- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Dual ISPs VPN failover across both
- LIVEcommunity
- Discussions
- General Topics
- Dual ISPs VPN failover across both
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Dual ISPs VPN failover across both
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-18-2022 11:43 AM - edited 08-18-2022 11:59 AM
Trying to provide some tunnel redundancy to some of our AWS environments. I have 2 ISPs both with an interface/static IPs on my HA PANs. ISP-A is my default with a default route to the internet pointing to its next hop.
ISP- A Eth1/8 9.9.9.9/24 ZONE-A
ISP-B Eth1/7 10.10.10.10/24 ZONE-B
Currently have all my VPN tunnels across ISP-A and want to bring up some tunnels across ISP-B. I created the IKE gateways and attached them to Eth1/7 ISP-B but in the logs I see the VPN traffic being dropped because its sending the traffic from Eth1/7 to Eth1/8 which is wrong, it should just go from Eth1/7 to the internet. I am missing something but not sure what.
Do both public interfaces need to be in the same ZONE? That is the only thing I can really see that maybe causing it. We have 2 static routes pointing out each ISP with the metric on the ISP-B higher than ISP-A so it prefers that route.
How do I force specific VPN tunnel traffic out of the secondary interface? I thought just trying the gateways to that interface would suffice but it doesn't appear to be the case.
Do I need static routes pointing to ISP-B for each tunnel endpoint at AWS?
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-19-2022 11:34 AM
Hello,
First the zone question. Basically its your preference, zones are there to provide logical separation so that security policies can/will be applied to the traffic.
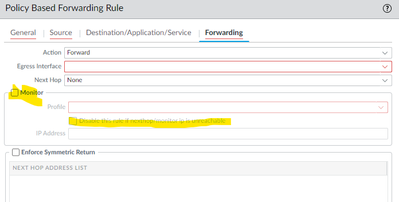
Second the VPN tunnels: What I did was create the tunnels to AWS. Then I created Policy Based Forwarding rules to force the traffic down one tunnel and have the tunnel removed if it fails.
This way I dont have traffic dropped due to asymmetric return. AWS is all policy based routing so it gets goofy under the hood. This is why I chose the PBF rules instead of dynamic routing etc.
Hope that makes sense.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-22-2022 07:22 AM
I don't mess with PBF at all anymore as it was more work than it's worth. For redundancy to the internet we utilize 2 static routes (1 with a higher cost) and path monitoring. That eliminates the need for PBF and having to make sure all the right subnets are configured and all that noise.
As far as VPN failover I got it working by simply adding static routes pointing to the secondary AWS tunnel IPs via the secondary circuit and run BGP across all of it. Works great.
- 3028 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Active Passive Failover in AWS in VM-Series in the Public Cloud
- OSPF process crashes after manual HA Failover in Next-Generation Firewall Discussions
- HA failover on Acitve Passive concerns in Next-Generation Firewall Discussions
- Panorama HA Pair and Managed Log Collectors Upgrade Process - Clarification in General Topics
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics