- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Configure second DUO for PA firewall MFA
- LIVEcommunity
- Discussions
- General Topics
- Re: Configure second DUO for PA firewall MFA
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2023 07:56 AM
We have configured a DUO Proxy server for PA firewall MFA and it works. We also configured the second DUO proxy server for redundancy. However, we don't know how to configure PA firewall to failover to the second DUO in a case the primary DUO proxy server is down. Any help?
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2023 09:20 AM
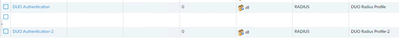
You need to add auth sequence under "Device > Authentication Sequence"
Add both RADIUS profiles there.
Configure GlobalProtect auth to use previously configured sequence.
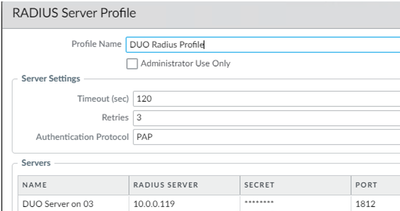
Check how many retries and timeout your RADIUS profiles have configured under "Device > Server Profiles > RADIUS".
Let's assume that you have 2 attempts with 20 sec timeout.
This leaves 20 seconds for secondary RADIUS server as GlobalProtect will time out in 60 seconds by default.
You might want to extend GP timeout.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMD5CAO
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2023 05:21 AM
You have timeout 120 sec.
That is eternity 🙂
For failover to ever happen it would take 3x120 sec.
GlobalProtect will wait only 60 sec by default until it times out.
Did you adjust GlobalProtect default timers?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2023 09:12 AM
There is no official way to configure active/active.
Utilizing NAT with session distribution is kind of a hack that you can use if you really need active/active.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2023 09:20 AM
You need to add auth sequence under "Device > Authentication Sequence"
Add both RADIUS profiles there.
Configure GlobalProtect auth to use previously configured sequence.
Check how many retries and timeout your RADIUS profiles have configured under "Device > Server Profiles > RADIUS".
Let's assume that you have 2 attempts with 20 sec timeout.
This leaves 20 seconds for secondary RADIUS server as GlobalProtect will time out in 60 seconds by default.
You might want to extend GP timeout.
https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000PMD5CAO
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2023 01:26 PM
Thank you for the tip. Is it possible to configure active/active or balance? If so how to do it?
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2023 01:44 PM
Hi @boblin ,
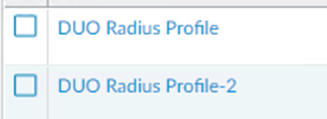
The easiest way to configure redundancy for the same protocol is to add multiple servers in the RADIUS Server Profile. However, this will not load balance. The NGFW will try each one from the top down. https://knowledgebase.paloaltonetworks.com/KCSArticleDetail?id=kA10g000000ClqECAS
Thanks,
Tom
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2023 06:21 PM
It is true that multiple servers can be added into single profile but I stopped doing this after I got bit by some bug back in a day where connection was attempted to first server only.
From then on every server is in dedicated profile and I use sequence instead.
Probably overkill nowadays but more robust.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2023 02:47 PM
Thank you for all tips. I have configured the second DUO proxy server, but it doesn't work. To troubleshooting, what would you do? Perhaps, where I can check the logs?
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2023 03:02 PM
I find authproxy.log and it shows:
2023-04-26T15:56:36.843265-0500 [duoauthproxy.lib.log#info] Duo Security Authentication Proxy 5.7.4 - Init Complete
2023-04-26T16:08:57.409802-0500 [-] (UDP Port 1812 Closed)
2023-04-26T16:08:57.409802-0500 [-] Stopping protocol <duoauthproxy.lib.forward_serv.DuoForwardServer object at 0x0000028A1FE91E80>
2023-04-26T16:08:57.409802-0500 [-] Main loop terminated.
2023-04-26T16:09:05.780813-0500 [-] DuoForwardServer starting on 1812
2023-04-26T16:09:05.780813-0500 [-] Starting protocol <duoauthproxy.lib.forward_serv.DuoForwardServer object at 0x0000021AA5B81CA0>
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] FIPS mode is not enabled
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] Reactor in use: <twisted.internet.selectreactor.SelectReactor object at 0x0000021AA32785E0>
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] AD Client Module Configuration:
2023-04-26T16:09:05.876008-0500 [duoauthproxy.lib.log#info] {'host': '10.0.0.58',
Can someone tell the problem from the logs/ Or what should I check.
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2023 03:04 PM
First thing first, can you authenticate to the secondary RADIUS server that you create separate from the authentication sequence that you configured (create a temporary Authentication Profile with just the new config if needed)? Via the CLI you can do this with the 'test authentication authentication-profile' command to verify that it just isn't an issue on that secondary node.
You can auto review the authd log file by using 'less mp-log authd.log' on the CLI as well.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2023 06:18 PM
The second DUO Proxy server configuration is correct and works if I don't use authentication sequence. For example, the first duo proxy IP is 10.0.0.119
in RADIUS Server profile, if you change the IP to second DUO proxy 10.0.0.183, it works.
If in Authentication Profile, I have two profiles.
and authentication sequence has two profiles.
Only DUO Profile works. If I stop the first duo proxy server, it doesn't work.
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-26-2023 06:31 PM
How do you run 'test authentication authentication-profile'? I keep getting Invalid syntax.
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2023 05:21 AM
You have timeout 120 sec.
That is eternity 🙂
For failover to ever happen it would take 3x120 sec.
GlobalProtect will wait only 60 sec by default until it times out.
Did you adjust GlobalProtect default timers?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2023 06:04 AM
In addition to the timeout aspect that @Raido_Rattameister already mentioned, the command that I gave you above was a starting point so you knew what to run instead of a full example. Assuming that your authentication profile is "DUO Authentication" the full example would be below:
test authentication authentication-profile "DUO Authentication" username <username> passwordOnce entered you'll be prompted to enter the password before the firewall attempts to authenticate, you don't include the password in the command.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2023 08:31 AM
Tom.
Now, the I have two DUO profile in the authentication sequency and it works. However, it seems to me this is active/passive. How can we setup active/active or balance?
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2023 08:40 AM
Active/Active can be only set if RADIUS profile points to NAT policy in Palo and this NAT policy has dynamic destination IP with session distribution.
But it will not check if destination is live or not.
DNAT is just round robin or least session etc basis.
No other way to set active/active.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2023 08:44 AM
Thank you for quick reply. Do you have document for configuring active/active or an link?
Data recovery, Windows OS Recovery, Networking, and Computer Troubleshooting on
http://www.ChicagoTech.net
How to Install and Configure Windows, VMware, Virtualization and Cisco on
http://www.HowToNetworking.com
- 3 accepted solutions
- 9819 Views
- 16 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- View Palo Alto Configuration through Panorama CLI commands in Panorama Discussions
- Cloud Identity Engine - Sync / Attribute Verification in General Topics
- bioc not prevent in Cortex XDR Discussions
- Palo Alto with AI assistant in Strata Copilot Discussions
- Request to locate account or transfer asset for S/N 023209008637 in Custom Signatures