
- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Palo Alto Networks announces the VM-Series Virtual Next-Generation Firewall can now integrate with Amazon Virtual Private Cloud Ingress Routing. Got questions? Get answers on LIVEcommunity!
We are excited to announce that the Palo Alto Networks VM-Series Virtual Next-Generation Firewall now integrates with the new Amazon Virtual Private Cloud (Amazon VPC) Ingress Routing feature to more efficiently protect your applications and data from inbound threats coming from the internet.
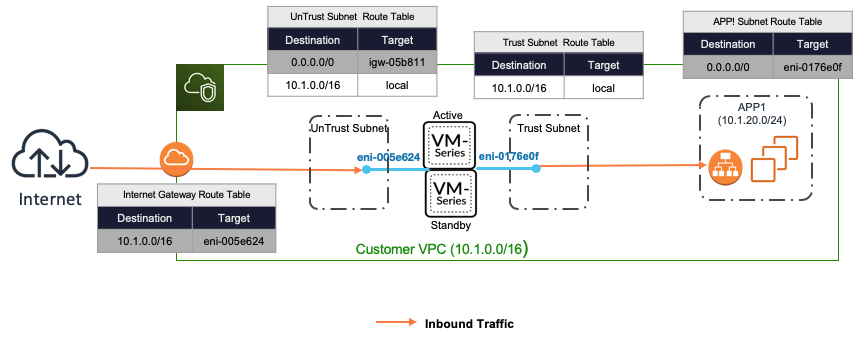
VM-Series virtual firewalls augment native Amazon Web Services (AWS) security groups in your Amazon VPC to protect your web-facing applications with next-generation security features that deliver superior visibility, control, and threat prevention. The VM-Series virtual firewalls apply application-specific threat prevention policies to prevent exploits, malware, and previously unknown threats from compromising applications and exfiltrating data from your AWS environment. With the new integration between the Amazon VPC Ingress Routing feature and VM-Series virtual firewalls, you can now seamlessly insert a VM-Series virtual firewall as a bump-in-the wire in your greenfield and brownfield VPC environments.
With Amazon VPC Ingress Routing, you can define routing rules at the Internet Gateway (IGW) and Virtual Private Gateway (VGW) to redirect ingress traffic to third-party appliances, such as the VM-Series virtual firewalls, before it reaches the final destination. This makes it easier for you to deploy production-grade applications with the security services you require within your Amazon VPC.
AWS provides a wide selection of flexible and compelling services, including AWS Lambda, Amazon API Gateway, Amazon Kinesis, and more. You may have created interface endpoints (a.k.a. AWS PrivateLink) in your Amazon VPC to enable your Amazon VPC workloads to privately access these services. Additionally, you may have enabled your on-premises hosts to privately access these AWS services using these interface endpoints via the virtual private gateway in your Amazon VPC.
With the new integration between Amazon VPC Ingress Routing and the VM-Series virtual firewalls, you can now associate route tables to your virtual private gateway and add route rules to redirect all ingress traffic to AWS services through the firewalls. This redirection ensures that all on-premises traffic accessing these AWS services will pass through the firewalls, strengthening your overall security posture.
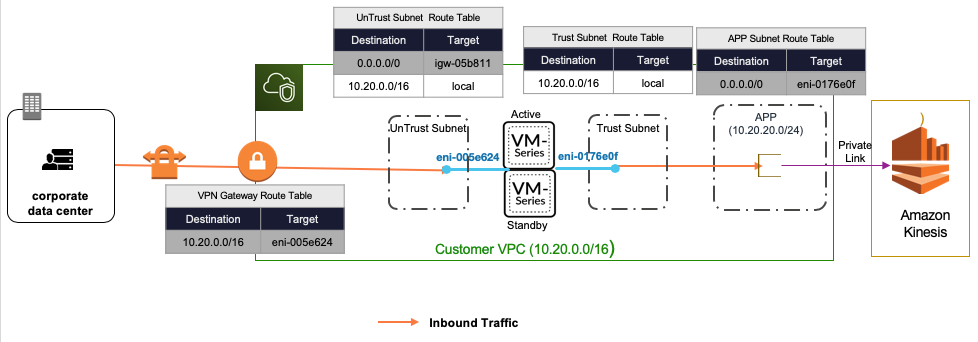
You can now use the Amazon VPC Ingress Routing feature with VM-Series virtual firewalls to improve the security posture of your Amazon VPC. Security is now always turned on for inbound Amazon VPC traffic from the internet and your on-premises environment.
We encourage you to read more about this integration on our TechDocs portal: Overview of HA on AWS.
You may also find more information about AWS on the LIVEcommunity VM-Series on AWS resource page.
We'd love to hear any feedback that you have.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
| Subject | Likes |
|---|---|
| 3 Likes | |
| 2 Likes | |
| 2 Likes | |
| 1 Like | |
| 1 Like |




