- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
DoS applictation attack to DNS server - how to prevent, and how to create report showing IP addressess with the highest number of session (not bytes) opened to it
- LIVEcommunity
- Discussions
- General Topics
- Re: DoS applictation attack to DNS server - how to prevent, and how to create report showing IP addressess with the highest number of session (not byt...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
DoS applictation attack to DNS server - how to prevent, and how to create report showing IP addressess with the highest number of session (not bytes) opened to it
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2014 07:58 AM
From time to time I observe a lots of DNS queries (not UDP floods) from Internet to my DNS servers. Unfortunately those queries have negative inpact to my old firewall (it can't establish so many sessions, which makes the network stops).
Probably my DNS servers are targets of:
- DoS application layer attacks: target specific applications, eg DNS dictionary attacks becuase I can see many DNS requests to unknown domains, which even doesn't exists on Internet.
rahter than
- DoS volumetric attacks: designed to saturate and overwhelm network recources, eg DNS Reflection, DNSSec Amplification, because I don't see DNS responses
My questions are:
1. PAN device is offering Zone/DoS Protection featers How to configure those featers to prevent my whole network from such DoS application attacks?
2. How to create report showing IP addresses with the highest number of session (not bytes) opened to my DNS servers behind PAN device? I would like to know (just in case) if in the future my DNS servers would be a target of DoS volumetric attack.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2014 08:51 AM
Hello Sir,
1. Please follow the below mentioned documents, it will help you to understand and configure DOS/ZONE protection profiles on PAN firewall.
Few related docs to troubleshoot:
a. CLI commands to verify the DOS functionality on Palo Alto Networks Devices
b. What are the Differences between DoS Protection and Zone Protection?
