- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Forensics Addon - Best practise licence and usage
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Forensics Addon - Best practise licence and usage
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Forensics Addon - Best practise licence and usage
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2022 11:55 AM
Hello dear community,
how do we use this addon?
I had found a article about the forensics addon which said, you can also put this feature to an client/server after the incident etc. happened.
What is the difference between having this addon for all our servers/clients active or to put this profile to our client/server after a real incident which needs a forensic investigation to dig deeper.
How and when does the addon pull the forensic logs, when clients are offline and they get online only for 8 hours? Does it happen when the client is turned on?
We do really want to know if we need to buy more licences for this addon or if it is not neccasarry.
Thanks a lot!
BR
Rob
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2022 07:52 PM
Hi @RFeyertag this boils down to the decision that your management team makes. What customers typically do is to procure an adequate number of Forensics licenses that should cover the count of endpoints that need to be triaged during an incident. That exact number depends on your internal teams based on experience.
Like any process, the XDR Forensics capability can only run when an endpoint is in a power-on state. You can perform an online triage by making the appropriate changes in the corresponding Agent Settings profile and initiating an online triage.
I also believe you're referring to the possibility of an Offline triage here. You can create a Forensics Collector and deploy it on an endpoint manually to collect Forensics evience as well. Once the collection is complete, the zip file can be uploaded to the XDR console for further analysis.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-22-2022 01:20 PM
From point of the technical aspect, I have no clue how the process can be in a real life scenario. Is there any ressource existing, where we can ask how to setup our Cortex XDR for a good practise way belonging to forensics incidents? I know in the end, we will have a team of forensics persons in the house, which will need informations quick. Therefore I thought we will collect every day forensics data from all endpoints.
To divide them to endpoint forensic and endpoint non forensic is not solved well. I would like to see a type of tag to be more flexible without putting the client/server to another endpoint group/policy/profile and dividing the inventory.
So now for my understanding, the triage is the function, which collects all forensic data based on the agent settings to the console/Host Timeline? When the collector in the agent settings is set to 12 hours, what will haben with this data? Is it collected, but the clients needs triage flag to get the informations to the host Timeline?
BR
Rob
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-28-2022 06:57 AM - edited 06-28-2022 08:08 AM
Adding perspective on this question as one of my customer had this process:
1st --> isolated the potential compromise endpoint (https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/investigation-and-response/...)
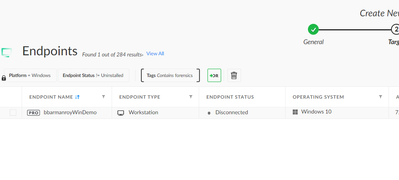
2nd --> assign agent profile with forensic enable (step 10-->item 4 --> https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/endpoint-security/customiza...)
3rd --> wait 24hrs to collect all forensic data (can be customize to lower hrs)
4th --> once data is available, start triage.. (https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/investigation-and-response/...)
Below are additional info on forensics:
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-28-2022 06:35 PM
Hi @RFeyertag to answer your question on creating groups/tags for Forensics, the reasoning is that when an endpoint is flagged for Forensics investigation, it is a potential case of assumed compromise. The endpoint should be ideally isolated to prevent any artefacts from being modified or destroyed in the host, or lateral movement/exfiltration etc. Assigning them to a specific logical partition using tags/groups is the recommended method to ensure the integrity of the forensics activities are maintained.
Surely, you can collect Forensics for all endpoints - however that'd be a huge volume of data collected every day and you'd need to procure additional licenses to ensure all your endpoints are covered, and additional personnel to comb through all of that. You can discuss with your DFIR teams to understand if all endpoints need to be actively covered and how it impact your operations. Existing processes/playbooks are a good way to set a baseline.
You can consider one of the following for creating logical groups for Forensics:
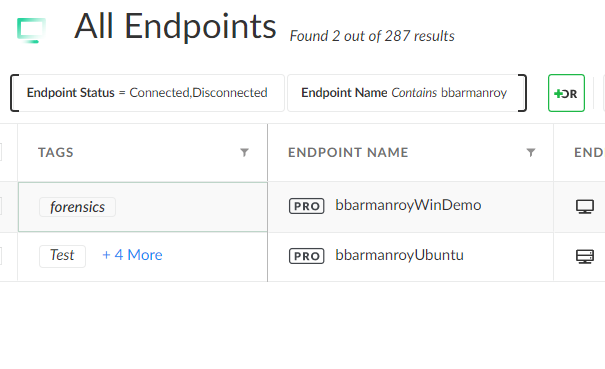
Method A (using endpoint tags)
1. assign user-created tags to specific endpoints as specified in the documentation here.
2. You can define endpoint policies based on the user-created tags like so and apply corresponding endpoint profiles with Forensics enabled:
Method 2 (using static groups)
You can refer to the documentation here.
@jcandelaria has provided you with the links for optimizing your workflows.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-29-2023 06:57 AM
Hello @bbarmanroy & @jcandelaria!
Thanks a lot for your informations to the process of DFIR.
What is the right way to do offline triage, simply case is when the network is locked down?
In my offline triage test I tested now, the installed cortex agent blocked the triage process because there was dropped a vulnerable driver. So, what do you recommend here? Will this also happen in the online/manual triage?
I tried following steps (first the offline triage-configuration with heavy and memory collection):
BR
Rob
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-14-2023 07:34 PM
hi @RFeyertag I am sorry I missed out on your message. Is the issue of vulnerable driver still persistent? If so, please raise a support ticket with the relevant information.
To answer your first question, the difference between online and offline triage are the following
- online forensics consumes one license from your quota of forensics licenses
- online triage will continuously keep collecting forensic artefacts and send it to XDR, whereas you'd need to manually run and upload the collected evidence to XDR (point-in-time snapshot of forensic evidence).
- If the endpoint is isolated with XDR, the online forensic collection capability will still work. That is not applicable for offline forensics as you'd need to manually upload the collected evidence.
- Offline triage is typically used in cases when the endpoint has been completely removed from the network and is "truly" offline, or put in a firewalled segment with no access to other devices, or something along those lines. It requires more work, and such runbooks are typically defined internally within the organization.
- 5985 Views
- 6 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!