- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Issue with WLC Radius request to NPS Server
- LIVEcommunity
- Discussions
- General Topics
- Issue with WLC Radius request to NPS Server
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Issue with WLC Radius request to NPS Server
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 04:44 AM
Hi all,
I have an issue with the radius request through the firewall,
The radius request come from an cisco 1852-ME WLC and goes to an Windows 2016 NPS Server, both in different zones.
An simular setup with an firewall works fine.
The NPS Server does not react on the requests. With Wireshark I can see the request and Answer from the NPS.
I suspect that the Certificate (used for auth) have changed at the firewall.
AFAIK certificate inspection is disabled (where I can check this?)
Does somebody else has an simular setup? What do I have to check for?
As I'm new on Palo, I could have missed something here.
Thanks for your feedback
Willem
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 05:12 AM
Hi @willem.degroot ,
you can see which TLS Interception Policy is defined by looking at Policy > Decryption Policy.
If there is a policy which does SSL Forward Proxy (MitM), then certificates are exchanged.
But: Radius runs with UDP, so there is no TLS support - I guess the problem is somewhere else.
Do you see the request in the NPS log?
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 05:24 AM
Hi Willem
Unless your implementation uses radius over ssl, the certificates should not be touched by the firewall
ssl decryption policies can be found under the policies tab
you can set up packetcapture on the firewall as well and set it so you capture ingres and egress, that way you can compare what goes into and what comes out
you can match your captures to global counters, to verify if anything additional of interest pops up:
https://paloaltonetworks.my.salesforce.com/kA10g000000ClTJ?srPos=0&srKp=ka1&lang=en_US
i'd probably look at NAT, routing and possibly timestamps on the radius/certificates
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 06:03 AM
Hi Chacko42
Thanks for your reply. I agree on the UDP traffic.
In the Eventviewer there is no message BUT in the file found here C:\Windows\System32\LogFiles There are messages like:
"EEMDC10","IAS",02/22/2019,14:44:01,1,"host/CHW7X576.sscgr.contoso.com","sscgr.contoso.com/chgr/zgi/Group_IT/resources/CHW7X576","b0-8b-cf-dc-e8-c0:V2ZDEWBC","88-b1-11-80-a8-b8",,,"CHGR-PAF-Office","172.16.129.20",1,0,"172.16.129.20","Test-AP-CHGR",,,19,,,2,5,"WLAN Office",0,"311 1 172.29.24.10 02/22/2019 10:25:00 514",,,,,,,,,"5c6fee90/88:b1:11:80:a8:b8/30",,,,,,,,,,,,,,,,,,,,,,,,,"Use Windows authentication for all users",1,,,, "EEMDC10","IAS",02/22/2019,14:44:01,11,,"sscgr.contoso.com/chgr/zgi/Group_IT/resources/CHW7X576",,,,,,,,0,"172.16.129.20","Test-AP-CHGR",,,,,,,5,"WLAN Office",0,"311 1 172.29.24.10 02/22/2019 10:25:00 514",30,,,,,,,,"5c6fee90/88:b1:11:80:a8:b8/30",,,,,,,,,,,,,,,,,,,,,,,,,"Use Windows authentication for all users",1,,,,
I can also do a test from the WLC to the NPS with user credentials, this is working fine.
I'll keep on trying 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 06:07 AM
Hi Reaper,
I will try the packet capture, to see what happens.
NAT and routing can be ignored.
Both ZONEs are internals without NAT
An test from the WLC to the NPS with user-credentials will be answered correct.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 07:25 AM
Hi Reaper,
I just could sniff and found an interesting difference between Firewall RX and TX.
Besides that I have duplicates in the trace, I see the following:
on the outgoing interface, there are packages missing, packages that are on the incomming interface with MTU of 1514, are not sendout the outgoing interface anymore.
Where do I have to check the Firewall settigns for this?
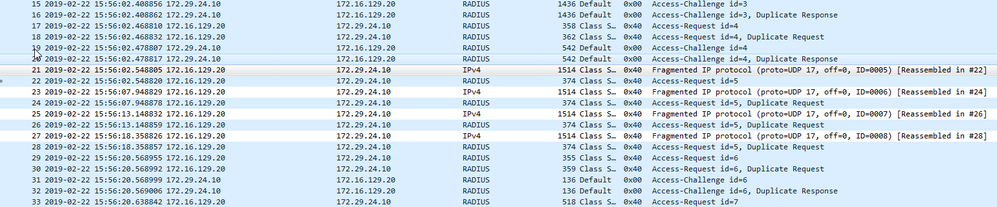
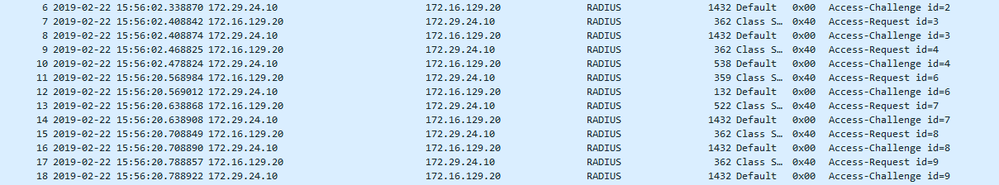
Incomming:
Outgoing, note that request/response ID 5 is missing.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 07:32 AM
Are all your interfaces set to "normal" MTU? It may be worth looking into enabling jumbo frames and increasing the mtu on internal interfaces
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-22-2019 08:41 AM
After changing the radius configuration to use certificate based authentication - do you see eventlogs with the mmc > event manager? I assume it's a config thing on the nps server - there should be event ids for the requests - if there aren't, it has to do something with the network/firewall
Chacko
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2019 02:29 AM
Hi Reaper,
I increased the MTU on the (sub) Interfaces but without an positiv result.
I don't think that this will solve the issue anyway because I see in the Capture that the packet is Fragmented ( I try to capture nearer to the source.
What I have found is an Issue ID PAN-93609 but I do not have the right (yet) to access the reports.
May this be the issue?
I'm running PAN-OS 8.0.4
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-25-2019 04:18 AM - edited 02-25-2019 04:19 AM
PAN-93609 is when an initial packet arrives that is fragmented it could be dropped, usually but not limited to udp (this was fixed in 8.0.11)
it might be worth looking into upgrading
the currently recommended release in your code train is 8.0.15
PANgurus - Strata & Prisma Access specialist
- 7774 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect Internal Detection in GlobalProtect Discussions
- Assistance with LDAP Authentication in General Topics
- Error when calling “Get number of users at location(s)” API in Prisma SASE Aggregate Monitoring APIs in Prisma Access Discussions
- Why do the same Windows Server data collected using XDRC and WEC agents show different statuses in the following fields? in Cortex XSIAM Discussions
- Request for VPN Capability Enhancement on Palo Alto Networks Firewalls in Next-Generation Firewall Discussions