- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
IKE SA negotiation is started as initiator, non-rekey
- LIVEcommunity
- Discussions
- General Topics
- IKE SA negotiation is started as initiator, non-rekey
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
IKE SA negotiation is started as initiator, non-rekey
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 12:36 AM
Hello :),
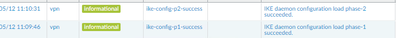
I have a problem with VPN from PA-220 to Azure. The logs show this information : "IKEv2 IKE SA negotiation is started as initiator, non-rekey. Initiated SA "
Every change I made it always is this same error. Is there any way to resolve this issue ?
Thanks in advance 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 01:20 AM
Hi @Lukaszm1 ,
The log you have shared doesn't contain any error. It indicates that FW is trying to negotiate Phase1. The key point here is that FW is starting the negotiation ("as initiator"), due to the nature of the IPsec the initiator will not log the real reason why negotiation is failing.
You can try to enable passive mode under the IKE Gateway advance options - this will force the firewall to act only as responder and waits for the Azure to trigger negotiation. That way you should see more "detailed" log what could be the reason for the unsuccessful negotiation. Note that in thi case you need to find a way to tell Azure to start first - either by sending traffic from azure to on-prem network or by any "azure troubleshooting commands".
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 03:14 AM
Hi ,
Thanks for fast replay , i try this but still no luck, It is also very strange i have this same configuration on different location and it works without any problems.
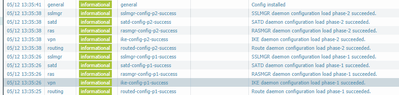
After change the ike to passive i have this information in logs :
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2021 06:51 AM
Hi @Lukaszm1 ,
These logs are not related to the VPN negotiation, but rather with configuration commit.
If you have enabled passive mode on the FW and you don't see anything else it probably means Azure is not even trying.
If you don't have a way to force Azure to start negotiation, you can disable again the passive mode and run packet capture for IKE packets on the FW. Under CLI run:
> debug ike pcap on (this will capture any ike packets so if you have other tunnel already running in this fw it will capture them as well)
> debug ike pcap view
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-13-2021 11:18 PM
Hi,
Thanks again, I found what was the problem, I make a mistake in polices and there was a bad ip address on it to the azure ;/ .
No it is working 🙂
Thanks ! 🙂
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-23-2021 10:54 AM
Hi @Lukaszm1,
I'm having the very same issue,
What do you mean by "there was a bad IP on it to azure"?
Thanks!
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-23-2021 09:42 PM
Hi @bcalderon
Check the configuration on the Policies there should be entry with information that You allow the connection from Your WAN ip address to the other site IP Address.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 06:41 AM - edited 06-24-2021 06:49 AM
Hello @Lukaszm1
So a Security Policy could prevent the establishment of phase 1?
I thought a policy could affect the traffic flow between zones, but once the tunnel was up and running...
Thanks, going to check that
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-24-2021 09:58 PM
Hello @bcalderon
In My case it do the job, after add proper ip address it established with no problem. Try to do that and see what happend. On the application add " ike and ipsec" it should be enough to have more granular control.
- 53408 Views
- 9 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto Site to Site VPN ipsec tunnel up but unable to ping Source to destination in Next-Generation Firewall Discussions
- PA1420 HA Mode stucks in Initial (HA Initializing) mode for too long in General Topics
- StoreDesktopExtension.exe - Again alerts are generated in Cortex XDR Discussions
- How to make Router BGP ping into IP inside Palo Alto in Next-Generation Firewall Discussions
- Failed to initiate Plugin Phase1 commit in Panorama Discussions