- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
XDR 7.6.1 seems to ignore exception
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- XDR 7.6.1 seems to ignore exception
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
XDR 7.6.1 seems to ignore exception
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-25-2022 01:31 AM - edited 01-25-2022 01:33 AM
Hi, Cortex XDR Local Analysis Malware module stops a process called "ClientConsole.exe" (I guess it's a false positive)
I've created a global exception for that issue and checked-in client but XDR still blocks this executable.
In client log I read these rows:
2022/01/25T10:17:33.337+01:00 <Info> VALERIANIT [10128:11292 ] {trapsd:Ptu:Heartbeat:Scheduled:} ignoring admin exception for process: 'clientconsole.exe'
2022/01/25T10:17:33.337+01:00 <Info> VALERIANIT [10128:11292 ] {trapsd:Ptu:Heartbeat:Scheduled:} ignoring admin exception for process: 'clientconsole.exe'
2022/01/25T10:17:33.337+01:00 <Info> VALERIANIT [10128:11292 ] {trapsd:Ptu:Heartbeat:Scheduled:} ignoring admin exception for process: 'clientconsole.exe'
2022/01/25T10:17:33.337+01:00 <Info> VALERIANIT [10128:11292 ] {trapsd:Ptu:Heartbeat:Scheduled:} ignoring admin exception for process: 'clientconsole.exe'
2022/01/25T10:17:33.337+01:00 <Info> VALERIANIT [10128:11292 ] {trapsd:Ptu:Heartbeat:Scheduled:} ignoring admin exception for process: 'clientconsole.exe'
Why XDR ignores my exceptions ????
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-10-2022 01:46 PM
Hi Faber,
This may be due to this process not being protected by a module. By default, your exploit security profile protects endpoints from attack techniques that target specific processes. Each exploit protection capability protects a different set of processes that Palo Alto Networks researchers determine are susceptible to attack. If there are no protection modules enabled on the process, no is exception needed. Please reference Processes Protected by Exploit Security Policy (paloaltonetworks.com) for more details.
There are other modules where Process Exceptions will still apply, like Anti-Ransomware Protection, Child Process Protection, but for all Exploit Prevention Modules the process exception makes no difference for an unprotected process.
If you're investigation has determined the process is benign, you can add the hash to the Allow List (*best practice is to whitelist by hash) and allow it to be executed on all your endpoints regardless of the WildFire or local analysis verdict.
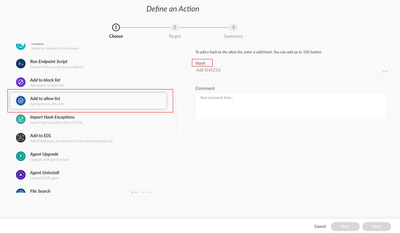
In the UI, Go to Incident Response, Response, Action Center, + New Action
Enter the SHA-256 hash of the file and click
You can add up to 100 hashes at once.
Click Next.
Review the summary and click Done.
Reference Manage File Execution (paloaltonetworks.com)
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-02-2025 02:35 AM
А якщо інцидент генерується модулем "Local Analise", а програма яка генерує це, створює що разу нові файли з новими хеш-сумами?
Яким чином можна добавити у виключення?
Бо за шляхом папки яка добавлена у виключення звідки генеруються файли, XDR всерівно блокує.
- 3180 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to add exception for known macros detection by cortex XDR in Cortex XDR Discussions
- Cortex XDR FIM in Cortex XDR Discussions
- SBAC limitations: Delegation of full control (profiles and exceptions) for a specific group of endpoints. in Cortex XDR Discussions
- Custom BIOC Rule won't apply to Prevention Profile in Cortex XDR Discussions
- API for exceptions? in Cortex XDR Discussions