- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
dmz design
- LIVEcommunity
- Discussions
- General Topics
- Re: dmz design
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-05-2018 01:45 PM
Hi,
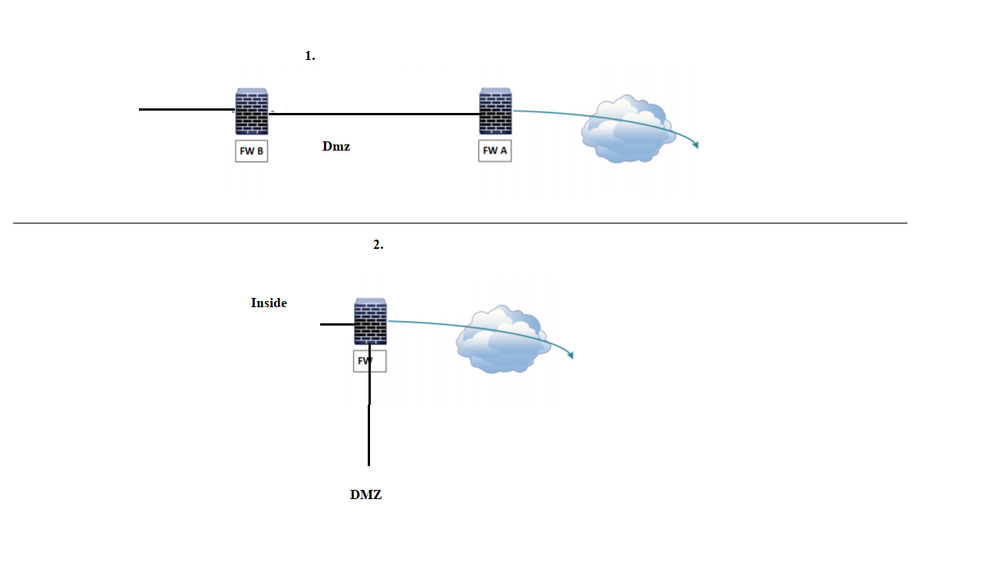
What is the benefit of having DMZ setup with two firewalls.
If we have dmz setup with two firewalls ( I don't know this design is valid and adopted design, I found it in the net )
If this is a valid design ,From local lan how the traffic flow to outside (10.0.10.0/24 to internet ) and outside the local lan 10.0.10.0/24
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-13-2018 11:07 AM
@Mick_Ball wrote:Ok the following example is for reverse proxy.
single firewall......
web requests enter the outside interface.
then routed to the dmz.
the reverse proxy on dmz then requests the web page from the lan via the same dmz interface,
so you have in and out traffic on the dmz interface.
twin firewall......
web requests enter the outside interface on firewall 1.
then routed to the dmz.
the reverse proxy on dmz requests the web page from the lan via the dmz interface on on firewall 2.
the same scenario applies to various other services within dmz, rdp gateways etc and even dns servers.
if you have just a web server on dmz then tromboning is not so much of an issue.
it all depends on your setup, data demands and services provided.
for a small to medium network, single firewall should suffice.
if your still having issues with the twin concept then happy to post a drawing on monday.
mick.
