- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
no decryption policy set, wan to wan traffic decrypt is yes
- LIVEcommunity
- Discussions
- General Topics
- no decryption policy set, wan to wan traffic decrypt is yes
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2023 11:47 PM
Hi All ,
We did not set decryption policy
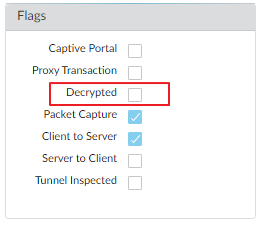
But in the threat log, it is seen that decrypt is yes, and the traffic is wan to wan.
Under what circumstances will the log of wan to wan decrypt is yes be generated?
thanks
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-19-2023 09:36 AM
Just to be abundantly clear, the only time that traffic is automatically decrypted by the firewall is if the traffic terminates on the firewall. So in the example of a GlobalProtect Portal/Gateway, that traffic will be decrypted automatically without anything being configured by you as the admin.
In the event that you have a device setup in your WAN/untrust zone outside of the above examples, it won't be automatically decrypted by the firewall unless you setup a decryption policy. For example if I hand a VPN concentrator off of a firewall and just place it in a WAN/untrust zone, the firewall won't automatically start decrypting that traffic.
That might add a bit of confusion as this isn't a common deployment that folks do, but it's important to have that distinction present.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-18-2023 11:50 PM
If ssl session is terminated on wan interface, for example; globalprotect portal, it will be wan2wan session and also decrypted.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-19-2023 12:06 AM
Hi Emr
Want to confirm if my understanding is correct
As long as the ssl 443 session from wan to wan ends on the wan interface, it will be decrypted by default on the PA. If it is a threat, it will be blocked, right?
Is there any other possibility besides ssl .
thanks
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-19-2023 12:51 AM
yes to first part.
the action (blocked you said) depends on your configuration. If you configure it to be blocked, you are correct.
If you are pointing this decryption, this indicates ssl decryption was applied to the ssl / tls session
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-19-2023 09:36 AM
Just to be abundantly clear, the only time that traffic is automatically decrypted by the firewall is if the traffic terminates on the firewall. So in the example of a GlobalProtect Portal/Gateway, that traffic will be decrypted automatically without anything being configured by you as the admin.
In the event that you have a device setup in your WAN/untrust zone outside of the above examples, it won't be automatically decrypted by the firewall unless you setup a decryption policy. For example if I hand a VPN concentrator off of a firewall and just place it in a WAN/untrust zone, the firewall won't automatically start decrypting that traffic.
That might add a bit of confusion as this isn't a common deployment that folks do, but it's important to have that distinction present.
- 1 accepted solution
- 3891 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Decryption policies and Short-Lived Certificates in Next-Generation Firewall Discussions
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- Question about ECH and its effect on URL filtering (without decryption) + how to block it in General Topics
- Prisma Access Explicit Proxy — Anti‑Spyware behavior when DNS bypasses Prisma (logging subtype + test methodology) in Prisma Access Discussions