- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Playbook Creates Incidents from Table.
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XSOAR Discussions
- Playbook Creates Incidents from Table.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-24-2022 08:36 AM - edited 10-24-2022 08:39 AM
I'm trying to create incidents from a Cortex XSOAR SIEM integration. The integration allows me to list alerts and I'm trying to create an incident for each one. When I run the playbook, the list alerts command returned multiple entries, but the create incident task is only creating 2 incidents opposed to 10 alerts.
I want to ensure that we're generating an incident for every SIEM alert.
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2022 05:40 PM
Hi @king_penson, the Securonix integration is developed and managed by the vendor. Please contact support@securonix.com.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-24-2022 04:26 PM
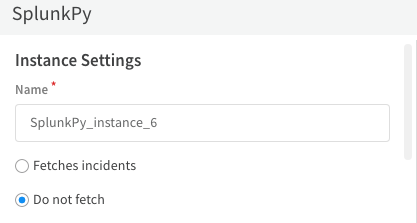
Hi @king_penson, What SIEM integration are using? Most if not all our SIEM integration can be configured to fetch incidents. The example below is from Splunk.
If you have the list of incidents inside the context, could provide screenshot as an example. Also, a screehshot of playbook task would help.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2022 02:09 PM
Hello, sorry for late response. I was able to figure it out. The Securonix integration has a command that fetches a list of violations aka alerts, which are different from incidents.
I was able to create a script to pull that data and format them into xsoar incidents. This might be a thing worth adding to the integration considering some customers want to look at each violation separately.
- Mark as New
- Subscribe to RSS Feed
- Permalink
10-31-2022 05:40 PM
Hi @king_penson, the Securonix integration is developed and managed by the vendor. Please contact support@securonix.com.
- 1 accepted solution
- 3120 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Username Generalization Playbook in Cortex XSIAM Discussions
- Cortex XDR Playbooks – Most returning errors, looking for working use cases in Cortex XDR Discussions
- Playbook for Disabling Azure User in Cortex XSOAR Discussions
- Fetched Integrations Objects in XSIAM 3.4 in Cortex XSIAM Discussions
- Create a IOC without incident in Cortex XDR Discussions