Hi mick ,
It would be real help if you could post
Thanks a million
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-15-2018 09:03 AM
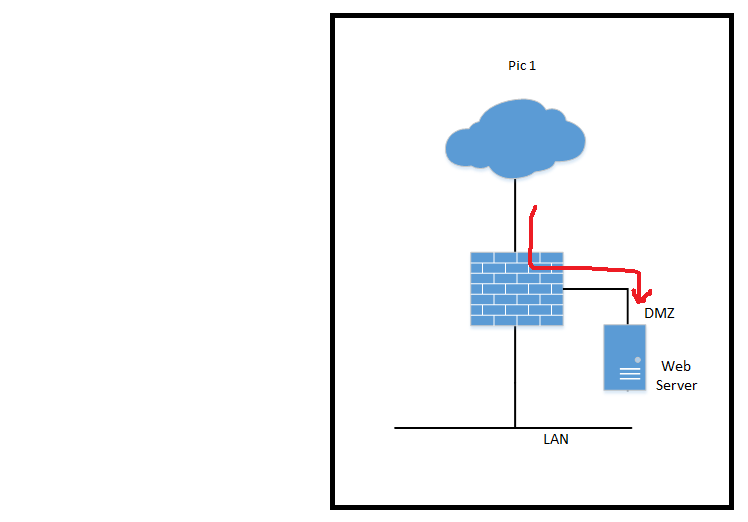
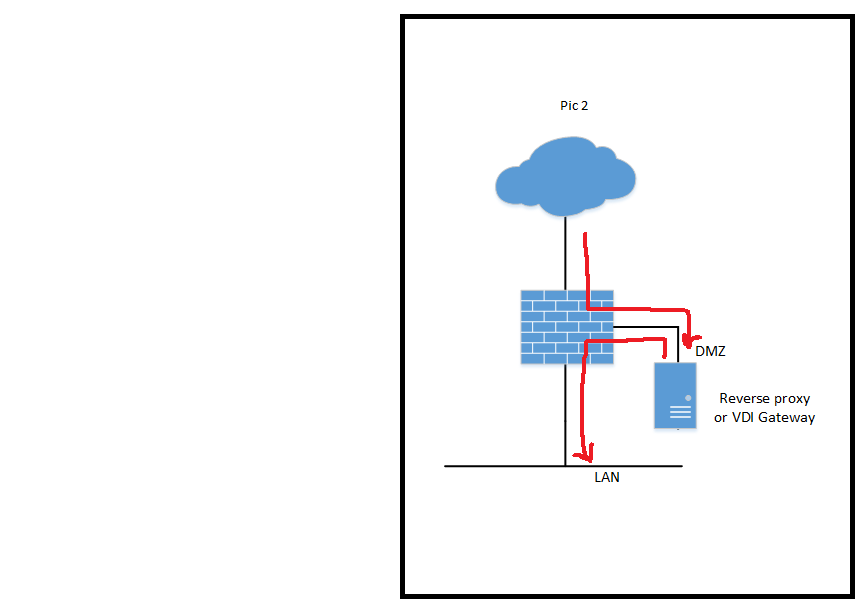
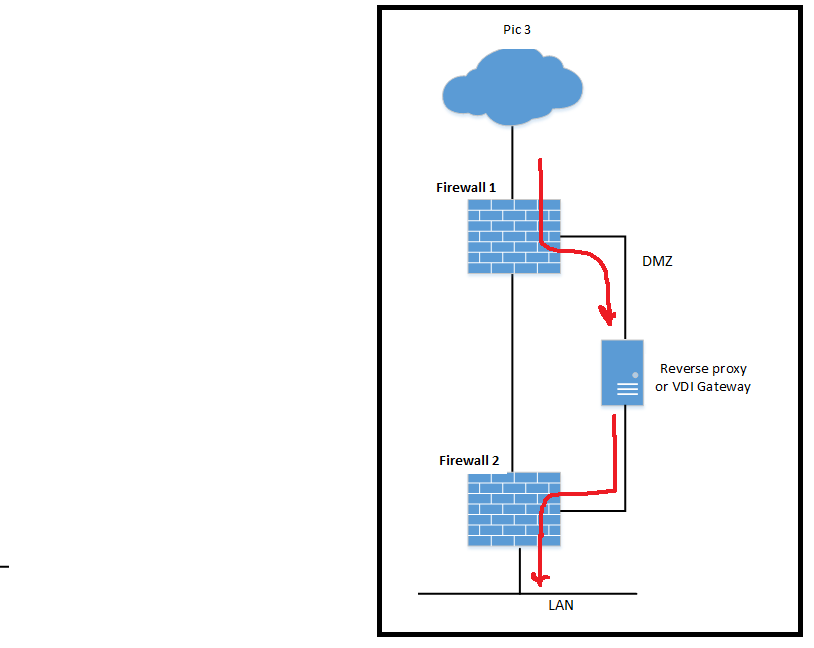
The red line in the following pics shows the flow of data requests.
Pic 1. this is for web server access from the internet. traffic is only allowed to the web server in DMZ.
