- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
possible to know what triggered malicious website classification on my website?
- LIVEcommunity
- Discussions
- General Topics
- Re: possible to know what triggered malicious website classification on my website?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
possible to know what triggered malicious website classification on my website?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-23-2023 06:32 PM
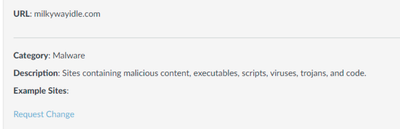
I run a small website (www.milkywayidle.com) which is an online game ran directly in the browser. after a few recent updates around 2-3 weeks ago, I saw noticed that https://urlfiltering.paloaltonetworks.com/query/ classified my website as malicious. I requested reclassify and it quickly classified to "game". However around the same time many users complained about their ISP (Spectrum, Xfinity) security shield which is part of the router their ISP provided them also started classifying my website as malicious and blocked them from access. I'm able to contact them and it gets temporarily whitelisted, but every time I make an update (even tiny updates) to the website, it gets blocked again.
I looked at a lot of other website scanners/classifiers online and nothing else classified my website as malicious. I'm wondering if it's possible to learn what triggered the malicious content classification from PAN since it could be related to the ISP false positives as well.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2023 12:07 AM - edited 03-24-2023 12:13 AM
Maybe ask again why Palo Alto is doing this by using the webform for reclassify as they should send you email update.
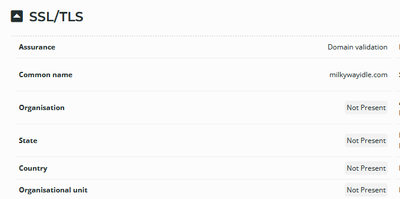
From checking your site with the link below I see that your site is new and maybe this adds to Palo Alto and other systems monitoring for changes. Also your SSL cer is not organization verified just domain verified, so maybe increase the SSL security and it could get better clasification.
Also there is some data that you may like to hide as I see that you have a "Server" response header and this better be removed.
This is what I can tell as maybe other people have better ideas.
https://sitereport.netcraft.com/?url=https://www.milkywayidle.com
Also in AWS you can add also a WAF product before your site as maybe if Palo Alto sees some vunrablity maybe from the https://www.exploit-db.com/google-hacking-database it will not like it. You can scan your site with https://www.qualys.com/free-services/ as they have a free web scanner community edition that may give you some ideas.
It is interesting what bad category was your site added to as this may provide extra info.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2023 12:29 AM
Thanks for the suggestions. I will try some of these and see if it will help. I actually asked about it in the additional notes for reclassify, but all I got back is a generic response that it did get reclassified.
The main thing that is odd is that the site was fine for over half a year without any of these issues. The only significant change I made 2-3 weeks ago was combining all of my website SVG assets into a number of sprite files (which seems fairly benign in terms of security concerns). Nothing in terms of SSL or server responses were changed.
I added images for the classification results from before, but it doesn't give too much detail.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2023 12:56 AM
Strange your SSL cert says "Not valid before 21.02.2023", so for me this suggests it is a new ssl cert but you say that you did not renew it. Maybe it was autorenewed and this could have caused the issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2023 02:21 AM
I originally created the certificate sept 25 2021 on AWS certificate manager. I did not manually renew it, so I guess AWS did auto renew it.
Are you suggesting that there could be issues simply because the SSL cert is new? or that there may have been some problem with the renewed SSL itself?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-24-2023 02:41 AM
Can't give 100% that this caused the issue but many ML engines will monitor such a thing when evaluating sites. Maybe the SSL change lowered the score then your file change may have lowered it even more.
Other than that if you have a licensed palo alto firewall you can ask a user to access your site and have a security rule for that user by matching source user or ip address and see if the palo alto wildfire/antivirus/vunrability profiles will block you when accessing the modified files as they may trigger a bad false positive signature and then you may submit to https://live.paloaltonetworks.com/t5/virustotal/bd-p/VirusTotal_Discussions the false positive. If a user was blocked by the security profiles and the palo alto firewall was providing telemetry to the Palo Alto cloud , this could explain why palo alto marked the website as "Malware" that suggests that the modified files triggered antivirus or wildfire protections for files. Also configure the Palo Alto antivirus and wildfire profiles to scan your sprite file types (https://docs.paloaltonetworks.com/wildfire/10-2/wildfire-admin/wildfire-overview/wildfire-file-type-... ). Palo Alto may have already fixed this with the latest content updates for antivirus signatures, so keep that in mind.
That is what I can provide you as input for this issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
01-28-2024 01:00 PM - edited 01-31-2024 01:43 AM
I had similar problems when I used unverified online gambling sites. However, everything changed after I read this review https://topcasinosreviews.in/minimum-deposit-casinos/ about an online casino that offers excellent terms of use. I liked that on this gaming platform you can start with a minimum deposit, and this significantly reduces the risk of losing a large amount of personal funds. I believe that the immersive experience and evolving technology make it more than just a pastime; it is a modern form of entertainment.
- 11493 Views
- 6 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to request review of residual High-Risk rating when category dispute has been resolved? in General Topics
- How to Handle High-Volume Email Events in XSOAR Without Overloading the System in Cortex XSOAR Discussions
- Request to Remove High-Risk Status and Update Website Category for ice-aec.com in General Topics
- After pushing content from Dev to Prod, we are seeing lot of errors in XSOAR in Cortex XSOAR Discussions
- Masquerading - 4203898100 in Cortex XDR Discussions