- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Disable NAT from Untrusted to Trusted device
- LIVEcommunity
- Discussions
- General Topics
- Disable NAT from Untrusted to Trusted device
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Disable NAT from Untrusted to Trusted device
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-28-2020 02:12 PM
Hello!
I am trying to port forward port 25 traffic without a NAT to an email security appliance behind the firewall. The problem is when SMTP traffic is forwarded through the Palo Alto the client-IP address of all e-mail going to the email security appliance is the private IP of the Palo Alto. I need to disable NAT for this traffic so that the IP address hitting the appliance is the source IP. Right now I have the following configuraiton:
Internet -> Untrusted Interface (Public IP NIC2) -> Trusted Interfance (Private IP NIC3) -> Translated Destination IP (Device Static IP)
For my NAT policy Below ->
Original Packet:
Source Zone Unstrust, Destination Zone Untrust, Destination Interface NIC 1 of Unstrusted zone, Service SMTP, Source Address ANY, Destination Address Private IP of NIC 1
Translated Packet:
Translation Type Dynamic IP and Port, Address type Interface Address, Interface NIC 2 of Trusted Interface, Destination Address type Static IP, Translated Address Static IP of device
My Security Policy's source is set to Untrust, Destination set to trust, Both Destination Address options are set to any, I have a custom SMTP rule to allow smtp traffic, Service Category set to application-default, action set to allow
I've tried a number of different combinations but can't seem to figure out how to do this. Has anyone done this before?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-28-2020 02:25 PM
Hello,
Does the email appliance have a public or private IP address? if Private, NAT must be enabled.
Regards,
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-28-2020 03:03 PM
At the moment it has both a private and public IP address. Also this is in an Azure environment. Is there a way to do it without NAT with it having a public IP? Is what you are possibly suggesting is having the Appliance in front of the firewall?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-31-2020 07:44 AM
I've set the setting of Translation Type to none which "should" disable the NAT but it stops all communication to the virtual appliance. I can no longer telnet via port 25 once that option is enabled. On a Fortigate it is possible to disable NAT so the original IP is listed as the client IP; I can't believe that this might not be possible on a Palo Alto
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-02-2020 11:29 AM
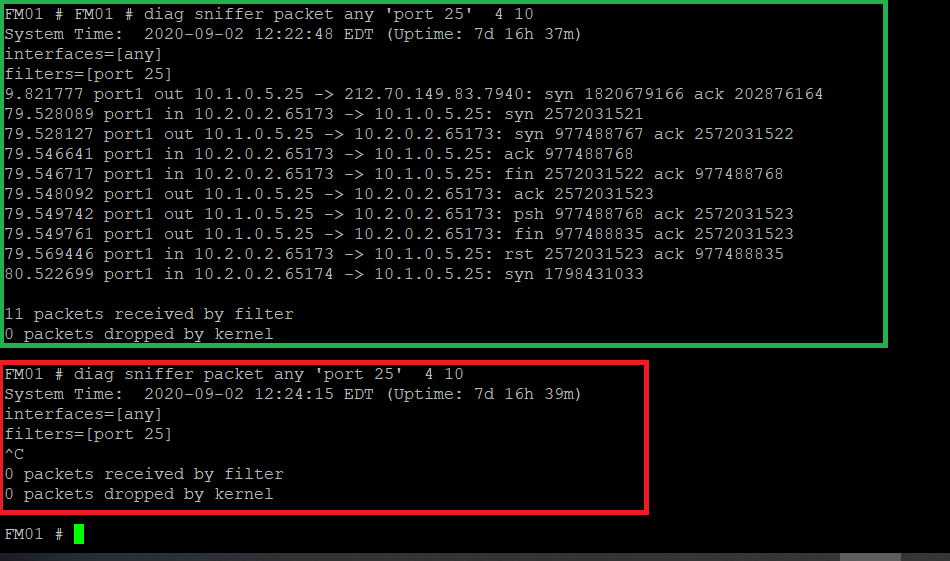
While doing the command "diag sniffer packet any 'port 25' 4 10" which sniffs all port 25 traffic after associating the VM Appliance's subnet in the route table in Azure to Palo Alto's private TRUST ip address which forces all traffic to go through the Palo Alto; I psping'd the private ip of the VM Appliance on port 25 "psping 10.1.0.5:25" to make sure that packing sniffing was working. In the screenshot you will see in green that it works. My second test is I tried to telnet to port 25 from the Palo Alto public IP address that is forwarding port 25 traffic to the VM Appliance with NAT Disabled and can confirm that the traffic is not hitting the VM Appliance which you see in red with no response from packet sniffing. Port 25 traffic is not leaving the Palo Alto when turning NAT off. You can see below with the following screenshot.
- 4833 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- No "certificate used by" field when generating certs for SSL forward trust and untrust? in General Topics
- Decryption Profile in General Topics
- Forward Proxy & SSL Inbound Inspection Certificate Comparasion in Next-Generation Firewall Discussions
- OCI PA vm unable to communicate outside in General Topics
- PaloAlto Firewall and Cisco Expressway integration with NAT Reflection in Next-Generation Firewall Discussions