- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Secure web-GUI access for managment
- LIVEcommunity
- Discussions
- General Topics
- Secure web-GUI access for managment
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Secure web-GUI access for managment
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-23-2020 10:24 PM
Dears,
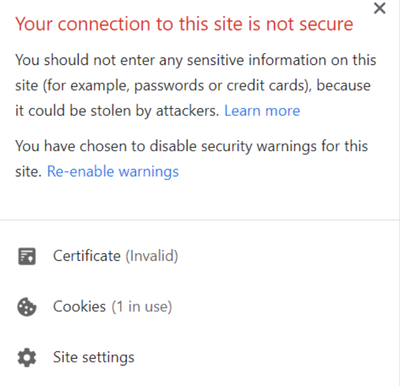
When i log in my firewall it is showing the connection not secure.
For secure connection login, i have gone through these documents and try to configure a secure connection for web GUI access.
How To Configure A Certificate For Secure Web-GUI Access - Knowledge Base - Palo Alto Networks
Procedure 1 I followed:-
- Created a self-sign certificate with a common name management IP address.
- Created an SSL/TLS profile and attached the self-sign certificate in SSL/TLS profile
- Then Device>Setup>>management>general setting > Attached the same SSL/TLS profile and commit.
- Export the self-sign certificate in import in client machine trusted root certificate store.
- Tried to login into the firewall in a different browser.
Procedure 2 i followed:-
- Created a CSR request and the certificate sign by internal CA.
- Import the certificate in the firewall.
- Created an SSL/TLS profile and attached the newly imported certificate in SSL/TLS profile
- Then Device>Setup>>management>general setting > Attached the same SSL/TLS profile and commit.
- Export the certificate in import in client machine trusted root certificate store.
- Tried to login into the firewall in a different browser.
I tried two both above procedures but still, I am facing the connection, not a secure error.
Can anyone help me with this.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-23-2020 10:44 PM
@Jafar_Hussain Your screenshot shows you are accessing it by IP, instead you should be accessing it by the common name you have set while creating cert.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-24-2020 09:17 AM
If i am not wrong it should be a dns name and not IP in there although it doesn't stop you from entering IP
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-24-2020 04:00 PM
For procedure 1, if you use a firewall self-signed cert for the web management, you're workstation won't trust that cert unless you import the firewall CA certificate on to your workstation.
For procedure 2, you don't need to export/import the device certificate. If your workstation trusts your internal CA, then your workstation will trust any certificates issued by that internal CA wherever they are installed.
What's the message if you click on 'Not secure'? It will usually point you in the right direction for troubleshooting. What does the subject and subject alternative show in the certificate details?
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-25-2020 01:55 AM
For procedure 1, if you use a firewall self-signed cert for the web management, you're workstation won't trust that cert unless you import the firewall CA certificate on to your workstation. - installed the certificate on the workstation but did not work.
For procedure 2, you don't need to export/import the device certificate. If your workstation trusts your internal CA, then your workstation will trust any certificates issued by that internal CA wherever they are installed.- OK got it.
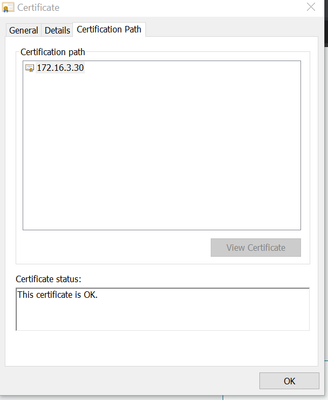
when I use a self-sign certificate and try to login in to the firewall. the below error is showing.
but when i check the certificate it is showing OK.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-30-2020 12:17 PM
Did you create a certificate authority on the PA and then use that to issue the device certificate? The root certificate from the PA would need to be imported into your local machine's certificate store, not the device certificate. For the device certificate to be trusted by your PC, the root that issued it needs to be trusted.
For actually generating the certificate, you'll probably need to use an actual name as the CN, not an IP address. Most authorities won't issue with an IP address as the CN. If you want to include the IP as a valid entry, create it as a SAN entry on the cert using the IP field. You should also include the CN in the SAN entry as well.
Try this:
Create a root authority on the PA: https://docs.paloaltonetworks.com/pan-os/8-1/pan-os-admin/certificate-management/obtain-certificates...
Export this root certificate and import to the trusted root store on your computer.
Generate a device certificate on the PA signed by the root you just created:
Common name: firewallname.company.com
Attribute Hostname: firewallname.company.com
Attribute Hostname: firewallname
Attribute IP: 172.16.3.30
Then assign this cert to your SSL/TLS profile.
- 11658 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA-445 lost management access in General Topics
- Enterprise email had not been allowed to access Strata Cloud manager pro link and common services in Strata Cloud Manager
- How do I check license usage in Prisma Access Panorama Managed? in Prisma Access Discussions
- Prisma Access Strata Cloud Manager - Push Failed in Prisma Access Cloud Management Discussions
- AZURE Entra MFA for admin access via CLI in Next-Generation Firewall Discussions