- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Source NAT on a IPSec VPN tunnel due to overlapping IP space.
- LIVEcommunity
- Discussions
- General Topics
- Source NAT on a IPSec VPN tunnel due to overlapping IP space.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2020 12:41 AM
Folks,
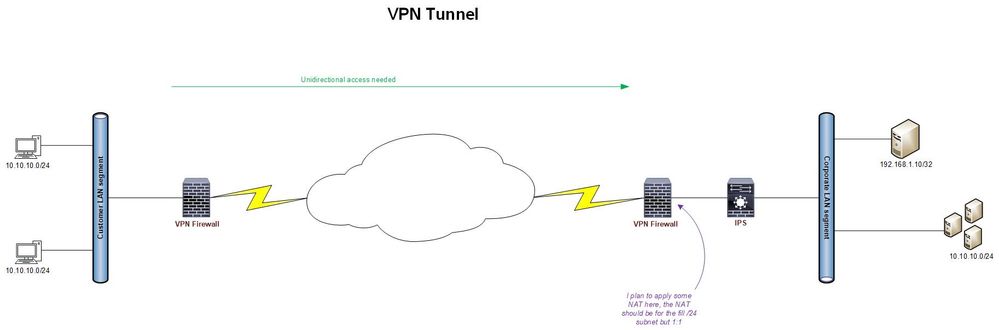
Our team has been tasked to work on a VPN tunnel from a customer premises to our corporate DC.
The access would be unidirectional with the Customer accessing on-prem resources.
The first challenge is that we have overlapping IP addresses at the customers end.
Our team wants to use some NAT policies which will act like a 1:1 policy. i.e. we want to avoid a interface based NAT.
There should be some way of identifying the IP address individually on the IPS behind the VPN Palo Alto firewall.
Any suggestions?
Thanks!!
N.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2020 11:14 AM - edited 06-16-2020 11:19 AM
I would think you could do with a Dynamic IP NAT to achieve the 1:1 NAT you're wanting (see https://docs.paloaltonetworks.com/pan-os/9-0/pan-os-admin/networking/nat/source-nat-and-destination-... ). However, I think if you're doing this on the corporate side, you're going to have a problem with conflicting routes (10.10.10.0/24 is both down the tunnel, and on the LAN). If you could do this at the customer side before it crosses the tunnel, that might be better.
EDIT: Actually, the more I think about it, that's going to cause the same problem on the other side then. Maybe you'll have to NAT both directions with two different pools that don't conflict with the 10.10.10.0/24 address. Maybe you translate 10.10.11.0/24 to 10.10.10.0/24 on the corp side, and you translate 10.10.12.0/24 to 10.10.10.0/24 on the client side or something like that.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-16-2020 11:14 AM - edited 06-16-2020 11:19 AM
I would think you could do with a Dynamic IP NAT to achieve the 1:1 NAT you're wanting (see https://docs.paloaltonetworks.com/pan-os/9-0/pan-os-admin/networking/nat/source-nat-and-destination-... ). However, I think if you're doing this on the corporate side, you're going to have a problem with conflicting routes (10.10.10.0/24 is both down the tunnel, and on the LAN). If you could do this at the customer side before it crosses the tunnel, that might be better.
EDIT: Actually, the more I think about it, that's going to cause the same problem on the other side then. Maybe you'll have to NAT both directions with two different pools that don't conflict with the 10.10.10.0/24 address. Maybe you translate 10.10.11.0/24 to 10.10.10.0/24 on the corp side, and you translate 10.10.12.0/24 to 10.10.10.0/24 on the client side or something like that.
- 1 accepted solution
- 9789 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto Site to Site VPN ipsec tunnel up but unable to ping Source to destination in Next-Generation Firewall Discussions
- [SOLVED] GPUDATE /FORCE DOESN'T WORK WITH GLOBAL PROTECT in GlobalProtect Discussions
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- Geo blocking after GP login in GlobalProtect Discussions