- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Is SSL decryption (inbound inspection) possible between 2 internal zones (subinterfaces)?
- LIVEcommunity
- Discussions
- General Topics
- Is SSL decryption (inbound inspection) possible between 2 internal zones (subinterfaces)?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2013 11:01 AM
Hello Harry,
Yes you are right. Currently do not support decryption of TLS1.2. TLS 1.2 hasn't be broadly supported by browsers until more or less practical TLS 1.0 and block cipher related attacks where demonstrated by cryptographers as proof of concept code. We do see a slow increase of TLS 1.2 support in major browsers lately. Especially Google Chrome and Apple Safari support in their standard configuration now. Since PANOS 5.0, if we detect a TLS1.1 or TLS1.2 session, we first try to downgrade it to TLS1.0 and decrypt. If that fails, we won't decrypt the session and either drop the session or allow it encrypted based upon your policy settings.
Thanks and regards,
Kunal Adak
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2013 08:01 AM
Hello hemarsys,
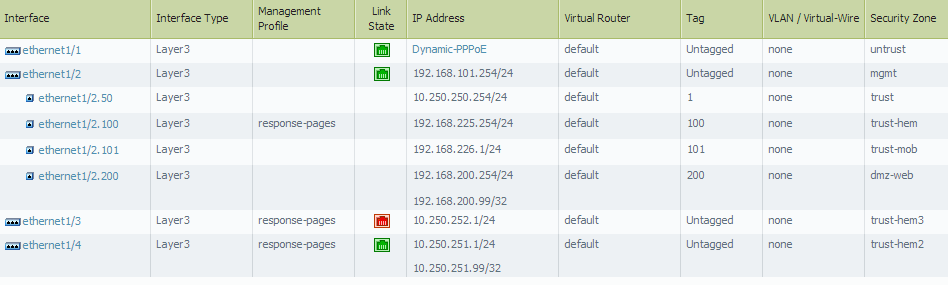
Yes, you should be able to perform decryption in between internal zones with sub-interfaces. We would just treat them as two separate layer3 zones while creating a decryption policy for inbound inspection.
Some documents that might help you:
How to Implement SSL Decryption
How to View SSL Decryption Information from the CLI
Difference Between SSL Forward-Proxy and Inbound Inspection Decryption Mode
Hope that helps!
Thanks and regards,
Kunal Adak
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2013 10:49 AM
Thanks, I found out that it was not working by TLS 1.2.
If I disable in the browser the option "use TLS 1.2 " then it works.
Hopefully TLS 1.2 is supported soon.
Regards,
Harry
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-14-2013 11:01 AM
Hello Harry,
Yes you are right. Currently do not support decryption of TLS1.2. TLS 1.2 hasn't be broadly supported by browsers until more or less practical TLS 1.0 and block cipher related attacks where demonstrated by cryptographers as proof of concept code. We do see a slow increase of TLS 1.2 support in major browsers lately. Especially Google Chrome and Apple Safari support in their standard configuration now. Since PANOS 5.0, if we detect a TLS1.1 or TLS1.2 session, we first try to downgrade it to TLS1.0 and decrypt. If that fails, we won't decrypt the session and either drop the session or allow it encrypted based upon your policy settings.
Thanks and regards,
Kunal Adak
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-23-2014 01:29 PM
In PAN OS 6 SSL decryption of TLS 1.2 seems to work with Internet Explorer but with Google Chrome and FireFox currently not.
Is this correct?
Regards,
Harry
- 1 accepted solution
- 3603 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- web file blocking in Next-Generation Firewall Discussions
- Action of allow but of Type policy deny in General Topics
- For those that seek to get SSH Proxy working in General Topics
- Global Protect / Vodafone / Germany in GlobalProtect Discussions
- SSL No-Decrypt issues in Next-Generation Firewall Discussions