Read about the new Cortex XDR – Investigation and Response Features introduced in May 2019. See what's new and learn how it can help you. You can also find helpful links to technical documentation about everything Cortex XDR. Got Questions? Get Answers on LIVEcommunity!

This May, explore the new features for Cortex XDR - Investigation and Response.
Here's a list of what's new for you in this release:
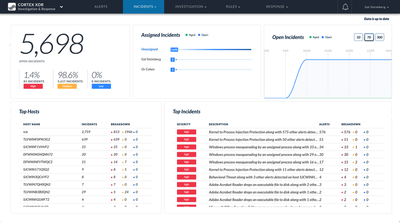
Incident Dashboard
- Cortex XDR – Investigation and Response now provides an overview summary of incidents in your environment. You can now view incidents prioritized by severity, assignee, incident age, and affected hosts from a new dashboard. This enables you to view the security status of your environment over time and drill down into incidents and alerts for additional details.
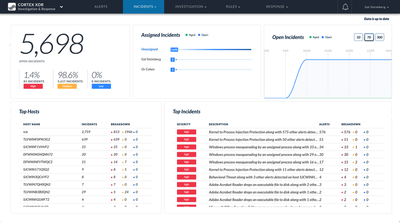 Incidents Dashboard on Cortex XDRRole-Based Access Control
Incidents Dashboard on Cortex XDRRole-Based Access Control
- In addition to the hub (formerly Cortex Hub) administrator roles that you can use to manage access for your apps, you can now assign more granular user roles for Cortex XDR – Investigation and Response from the hub. The new roles enable you to restrict access to specific functions such as threat response capabilities to enforce the separation of information and access for different users in your organization. You can assign the following roles in Cortex XDR – Investigation and Response:
-
Investigation – Provides full access to the Alerts, Incidents, and Investigation tabs.
-
Investigation and Rules View – Provides full access to the Alerts, Incidents, and Investigation tabs, with read-only access to BIOC and IOC rules.
-
Investigation and Response – Provides full access to the Alerts, Incidents, Investigation, and Response tabs.
-
Investigation Rules View and Response – Provides full access to the Alerts, Incidents, Investigation, and Response tabs, and read-only access to Rules.
-
Investigation Rules and Response – Provides full access to all features except the app configuration pages and audit logs.
IoC Rule Exceptions
- In addition to BIOC exceptions, you can now create exceptions to IOC rules to prevent Cortex XDR – Investigation and Response from raising alerts when an IOC is used in a legitimate way.
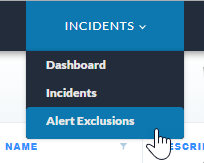
Alert Exclusions
- If you determine certain alerts to be benign and you want to suppress all similar alerts in the app, you can now define an alert exclusion policy. Cortex XDR – Investigation and Response then hides any new alerts that match the policy. If you set an exclusion to apply to existing alerts, the app displays the previously generated alerts as grayed-out in the incident and alert tables.
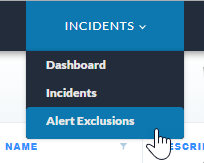 Alert Exclusion
Alert Exclusion
Make sure to check our page for the latest "Features Introduced in Cortex XDR – Investigation and Response" to stay on top of all the new and previously released features!
As always, we welcome all comments and feedback in the comments section below.
- Kiwi out!