- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GlobalProtect not using AD group
- LIVEcommunity
- Discussions
- General Topics
- GlobalProtect not using AD group
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 05:58 AM
Hi,
I am running a PA-VM on AWS. It has two interfaces, one for management, one for data.
I have created an LDAP connection to our network and can log into GP using my AD credentials. So far, so good.
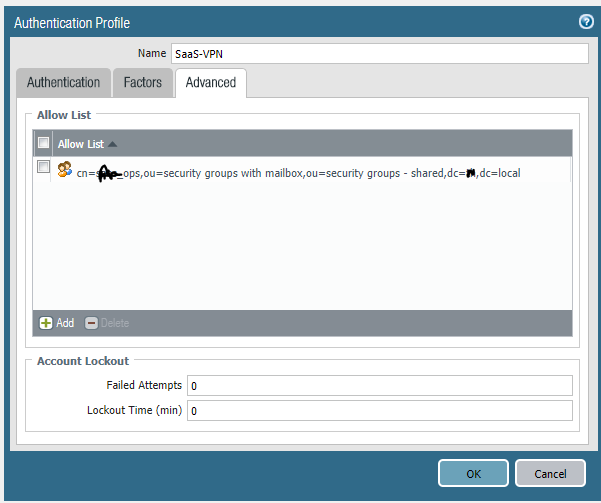
I need to have separation of users and assigned IPs based on group membership. I have an authentication profile with two sequences. One to match on the group that my account is a member of, the second uses local authentication.
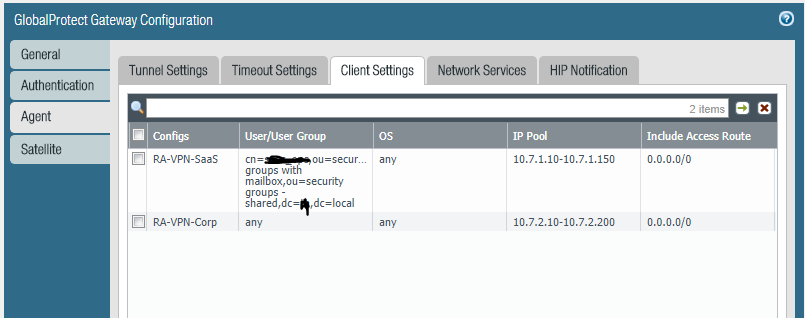
In the GP gateway, I have the authentication set to the auth sequence (which uses the first authentication profile - the one that should match my account and group set first), and in the agent client settings, I have two entries. the first one should give me an IP address from the first range, the second entry is set to any/any and gives an IP from a different range.
When I connect, I use my username/password from AD but get an IP address from the second range.
The logs show these entries (note I have replaced the actual AD details):
1,2017/09/12 05:48:17,4E0FEDAE31E65C2,31,0x0,USERID,login,53,2017/09/12 05:48:17,0,0,0,0,,PA-VM,1,vsys1,10.7.2.10,xx\sfordham,,0,1,2592000,0,0,vpn-client,globalprotect,0,0,,2017/09/12 05:48:18,1
admin@PA-VM> show user group-mapping state all
Group Mapping(vsys1, type: active-directory): SaaS-Users
Bind DN : CN=xxx,OU=xxx xxx - Shared,DC=XX,DC=xxx
Base : DC=XX,DC=xxx
Group Filter: (None)
User Filter: (None)
Servers : configured 1 servers
213.78.96.130(389)
Last Action Time: 1607 secs ago(took 0 secs)
Next Action Time: In 1993 secs
Number of Groups: 1
cn=replaced_xxx,ou=security groups with mailbox,ou=security groups - shared,dc=xx,dc=xxx
admin@PA-VM>
admin@PA-VM> show user ip-user-mapping all
IP Vsys From User IdleTimeout(s) MaxTimeout(s)
--------------- ------ ------- -------------------------------- -------------- -------------
10.7.2.10 vsys1 GP xx\sfordham 2591689 2591689
Total: 1 users
admin@PA-VM>
From what I have read, GP in the above command *should* be AD
admin@PA-VM> show user user-ids
User Name Vsys Groups
------------------------------------------------------------------
xx.xxx\sfordham vsys1 cn=replaced_xxx,ou=security groups with mailbox,ou=security groups - shared,dc=xx,dc=xxx
Total: 22
admin@PA-VM>
So it looks like it is reading all of the necessary details - I can log in using my AD account, for example - it's just the mapping that's incorrect.
Can anyone advise?
Apologies if I have missed something blindingly obvious. I only started working with PA last week, so am learning as I go!
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-14-2017 03:15 AM
policies based on group membership are more scaleable.
you may only have two main types of users but we have tons, so would need to create a subnet range for each group.
then, we still need to add policy to allow subnet range or deny.
we have 1 x.x.x.x/19 scope for all users and when all the pilicies are in place we just move users in ad groups accordingly.
actually we have 2 x.x.x.x/19 subnets for each gateway, you may not need /19 but you will deffo need 2 different scopes per gateway.
happy to discuss why when you decide your way forward with groups.
please note, you may need to enable "user mapping" to be able to policy all traffic on your PA, not just VPN stuff.
i may not have explained this very well....
sorry for the essay....
