- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Post 7.0x upgrade intermittend SSL traffic hangs when being decrypted
- LIVEcommunity
- Discussions
- General Topics
- Re: Post 7.0x upgrade intermittend SSL traffic hangs when being decrypted
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Post 7.0x upgrade intermittend SSL traffic hangs when being decrypted
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-18-2015 12:19 PM
Hi
We have noticed this with two customers and on our own PA's , all of these are PA3020's in a HA a/s setup
SSL decrypted outbound traffic hangs intermittently for a few minutes and then it starts to pass through again.
This happens both with 7.0.1 and 7.0.2
anyone seen this issue as well ?
kinda hard to work with support on this since it's intermittent
regards
Gudmundur
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-13-2015 06:46 AM
starting asking your SE to putinternal pressure on this; I fear the admins aren't alerting the right internal Palo folks on the importance of this
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-13-2015 09:06 AM
Fortunately we didn't upgrade to 7.X on any of our firewalls (thanks to the community's responses on how much it sucks)...ok it doesn't suck but it's been riddled with problems.
To me it seems this issue has been big enough that an off-cycle patch should have done and Palo should have spent engineering time 24x7 until these issues had been fixed. The cost of support 6-figures+ to have this large of a problem with a "wait for our patch cycle" mentality blows my mind.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-13-2015 10:20 AM
I asked for an update on my ticket and received the following back. I'd like to see the fix sooner, but it is what it is I guess.
Working with the engineering team I have been able to confirm the root cause of the issue is the result of Bug 85091. The resolution for this issue is currently scheduled for release in the 6.1.8 and 7.0.4 software update.
The new software versions are expected to be released the Week of November 16, 2015 for 6.1.8 and the Week of December 7, 2015 for 7.0.4.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-13-2015 12:05 PM
I wonder how big a problem has to be before they patch it out of the normal release cycle?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2015 05:12 AM
Is anybody running 6.1.x having this problem? I hadn't heard of it occuring in the 6.x line until the PA response stating it'll be fixed in 6.1.8. I'm concerned that once again they've missed the root cause.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2015 05:15 AM
I found that weird as well. I was running 6.1.7 with no issues until I upgraded to 7.0.3. At least I was not aware of any issues... maybe it's more pronounced in 7.0.x??
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-17-2015 01:08 AM
Hi all- I’m Nathan, with Support Management at Palo Alto Networks. As was posted earlier, we’re sorry for frustration caused by this issue. The support response details posted above are correct. 6.1.8 is planned for release later this week (16-Nov) and 7.04 will be available during the week of 21-Dec (please note the date, as it is different than what was posted earlier). Both of these releases resolve this issue.
There may be additional options available, but support would prefer to discuss these individually to ensure they meet your individual needs and timeliness. I’ve reached out to some of the members on this discussion via phone/email to provide some options related to this issue. While we recommend upgrading when the releases become available, there may also be a workaround option for those that require an immediate fix. The workaround has been tested by our QA group, which is why we would like to have a live debug session for those that are having trouble implementing the workaround. For those I’ve contacted that need to pursue this path, please get back to me and I will make sure you get help from Support to discuss all options.
Note: if there are others experiencing this issue who have not created a support case, please contact Palo Alto Networks support (https://www.paloaltonetworks.com/company/contact-us.html). We’re happy to help get this resolved for you.
Thanks,
Nathan
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2015 10:49 AM
What is the workaround? Have a call open, but maybe the community is faster.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2015 10:52 AM
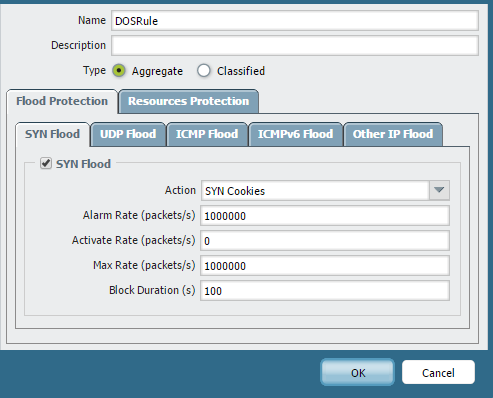
There really isn't (from what I've been told and discovered after implementing the work-around). They're recommending people configure some DoS rules against SSL. This will extend the interval between the issue happening and traffic halting but not fix it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2015 10:53 AM
Yes, it hasn't fixed the problem for me, but it's made the freezes much less often to several pay day rather than every 45 minutes as I was seeing prior. I've been able to turn decryption back on, and my users are dealing with the pain right now.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2015 10:56 AM
This is what they did for me.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2015 10:59 AM
Thanks Guys, will try the DOS rule.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2015 11:02 AM
For reference here's the work-around I was provided:
set profiles dos-protection profiledos type aggregate flood tcp-syn enable yes syn-cookies activate-rate 0 alarm-rate 1000000 maximal-rate 1000000 block duration 100
set rulebase dos rules dosrule2 service service-https source 192.168.1.10 destination 1.1.1.2 action protect
set rulebase dos rules dosrule2 from zone L3-Trust
set rulebase dos rules dosrule2 to zone L3-Untrust
set rulebase dos rules dosrule2 protection aggregate profile profiledos
Everybody running into this problem should still open a case though to show how many people are being affected.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-07-2015 11:18 AM
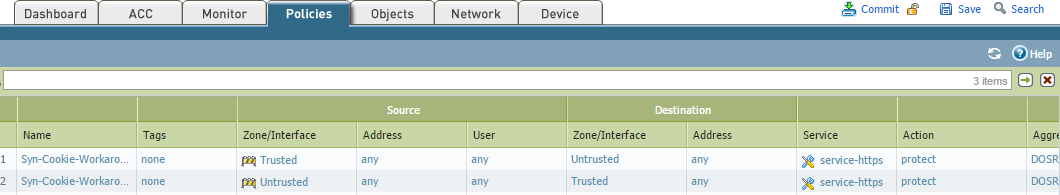
They had me create a reverse rule as well. I did mine based on zones rather than networks IP
trusted ---> untrusted
untrusted ---> trusted
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-15-2015 05:37 AM
Can anyone who has updated to 6.1.8 verify if the issue has been resolved by the update? Support claims the issue is resolved in both 6.1.8 and 7.0.4 so hopefully if it's resolved in 6.1.8 we can assume it will also be resolved in the upcoming 7.0.4 release.
We're wanting to roll out 7.0.4 shortly after the release but only if we can verify the issue is resolved.
- 30561 Views
- 59 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Not able to log XFF (Actual Client IP) in PaloAlto Logs even when we enable XFF and URL filtering profile in Palo's in Next-Generation Firewall Discussions
- Where to find information about SSL decryption is (not) required to identified traffic in General Topics
- Question regarding Signal messaging application in General Topics
- SSL Forward Proxy - Exclude certain IPs from decryption in VM-Series in the Public Cloud
- Issues with decryption on versions higher than 10.2.8-x, TAC no help in General Topics