- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
PPPOE interface - dynamic IP - GP Portal
- LIVEcommunity
- Discussions
- General Topics
- PPPOE interface - dynamic IP - GP Portal
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
PPPOE interface - dynamic IP - GP Portal
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-17-2019 05:03 PM
When establishing a connection via PPPOE there is no possibility to select the IP ("None") assigned by ISP in the Global Protect portal configuration, only the interface, which is not sufficient for it to work. I would expect that the IP assigned by ISP is created as an dynamic address object.
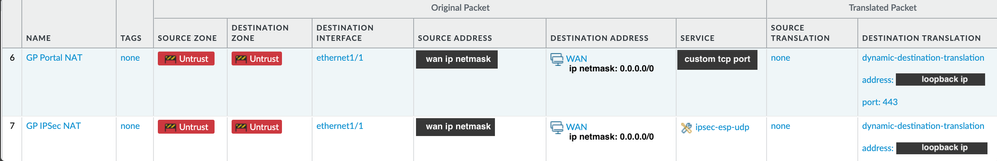
To make GP work with portal & gateway, I had to create a loopback, then doing a NAT from the pppoe interface's (in my case eth1/1) ip:some other port not being 443 to the loopback:443. I had to create an additional address object where I manually had to put in the dynamic ip. I now have to amend this address object manually every time the interface ip changes. Am I missing something here or is it really this cumbersome using PPPOE?
It seems PAN is not that much interested in supporting PPPOE connections- besides this, there is also lack of vlan tagging support once the L3 interface has been set to PPPOE which many ISPs require and no option for a scheduled reconnection.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2019 12:43 AM
Hi
This should be work with 'None' in IP address field.
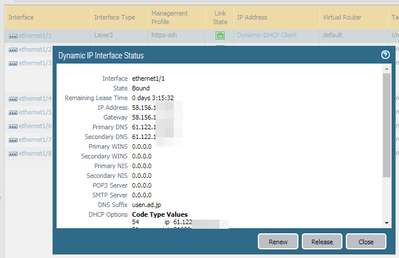
Here is my testbed (sorry, mine is dhcp client - not pppoe)
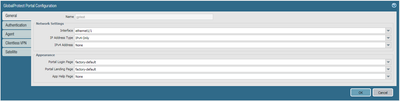
With above interface, if I configure GP as below...
The device recognizes IP address which retrieved from ISP.
admin@PA-220> debug ssl-vpn global-protect-portal
portal : gptest
portal address IPv4 : 58.156.1xx.xxx
admin@PA-220> debug ssl-vpn global-protect-gateway
gateway : gptest
gateway address (IPv4 Only) : 58.156.1xx.xxx
admin@PA-220>
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2019 01:37 AM
thanks!
can you select your ip where none is listed in GP portal configuration?
I have the assumption pppoe differs from dhcp
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-20-2019 04:21 PM
No, if IP address grabed dynamically, it is not shown on the list.
(as I mentioned above, it works with 'None')
By the way, if you configure static-ip under pppoe setting, it shows IP address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-11-2022 12:52 PM
Hi community,
after having spent two whole days on the topic of getting the GP-gateway up and running to connect via androids native ipsec client on a PPPoE interface with dynamically assigned IP...I gave up... and can confirm:
1.) 'cumbersome' is an euphemism
2.) the 'solution' presented herein does not work for scenarios with dynamically assigned IP via PPPoE
3.) selecting 'none' IP in GP-gatway config will not work in this scenario -> the paloalto PA220 (SW Ver. 10.1.4) will not respond to IKE traffic on the PPPoE interface (captured via a transparent linux bridge on respective WAN uplink)
4.) I also tried Pan219s trick with NATting the ipsec traffic to a loopback interface with a static IP on which the GP-portal would reside with the modification of using the FQDN destination object of my WANs DDNS address in my NAT-rules' 'original packet' section. Here I had the problem that the FQDN object was not reliably translated and suddenly reported that it had 'no value assigned'.
After all I share the impression that paloalto really does not pay too much attention to these SOHO scenarios, i.e. the lack of VLAN support, the DDNS implementation (had to use a linux box behind the palo to update my DDNS provider with firewalls external address) and now the non-functional GP-portal.
I don't want to put another router in front of the palo just to get the GP-portal up and running.
How are chances to get above functionalities implemented/fixed? Or anybody around with some virtuos workaround?
Any help would be highly appreciated.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2022 12:06 PM - edited 01-18-2022 12:08 PM
Hi Supergonzo,
after some fiddling and trial an error I found the solution. Initially I also tried the fqdn workaround you mentioned above, also no success. The breakthrough: Instead of using an address object limited to the assigned WAN IP I have created an address object with the ip range 0.0.0.0/0 which is used in any rules (NAT as well as Security Policy).
That's the only change I have made to the original setup. Lo and behold, this configuration works flawlessly since 2 years.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2022 12:43 PM
Hi Pan219,
tried the setup you mentioned above with the 0.0.0.0/0 object this evening but to no avail. When trying to commit my nat ruleset it throws following error as host portion of original address differs from translated when nat-ting from "0.0.0.0/0" to "loopback-ip/32":
Error: nat rule 'inbound_ipsec_to_untrust_interface': Mismatch of destination address translation range between original address and translated address
Can you plz post a screenshot of your nat rule?
Thx in advance!
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2022 01:32 AM - edited 01-25-2022 02:01 AM
some more clarification:
- I have limited the source address: x.x.x.x/x
- the loopback ip is an address object in the format x.x.x.x without the /32
- gateway and portal sitting on the loopback interface
- in gateway configuration - agents - tunnel settings: tunnel mode and ipsec is enabled
- 14430 Views
- 7 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Address Group and Tag limitations in General Topics
- PA-415-5G not working with fresh T-Mobile SIM in General Topics
- Unable to reach Palo Alto - Global Protect Portal. in GlobalProtect Discussions
- Newsletter: Cloud Delivered Security Services, Oct-2025 in Advanced Threat Prevention Discussions
- GlobalProtect Gateway on PA-820 Stopped Responding – Guidance Needed in GlobalProtect Discussions