discussions