c. Global Counters Triggered by a Zone Protection Profile
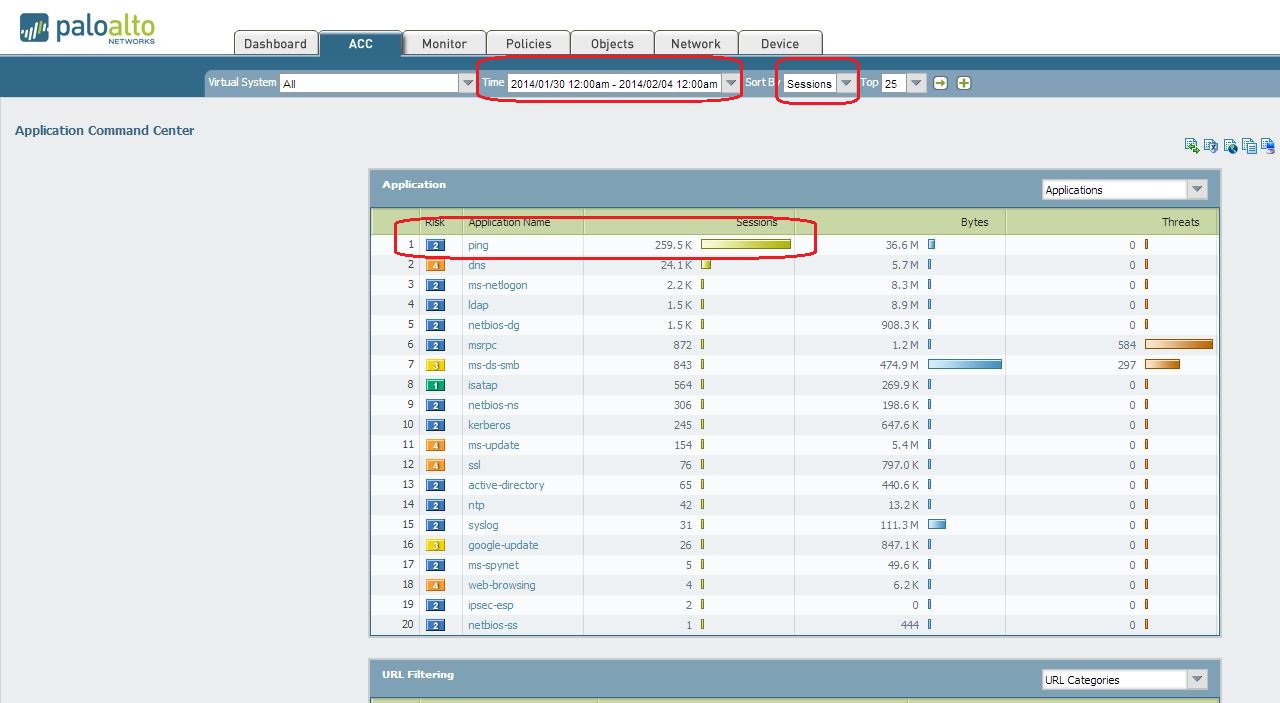
2. You can create a custom report under ACC tab ( Application Command center). Please see the example below:
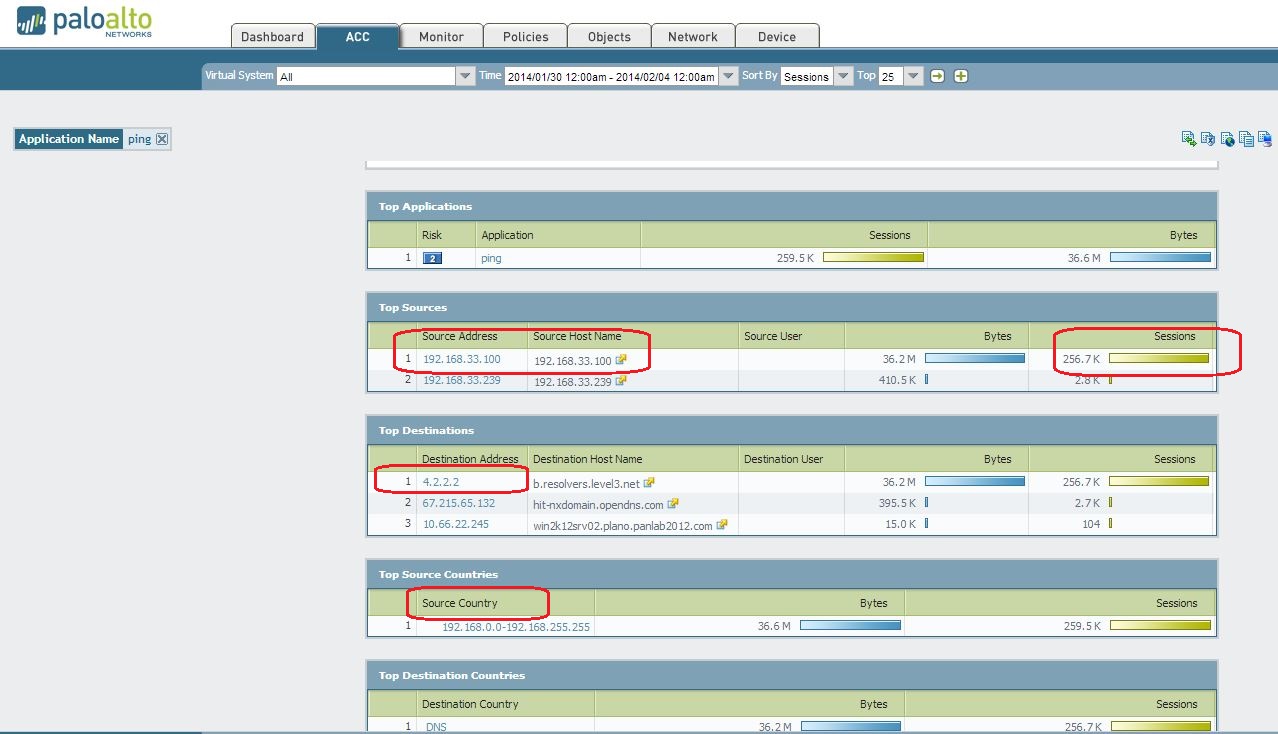
Next, click into the application, where you want see the source and destination IP details:
Hope this helps.
Thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2014 12:22 PM
Hi Mariusz,
In addition to the DOS protection, you may wish to consider using one of the DNS hosting services out there. Then you won't see traffic like that targeted at your DNS servers. I use DNS Made Easy, and I can tell you, they can take a bigger hit than I can. Anyway for public DNS, it's a good way to go, and it isn't expensive.
Cheers,
Mike
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2014 03:20 PM
Ad1. I was thinking about your recomendation how to configure DoS protection regarding described attacks, not sending documents from Knowledge base.
Is it possible anyway to prtoect from DoS application layer attacks with Palo Atlo?
Ad2. I know about ACC tab, but I was thinking about Manageed Custom Reports, and your advice how to configure such report grouped by seession.
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2014 03:25 PM
Mike, you'are definitely right, maybe this is workaround but I agree it works, always ![]()
Anyway I would like to tackle the problem without external dns hosting services..
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-05-2014 04:13 PM
Mariusz,
You may also wish to reduce the session timeout for the dns application from the default 30 seconds to something a bit lower. This would tear down the udp sessions sooner thus reducing the size of the connection table that relates to DNS traffic. The other approach with DOS protection is to utilize resource protection and limit the number of concurrent sessions you allow to your DNS servers. Hope this provides some additional options for you to think about.
Phil
- 6229 Views
- 5 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!




