- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Issue | "Nist NVD" Integration is not working
- LIVEcommunity
- Tools
- Integration Resources
- Integration Discussions
- Issue | "Nist NVD" Integration is not working
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Issue | "Nist NVD" Integration is not working
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2021 03:12 AM
Hi,
We have an issue with "Nist NVD" integration.
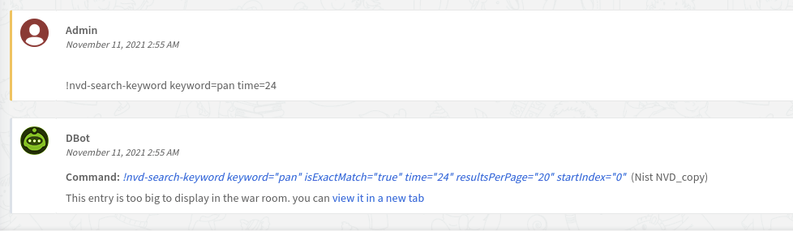
When I click the command "!Nvd-search-keyword" we are getting the following message:
"{" message ":" Both modStartDate and modEndDate are required when either is present. "}"
The integration was published by: "Murat Ozfidan" and supported by "Community".
Does anyone have an issue and can help?
Thanks,
Elad
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2021 05:58 AM
I found the cause of this error:
NVD has implemented API_Key. Until I upgrade integration you have to follow the limits or you can copy integration and change code, add api_key value to connection method.
Code:
def connection(url, additional_parameters):
headers = {'Accept': 'application/json'}
#add "+ '&apiKey=' + YOUR_API_KEY" following row
endpoint = url + additional_parameters + '&apiKey=' + YOUR_API_KEY
req = requests.get(endpoint, headers=headers, verify=VERIFY_SSL)
if req.status_code != 200:
return_results(req.content)
sys.exit(1)
else:
return req.json()
source: https://nvd.nist.gov/general/news/API-Key-Announcement
Best practices for using the NVD API:
The best practice for making requests within either rate limit is to use the modified date parameters. No more than once every two hours, automated requests should include a range where modStartDate equals the time of the last response received and modEndDate equals the current time. Enterprise scale development should enforce this approach through a single requestor to ensure all users are in sync and have the latest CVE and CPE information. It is also recommended that users "sleep" their scripts for six seconds between requests.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-08-2021 02:40 AM
Hi MOzfidan,
Thanks for the help.
I added the code to the integration but I still get the error:
"{"message": "Both modStartDate and modEndDate are required when either is present."}"
Please advise.
Thanks,
Elad
- Mark as New
- Subscribe to RSS Feed
- Permalink
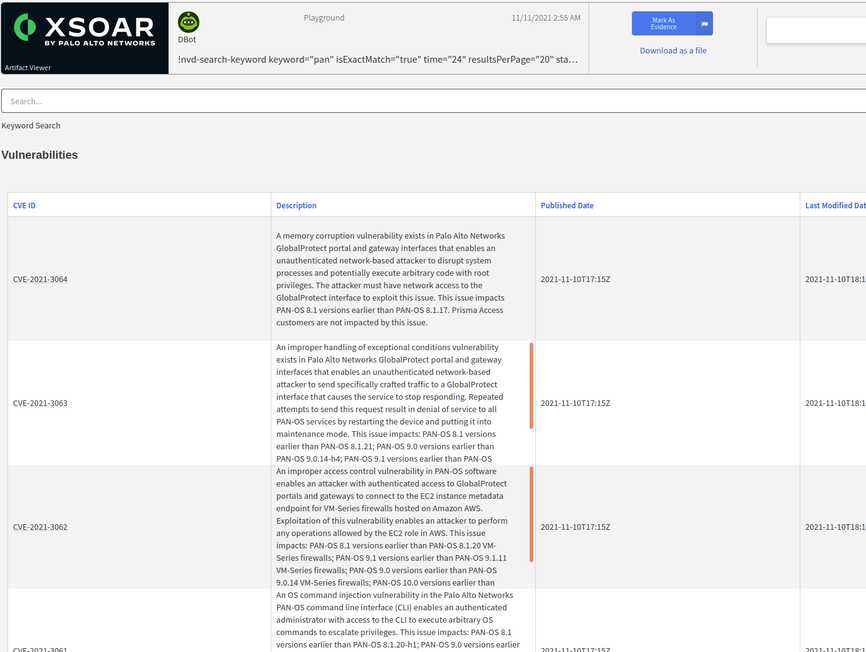
11-11-2021 03:06 AM
Hi Elad,
I resolved this issue.
I made a few changes in keyword_search function.
Finally, The yaml file is attached.
def keywordSearch():
base_url = urljoin(demisto.params()['url'], '/rest/json/cves/1.0')
keyword = demisto.args().get('keyword')
isExactMatch = demisto.args().get('isExactMatch')
time = int(demisto.args().get('time'))
last_time = datetime.today() - timedelta(hours=int(time))
start_date = last_time.strftime('%Y-%m-%dT%H:%M:%S:000')
modEndDate_date = datetime.today()
modEndDate= modEndDate_date.strftime('%Y-%m-%dT%H:%M:%S:000')
startIndex = demisto.args().get('startIndex')
resultsPerPage = demisto.args().get('resultsPerPage')
additional_parameters = '?modStartDate=' + start_date + ' UTC-00:00' + '&modEndDate=' + modEndDate + ' UTC-00:00' + '&keyword=' + keyword + \
'&isExactMatch=' + isExactMatch + '&startIndex=' + str(startIndex) + '&resultsPerPage=' + str(resultsPerPage)
generalSearchRequest = connection(base_url, additional_parameters)
generalVulnerabilityList = extractVulnDetails(generalSearchRequest)
headers = ['CVE ID', 'Description', 'Published Date', 'Last Modified Date', 'References']
markdown = 'Keyword Search\n'
markdown += tableToMarkdown('Vulnerabilities', generalVulnerabilityList, headers=headers, removeNull=True)
results = CommandResults(
readable_output=markdown,
outputs_prefix='NistNVD.KeywordSearch',
outputs_key_field='CVE ID',
outputs=generalVulnerabilityList
)
return_results(results)
- 7201 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Does anyone have information on how to integrate Hillston brand Firewalls into XSIAMAmazon in Integration Discussions
- Microsoft Sentinel Incident custom details fetch in XSOAR in Integration Discussions
- Modifying Checkpoint FW Access Rule from Cortex XSOAR in Integration Discussions
- Aruba ClearPass integration dynamic group issue in Integration Discussions
- Cortex XSOAR integration vs XSIAM integrations in Integration Discussions