
- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
So what are VSYS exactly?
Virtual systems are separate, logical firewall instances within a single physical Palo Alto Networks firewall. Rather than using multiple firewalls, managed service providers and enterprises can use a single pair of firewalls (for high availability) and enable virtual systems on them. Each virtual system (vsys) is an independent, separately managed firewall with its traffic kept separate from the traffic of other virtual systems.
Sounds like a magical solution, doesn't it?
A popular use case for VSYS -- let's say you are a managed security service provider (MSSP) and would like to deliver services to multiple customers with a single firewall.
Another common use case is within a large enterprise that requires different firewall instances because of different technical or confidentiality requirements among multiple departments.
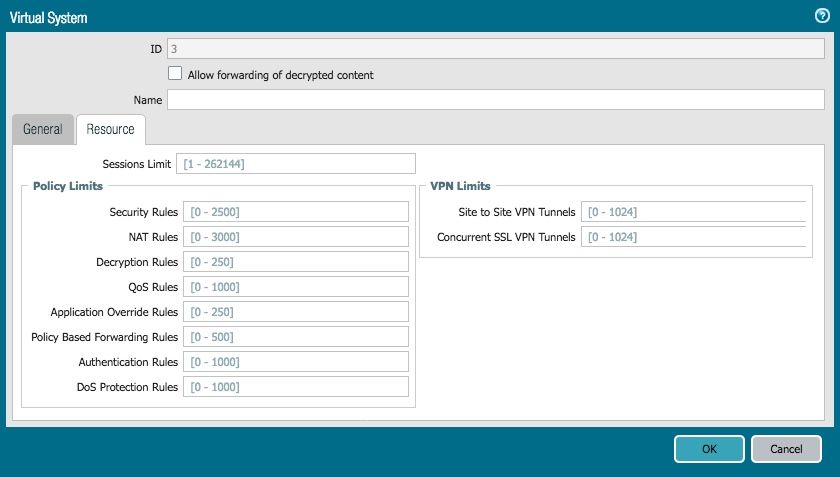 Virtual System Limits
Virtual System Limits
By ignoring this step, the VSYS will fall back to using the hardware limits, which are different for each platform. As a result, you could have one particular virtual system hogging all the device resources, leaving you with some very upset customers that are configured on the remaining VSYS.
Virtual systems can be configured quickly and easily, but can cause some frustration if not done properly.
Seeing that this question on virtual system resources popped up on the discussion board, I hope I have clarified how you can safely configure some limitations per VSYS. This flexibility of being able to allocate limits per virtual system allows you to effectively control firewall resources.
Make sure to check out our admin guide on virtual systems where you can read up on their benefits, typical use cases, and how to configure them. You can also read up on how they function with other features like HA or QoS.
That's it for me!
-Kiwi out.
You must be a registered user to add a comment. If you've already registered, sign in. Otherwise, register and sign in.
| Subject | Likes |
|---|---|
| 3 Likes | |
| 2 Likes | |
| 2 Likes | |
| 2 Likes | |
| 1 Like |




