- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Wildfire submission log
- LIVEcommunity
- Discussions
- General Topics
- Wildfire submission log
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Wildfire submission log
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2019 06:25 PM
I don't understand wildfire work.
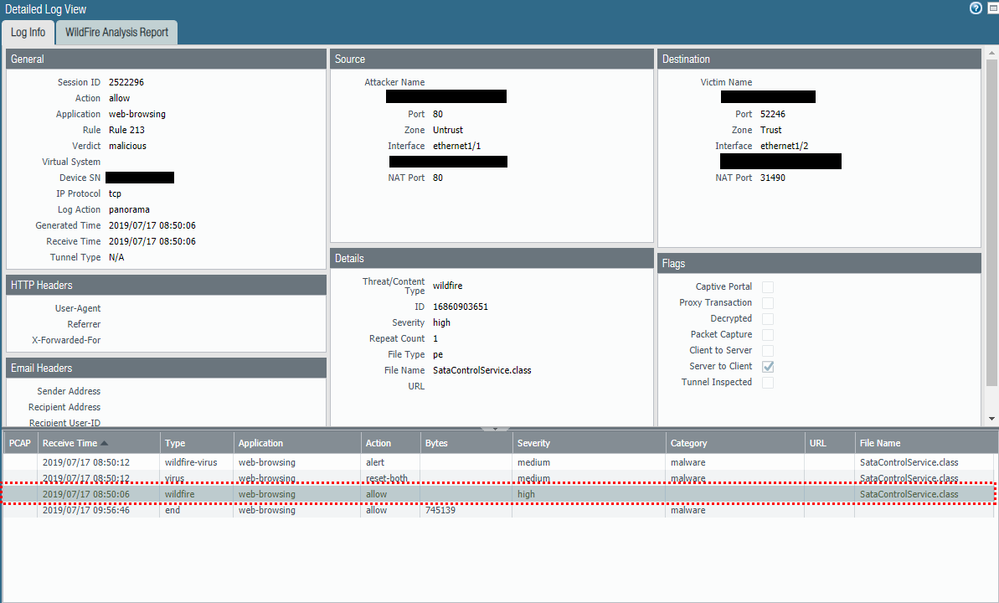
I have this example that Firewall had wildfire-virus signature but was created wildfire submission log before wildfire-virus identification
why?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-18-2019 08:40 PM
Wildfire is for zero day attacks so it looks like there is not an existing verdict for this PE file at the time. Therefore, the firewall has to send the file to Wildfire servers for detonation and analysis. Subsequent logs show that Wildfire determined it to be malware and reseted the connection. Future detection of this same PE file should result in the same action taken, reset-both.
Out of curiousity, is it possible to get a MD5 hash of this file?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-19-2019 06:55 AM - edited 07-19-2019 08:56 AM
Hi @allee
I think firewalll already had wildfire-virus signature when wildfire submission log was generated
unknown sample is uploadd when there is no virus signature. is it right?
as you see detail log The Receive time interval between two logs is 6 seconds.
It's strange to say that the sample was uploaded and installed signature and blocked in six seconds and It is same session.
MD5 is 5cbb230d67b0b0127f369eb3e8288fac
Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-19-2019 02:38 PM - edited 07-19-2019 02:39 PM
@hbshinright. Looking at the logs again, it looks like there was no actual upload to the WF cloud taking place. Threatvault is saying that there is both a Wildfire and AV signature that has been released since last year.
Looking at the 3rd line of the logs, it looks like it matched against the WF signature.
2nd line then matches the AV signature which triggers the reset-both.
- 5789 Views
- 4 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Cortex XDR MITRE ATT&CK v16 -- We're Now on v19. Can We Talk About This? in Cortex XDR Discussions
- Is the unified RPC interface (MonitorDirect.enqueueLogRequest) supported for external use? in Next-Generation Firewall Discussions
- PA 445 setup in Next-Generation Firewall Discussions
- Reset admin cli password of wildfire appliance 500 in General Topics
- Wildfire False Positive on Detection of .XLSX extension in General Topics