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 06:38 AM
firstly, check the monitor\system log to ensure you are authenticating as domain\user name to both the portal and gateway.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 06:40 AM
sorry, cancel the above....
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 06:43 AM
Ok, cancelling... but here are the logs just in case...
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 06:57 AM
could you confirm that under network/gateways/(gateway name)/agent that you have 2 configs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 06:58 AM
oops.. missed off /client settings
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:01 AM
Check! both are there, and I am getting an IP address from the Corp pool - not the first pool as I would like...
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:09 AM
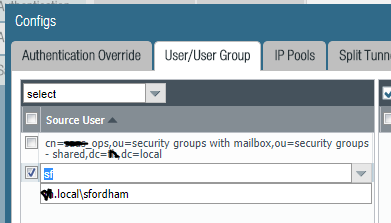
open up your first config and add another user, start typing sford and see if your name auto appears
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:17 AM
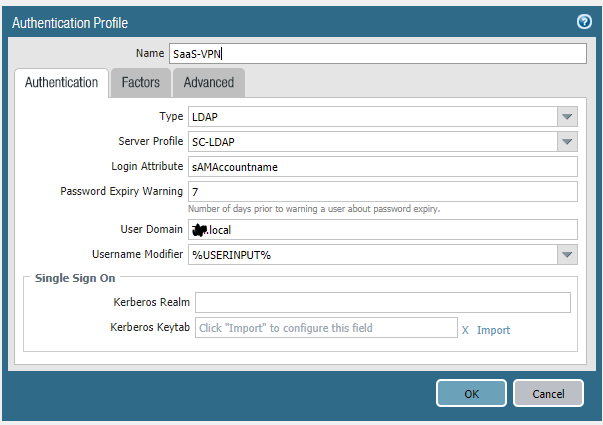
could you provide print screen of ldap auth profile
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:20 AM
I this what you mean?
there are no settings under "Factors"
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:30 AM
ok i'm not so good with domain names, we do not have a something.local in our domain name. just a single entry.
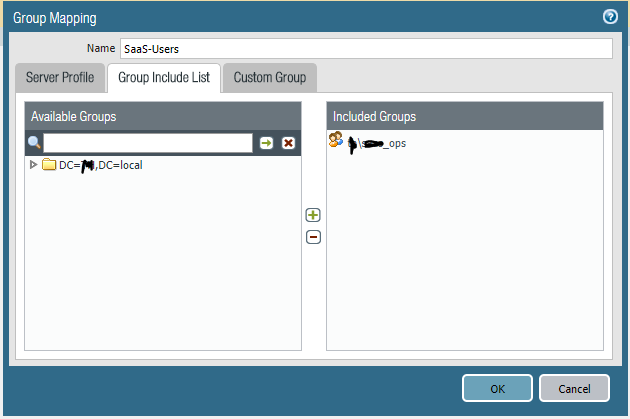
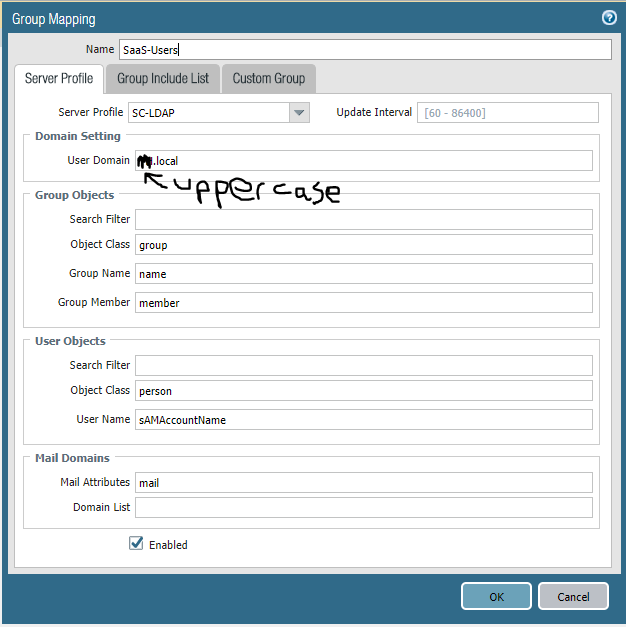
hopefully someone else will jump in with more domain experience but could you just post device/user id/group mapping settings/(name)/server profile.
also.. under the gateway client settings, just enter your name manually without domain info. and test.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:41 AM
The only difference I can see is that the domain is uppercase here - but I can drill into it and select the group, so I think this is probably not causing an issue.
I added myself as a new entry as you suggested:
However, I still get an IP address from the 10.7.2. range.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:45 AM
you have added yourself with domain info. dont select yourself from the list, just type it in and ignore name in list. just click whitespace and it will stick.
- Mark as New
- Subscribe to RSS Feed
- Permalink
09-12-2017 07:58 AM
Tried that, it just shows sfordham, but I still jump down to the Corp entry.
- 1 accepted solution
- 22355 Views
- 46 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Can we create a custom log forwarding to syslog server for PAN OS greater then 11.0.0 in Panorama Discussions
- ADEM Shows Gaps In Synthetics Trends in General Topics
- Semi-Disable Global Protect on Mac in GlobalProtect Discussions
- Issues with Norton 360 in GlobalProtect Discussions
- Information about Palo Alto Software upgrades via SCM in Strata Cloud Manager