- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
User-ID
- LIVEcommunity
- Discussions
- General Topics
- User-ID
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
User-ID
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2017 03:14 AM
When enabling user-id where does it check against to get the information to identify the users? I have it turned on for serveral zones and it only seems to work on the VPN user-id's.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2017 04:14 AM
You can use the security log of you’re domain controllers.
Check device, User Identification. I prefer using the User ID Agent and point the Palo Alto to this agent.
There are also scripts available to get the users from a radius log.
Good luck!
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-29-2017 05:42 AM
Hi @jdprovine,
This guide should be very helpful :
Cheers !
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2017 05:28 AM
That is what I was thinking too Mick, we authenticate against LDAP instead of AD and I was wondering if the PA only does the userid against AD
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2017 05:40 AM
i have never tried with LDAP but i'm sure its something to do with the PA being only able to read LDAP groups and not LDAP attributes that some LDAP admins use instead of groups.
below is a link explaining this issue and a possible workaround.
it may not help you but at least give you a better understanding of whats going on.
Mick.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2017 06:09 AM
So the PA does do it userid queries only against AD
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2017 07:04 AM
Hi @jdprovine
There are many methods to collect User id information: reading Active Directory authentication logs, server sessions (drive maps), API scripts, Captive portal, syslog collection, TerminalServer sessions, GlobalProtect authentication,...
Please check out this article that highlights most of the main ways to collect user identification information and how to set it all up:
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2017 07:09 AM
well i have only briefly browsed the document but my assumptions are as follows.
if your PA identifies its users via authentication, such as your VPN then you can use LDAP groups against those users for policies etc.
the previous link explains how to do this. but...
if your users do not auth via AD then you will not be able to map IP's to users as the LDAP server will not hold a database of user related IP's.
The PA user-id reads the security log on AD as this records users addresses when they use domain services, email, logon etc.
so I would say yes to your previous post.. But.. (again)
the user-AD agent installed seperately has config settings for EDirectory.. as wll as AD.
Mick.
oops! someone has just posted previous to me so may be of better use.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2017 07:11 AM
the document I refer to is the one i posted earlier, not the one from @reaper.
sorry for the confusion....
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-01-2017 09:11 AM
Hello,
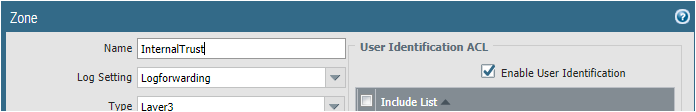
Also check to make sure that the User-ID is enabled on the zone. Its burned me a few times over the years.
Cheers!
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2017 09:45 AM
Do you have to have a certain version of the userid agent for different OS's of the PA? I don't want to have to upgrage the agents every other month unless it does it automagically
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2017 10:32 AM
No, i have used same agent for all 7.x versions, only had to upgrade when moved to v8. As requires a device cert.
however v8 had other issues so rolled back to v7 and original agent.
we have 2 agents so upgrading (if required) can be pretty seemless.
- 15243 Views
- 42 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- GlobalProtect Name Normalization issue in GlobalProtect Discussions
- Prisma Access CIE and User-ID mapping not working for groups in Prisma Access Discussions
- UserID periodic empty groups issue in General Topics
- UserID Redistribution Filters working weirdly in Next-Generation Firewall Discussions