- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
vm palo question on interfaces for esxi
- LIVEcommunity
- Discussions
- General Topics
- Re: vm palo question on interfaces for esxi
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
vm palo question on interfaces for esxi
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-26-2021 01:20 PM - edited 11-30-2021 06:40 AM
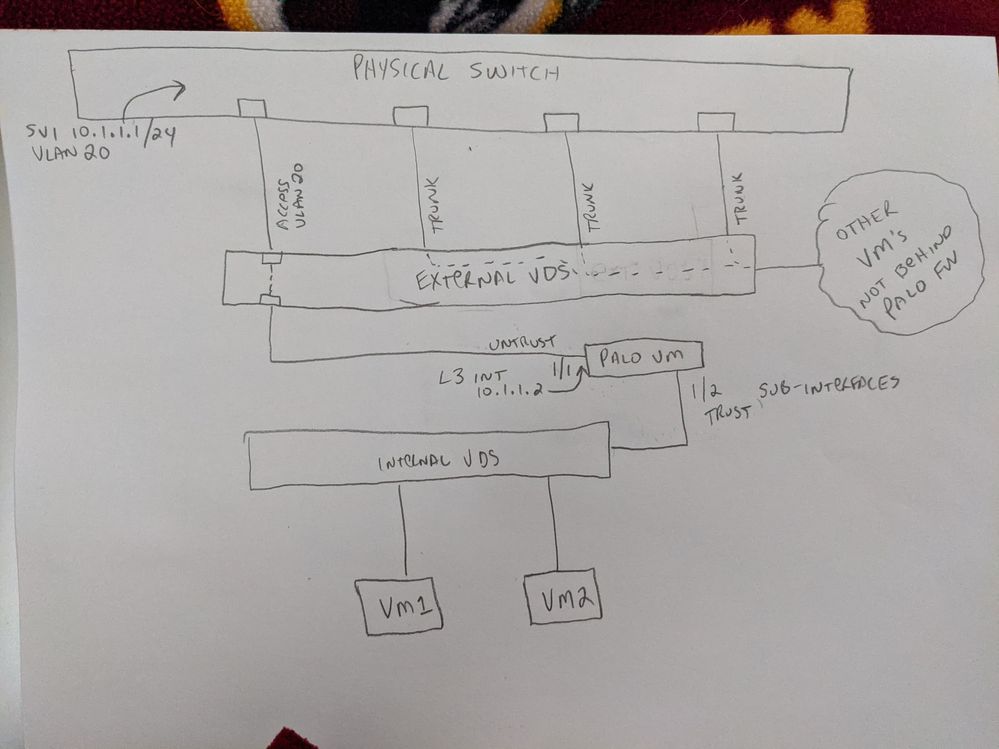
We have an exisiting vmware esxi environment that has 3 hosts with distributed switches configured.
Currently, each esxi host has 4 links (all trunks) going to the physical uplink switch.
We've installed a VM palo series firewall and have established managment connectivity to it via eth1/0 with no issues.
Now we are configuring sub interfaces on the vm palo and will point the vm's to it as their gateways. I think this part is working.
Where our issue is happening is on the uplink from the vm palo to the physical switch. I'm confused how this works as all the uplinks are trunks and I need to have the connection from the physical switch to the palo vm as a L3 link.
Could someone break this down for me? Does the questione even make sense?
More info
I have a SVI on the physical Cisco switch. 10.1.1.1/24
I configured eth1/1 on the vm palo as a L3 link as 10.1.1.2/24
I have sub interfaces 10.1.80.1/24 (vlan 80) and 10.1.90.1/24 (vlan90) created off of eth1/2 of the VM Palo and they will be gateways for the virtual machines.
The palo virtual router is set with a default router of 10.1.1.1 to the physical switch.
Honestly without any routing, I would think that I should be able to ping from the physical switch to the 10.1.1.2 as it should be directly connected but that's not working even with the management profile applied.
So confused!
Thanks in advance!!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2021 06:35 AM - edited 11-30-2021 06:36 AM
Hi @geewiss ,
I will ask you to verify below points.
1. Make sure the proper VLAN mapping (VLAN for subnet 10.1.1.0/24) is done on esxi side for the Palo Alto VM eth1/1 nic. If its not then you need to fix it.
2. Also you need to make sure VLAN for subnet 10.1.1.0/24 is flowed till the esxi. You need to verify your esxi physical connectivity and check if VLAN for subnet 10.1.1.0/24 is available.
Also in the attached diagram, I see you have configured VLAN20 for the palo alto eth1/1 but as per information given, VLAN 20 belongs to 10.1.20.1/24. So in this case, subnet 10.1.1.0/24 should have different vlan id. You need to verify this.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2021 06:44 AM
1. Proper vlan maping is done on the esxi side. I think i'm good there.
2. Vlan is flowed till the esxi. Should be good there.
I fixed the original post. Vlan 20 is only on the physical switch to the external vds. Vlan 80,90 are on the interal vds with different id's.
I guess my real question is .....will the physical links work like this were I have access port and trunk ports terminated to the physical from the external vds?
Thanks for your help and clarification!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2021 08:34 PM
License shouldn’t be the issue here.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2021 06:21 AM
Hi @geewiss ,
If any of the palo alto interface is configured as a L3 sub-interface, then you need to configure neighboring device interface as a trunk then you can flow specific vlan traffic via that trunk port. If Palo Alto interface is configured as normal L3 interface then keeping neighboring device interface in access port should work.
Check out my YouTube channel - https://www.youtube.com/@NetworkTalks
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-02-2021 01:40 PM
UPDATE
The key here was to make all 4 physical links from the ESXi host to the physical switch as trunks. Then to have the e1/1 interface on the palo configured in a port group that is "vlan trunking". Then to have a sub interface on the palo with tagging the vlan number. This seem to work.
- 7169 Views
- 8 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Question on "default" VLAN Interface in Next-Generation Firewall Discussions
- Unable to reach Palo Alto - Global Protect Portal. in GlobalProtect Discussions
- PALO ALTO FIREWALL , lan interface internet issue in Next-Generation Firewall Discussions
- SCM Essentials - No interfaces in Routing and Zones in Strata Cloud Manager
- PANW aws vm-series ipsec tunnel ip /30 Tunnel interface in VM-Series in the Public Cloud