- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Services
- LIVEcommunity
- Discussions
- General Topics
- Services
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Services
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 08:33 AM
Is there anyway in the traffic monitor, or the ACC or any other logs to see what services are being hit? I can see applications but not specifically services though to can add specific services in the rules
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 09:07 AM
Not that I'm aware. You could just modify the port information since that essentially will determine the service; but the PA being application base the end-goal would really be to app-id all traffic and create custom app-ids where needed.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 09:19 AM
By service you mean destination port?
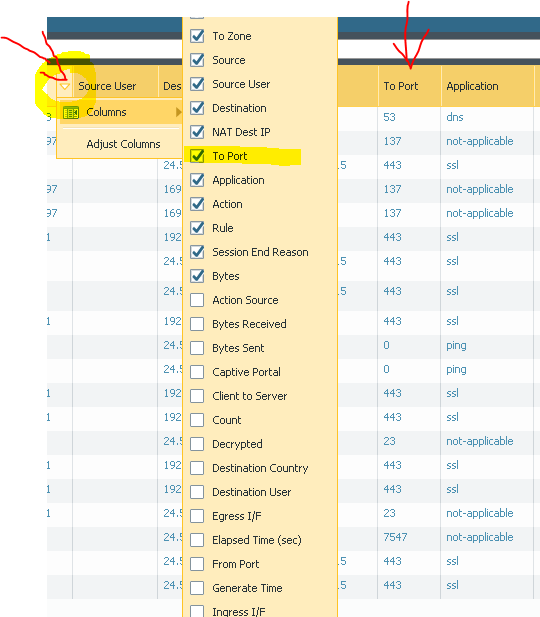
If yes then just add this column into Monitor > Traffic view.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 09:49 AM
no I mean services, I have it set to show my port in my traffic monitor already, but I want to be sure what palo alto is defining as services since they give the option to add it in their rules I was surprised there was no option to filter by services
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 10:32 AM
Service field under Policies > Security and is just destination port number.
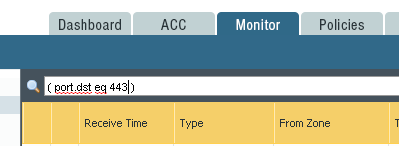
If you want to filter traffic in Monitor > Traffic then just use filer.
For example filter below will show traffic towards port 443
( port.dst eq 443 )
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 10:34 AM - edited 04-24-2017 10:35 AM
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:06 AM
Okay
So if I have the application web-browsing or http are they alway port 80
or if I have https or ssl are they always port 443
I guess I am curious why it is interchangeable to either use the application or the the port
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:15 AM
If you create policy to allow tcp/80 then this will allow any application that is capable of running over port 80 (even Skype).
If you allow application web-browsing and service application-default then web-browsing can run only on default port.
Now if you need to access website that runs on some random port then you need to create policy where application is web-browsing and service is destination port you need.
Good example is if you decrypt SSL.
In this case first you need to permit SSL on default port that is 443.
Now if Palo removes decryption then inside SSL there is web-browsing.
But on what port it runs on? 443
So you need dedicated rule to allow web-browsing on tcp/443 as 443 is not in default list of web-browsing application.
So service is just port number.
Application is Layer 7 application identified by the firewall.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:31 AM
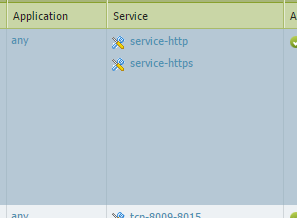
Thats was a greate response Radio so what do you think is going on in this example that is from a reul on my firewall
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:40 AM
Under the applications tab under objects every application will list the 'standard' ports that the application will utilize. In the case of web-browsing then yes the only port allowed is tcp/80; SSL only lists tcp/443; SMTP will list tcp/25,587.
The application and port/service settings are not really 'interchangable', yes SMTP will function fine if I open tcp-25 but then anything else could also potentially use tcp-25.
A better example would be something like a large SQLenvironment where I have a large amount of non-standard ports open for the different database connections; in this case I will specify the application as mssql-db/mon depending on the connection and then specify a custom service for something like tcp-64280 or tcp-63180. Obviously I don't want every single application that could use these ports to actually be allowed, so as long as I have mssql specified I can rest realatively easy knowing that only the sql connections will actually be allowed. If you simply allow the service and specify 'application any' then you are missing the vast majority of the advantages that come with a Palo Alto firwall.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:43 AM
If you go to Objects > Services you can see that service-http includes ports 80 and 8080 by default and service-https includes port 443 by default.
With this rule you allow any application to run over those ports.
If you check Objects > Applications and search for 80 it shows 1435 and 443 it shows 1137 applications that Palo identifies and that uses this specific port.
All of them are allowed.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:45 AM
I'll generally have this rule included from my Trust to Untrust zones with an application deny rule in front of it. Any application that I specifically don't want to be allowed outside of my network will simply be placed in a deny rule above on that looks like this; as long as the traffic doesn't match the deny rule then it simply gets allowed through the network.
It's a simple way to allow anything but specifically denied traffic to the outside. Now if this wasn't from my trust to my untrust zones and this was allowing traffic to access devices located in my trust or dmz zones then it would be an issue.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:46 AM
You're either just really quick today or I need to stop trying to drink this coffee while replying to posts 😉
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:50 AM
So in the example I sent you, that rule is allowing every application that can use http and https not just web browsing and ssl. I did not create this rule so I guess I need to figure out why they chose to do http and https instead of the web-browsing and ssl applications
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-24-2017 11:52 AM
Great information of all of you even though Raido seems to be posting faster than Bpry LOL
- 10538 Views
- 26 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Enable user context cloud service in IoT Security Discussions
- Panorama continuously pulling expired Strata Logging Service License in General Topics
- Google Playstore rule allowed services in General Topics
- Migrating Cisco multi-contexts into one vsys Palo Alto firewall in General Topics
- Continuous Threat Logs Showing Management Server IP as Source in Next-Generation Firewall Discussions