Pic 2. if you use RDP gateways, reverse proxies etc then with a single firewall the data flow from the internet passes into the DMZ and back out again to the LAN via the same interface.
Pic 3. to reduce this in and out (tromboning) effect you can add a second firewall. so.. the data request enters firewall "1" but the proxied or forwarded traffic passes through firewall "2".
please note... this is only a requirement if you need the extra security or have massive data requests.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2018 06:37 PM
Hi,
Thanks for the detailed reply and appreciate your effort .You are amazing .
It would be great If you could give if you could share the best design if there is something called 'best design ' 🙂
Thanks a million
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-19-2018 02:14 AM
thats almost impossible to answer as all network designs, security levels and ammounts of data requests are different.
for simplicity and cost Pic 1 is the obvious choice.
both designs perform exactly the same task of creating a DMZ.
it all depends on the network design, ammounts of data requests etc..
i could not even suggest a level requirement as you could have 2 servers offering mega data or 100 servers not doing much at all....
nowadays data links and firewall processers are exceptional compared to previous decades so it all depends on your requirements and network designs.
Mick.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2018 09:26 AM
hi,
In pic3 ,lets say I have a web server , what should be the gateway on that server ?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2018 11:26 AM
Hello @simsim.
that depends on who needs access to the server.
assuming you need access for both internal and external users... your default gateway will be firewall 1. You will then need static routes to your internal network via gateway firewall 2.
however there are other options...
if you do not want your server to have default gateway to firewall 1, you can have firewall 2 as default gateway and then NAT your incoming traffic to the interface on firewall 1.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-05-2018 11:09 PM
Hi,
Thanks for the reply .
assuming you need access for both internal and external users... your default gateway will be firewall 1. You will then need static routes to your internal network via gateway firewall 2.
let's say lan is 192.168.0.0 and 10.0.0.0/8 and DMZ is 172.16.0.0/8
If I give default gw fw1,server will always choose the path fw1?
So what s the point of giving static routes on fw2 ?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2018 03:07 AM
On you server... default gateway via firewall 1.
on your server ... static routes to 192.168.0.0/16 and 10.0.0.0/8 via firewall 2.
any traffic to static routes will take priority over default gateway.
so... any traffic to 192.168.0.0/16 and 10.0.0.0/8 will go via firewall 2, all other traffic will go via firewall 1.
you need to know that a default gateway is only used when your server does not know a route for a particular network.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2018 05:30 AM
Hi,
if you do not want your server to have default gateway to firewall 1, you can have firewall 2 as default gateway and then NAT your incoming traffic to the interface on firewall 1.
can you explain this also ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2018 08:28 AM
Ok, if firewall 1 has dmz address of 172.16.0.1 then you could have a NAT policy on that firewall for..
source= external, destination=server, source NAT address 172.16.0.1.
this will mean that the server will see all external traffic as 172.16.0.1, so it will not need a route or gateway as this is on it’s LAN.
it will simply reply to 172.16.0.1 and the firewall 1 will return the traffic to the un NAT’d address...
so...
46.16.3.4 sends a request to the server, the firewall 1 forwards this to the server but adds source NAT 172.16.0.1.
the server replies to 172.16.0.1 and the firewall 1 un-NAT’s and sends back to 46.16.3.5.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2018 07:30 PM - edited 04-07-2018 07:41 PM
Hi,
What about the internal traffic in this case , Internal traffic must go to fw2 ?.
If no gateway , how the server access the internet ?
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-08-2018 12:09 AM
You could either set the server default gateway to firewall 2 or add static routes to 192.168 and 10.0.
or you could use NAT from trusted to DMZ. As previously explained for untrust to DMZ.
at some point your server will need a default gateway or static routes as it may need to initiate connections to other servers or devices.
- 15679 Views
- 26 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- Does Prisma Browser support device-based Conditional Access (device ID / compliance)? in Prisma Access Discussions
- Design active passive connected with vrrp switches in General Topics
- playbook completely stuck on a simple condition in Cortex XSOAR Discussions
- SBAC limitations: Delegation of full control (profiles and exceptions) for a specific group of endpoints. in Cortex XDR Discussions