- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to tune wildfire rules
- LIVEcommunity
- Discussions
- General Topics
- Re: How to tune wildfire rules
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How to tune wildfire rules
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-05-2013 08:55 AM
I am on a PA2050 using 4.1.12 in Device/Setup/Wildfire I have Wildfire enabled. In Objects / Security Profiles / File Blocking I have rules that "ALERT" and "FORWARD" on certain file types.
My rule base for USERS connecting to the INTERNET consists of rules that allow certain AD groups access to certain PROFILES. These profiles include data filtering, antivirus, and URL FILTERING.
The problem I have is that Google Maps and Google Earth generates a very large number of alerts due to all the archives sent to the browser. Much of this traffic is determined to be ZIP by the Palo Alto. I would like to exclude Google Maps and Google Earth files from alerting on ZIPs, though I don't want to stop alerting on other Google Services.
Attached is a screen shot of this traffic. If I can figure out how to do this with Google Earth and Google Maps then there are some other platforms I would like to exclude.
Can what I ask reasonably be done?
- Labels:
-
Set Up
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-05-2013 09:12 AM
Create a new security rule above the rule where your file blocking profile is currently catching the Zip files. In this new security rule, allow only google-maps and google-earth. From here, you can do a few things. 1.) you could opt not to attach any file blocking profiles to these two applications, or you could create a customized file blocking profile that does not include ZIPs.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-05-2013 10:02 AM
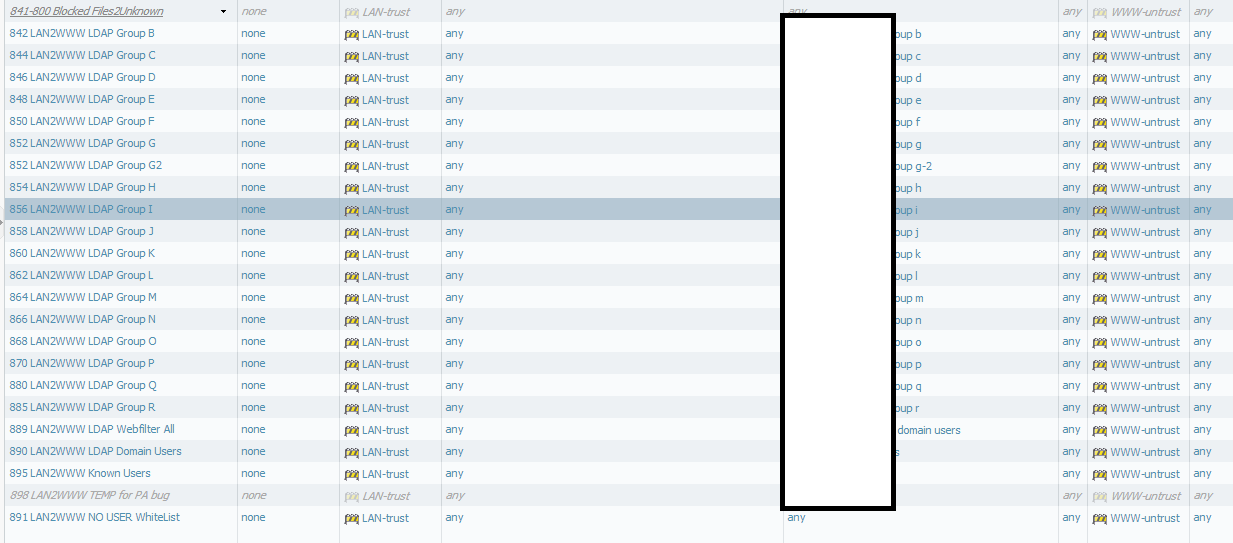
Attached is a small section of my rules. These rules have profiles associated with them which include URL filtering, Data filtering, and so on. Some groups have Google Earth, Google Maps, both, or none.
If I stick a rule above all these rules which allows Google Earth and Google maps, then I'm breaking my URL filtering as the allow rule would allow this traffic regardless of what the subsequent rules state.
I would need to duplicate every single one of these rules that allow Google Earth and/or Google Maps and set the top duplicate rule to allow the platform without data filtering, correct?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-05-2013 10:16 AM
The file blocking profile is applied per-rule. So, if you wish to use a different file blocking policy for some apps (google-maps, google-earth) than other apps (gmail, web-browsing, ssl, anything else), then you must separate out their traffic into different rules. Yes, in your case, you could duplicate each group's security policy rule, modify the application to be goggle-maps and/or google-earth) use a different file blocking profile just for those two apps.
- 6389 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Root Partition Full in Next-Generation Firewall Discussions
- Help me understand wildfire please!!! in General Topics
- Use Auto-Tagging to block failed Global Protect login attempts in GlobalProtect Discussions
- XDR analytics (AI/ML) model maturity in Cortex XDR Discussions
- error: azure marketplace vm-series do not bootstrap in VM-Series in the Public Cloud




