- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Internet facing interface dhcp-client inbound NAT
- LIVEcommunity
- Discussions
- General Topics
- Re: Internet facing interface dhcp-client inbound NAT
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-06-2013 10:12 AM
So,
PAN 5.0.1
eth1/1 - Layer 3 / Internal network 10.0.0.1/24
eth1/2 - Layer 3 / External network - DHCP assigned IP adress from ISP.
Outbound NAT works. Inbound NAT i simply doesnt get to work.. ![]()
Used the cli command test nat-policy-match from Untrust source 8.8.8.8 destination [assigned ip adress of eth 1/2] destination port 3389 protocol 6
Got rule matched on that..
Followed that up with
debug dataplane packet-diag set filter match destination [ip adress of etch1/2]
debug dataplane packet-diag set filter on
debug dataplane packet-diag set log feature flow basic
debug dataplane packet-diag clear log log
debug dataplane packet-diag set log on
Then several:
tail mp-log pan_packet_diag.log
Nothing in that log ![]()
End result wanted.. Traffic going to DHCP assigned IP is NAT:ed into internal network. Ie. Satelite office ISP's gives us dhcp issued adresses / or one static / I want to host services such as rdp / ssh etc etc. IPSEC is not an option in this scenario.
Ideas for sollution? Is it even possible???
BR, Christian
- Labels:
-
Configuration
-
Networking
-
Troubleshooting
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-07-2013 01:19 AM
I think your destination address in the security policy is wrong. Destination address should be based on the pre nat address(External DCHP address), while the desination zone should be the post nat zone(LAN).
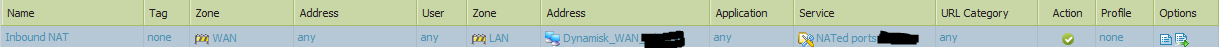
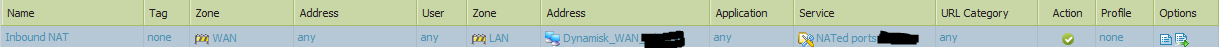
My rule looks like this:
The reason you don't get any logs is probably because PA doesn't log traffic that is blocked by the default policy. You can temporarily log this with a CLI command ()
I don't think there is any way to automatically get the DHCP assigned address in an object, but a workaround is using a dyn-dns service and use your fqdn in the security/nat policy. ()
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-07-2013 12:25 AM
It should be possible. I have the same setup on my PA-200 at home, and inbound NAT working without any problems.
Is your security policy allowing the NATed traffic? What does your nat policy and matching security policy look like?
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-07-2013 12:53 AM
I thought it would..
SO I have,
Sec pol:
src - Untrust - any -any - any dst - Unstrust - any - (Application) ms-rdp - services (any) - allow - options log
Also have:
src - Untrust - any -any - any dst - Trust- internal.server.object- (Application) ms-rdp - services (any) - allow - options log
Also tried - Chaging Application to ANY and services to the same I used in the NAT rule. service-ms-rdp...
NAT policy:
src zone: Untrust dst: zone Untrust: any - any - dest adress: External DHCP interface Service: (Created service-ms-rdp 3389) - dest translation: internal.server.object
The sad part is - I don't see anything in the logs... ![]() And nothing in the debug flow either... How would you go about troubleshoot it?
And nothing in the debug flow either... How would you go about troubleshoot it?
And, Is there an object with the "DHCP-assigned.address" that one can use instead of the one I made that will not update if the DHCP client gets an new address... ![]()
Br, Christian
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-07-2013 01:19 AM
I think your destination address in the security policy is wrong. Destination address should be based on the pre nat address(External DCHP address), while the desination zone should be the post nat zone(LAN).
My rule looks like this:
The reason you don't get any logs is probably because PA doesn't log traffic that is blocked by the default policy. You can temporarily log this with a CLI command ()
I don't think there is any way to automatically get the DHCP assigned address in an object, but a workaround is using a dyn-dns service and use your fqdn in the security/nat policy. ()
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-07-2013 02:05 AM
Damn thats the change I needed to make... I read the advanced NAT PDF and I got the impression that It first nats THEN check policies... Obviously, this is NOT the case ![]()
SO by adding the external IP to the ruleset - BAM, it started working right of the bat... ![]()
I soo searched for DHCP on this site and NAT.. And did not get it to work ![]() But with your great help.. It-s working like a charm.. SO The zone reflect the NATted actions, but the IP does not. Not that obvious imho... And not like any other FW i've worked. with... Juniper, Checkpoint, Clavister.....
But with your great help.. It-s working like a charm.. SO The zone reflect the NATted actions, but the IP does not. Not that obvious imho... And not like any other FW i've worked. with... Juniper, Checkpoint, Clavister..... ![]() So, one more thing to get used to
So, one more thing to get used to ![]()
Again, THANKS!!! Much appreciated !!!
/C
- 1 accepted solution
- 5081 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PAC File for Prisma Access China in Prisma Access Discussions
- Is the unified RPC interface (MonitorDirect.enqueueLogRequest) supported for external use? in Next-Generation Firewall Discussions
- Palo Windows ARP Issue - Windows Hosts Not Installing ARP info in Next-Generation Firewall Discussions
- Existing traffic stops suddenly, and changing of interface MTU resolved it. in General Topics
- Beginner Question Understanding Basic NAT and Traffic Flow in Palo Alto Firewall in General Topics




