- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Workstations no internet after receive IP from firewall DHCP Server
- LIVEcommunity
- Discussions
- General Topics
- Workstations no internet after receive IP from firewall DHCP Server
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Workstations no internet after receive IP from firewall DHCP Server
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-03-2021 02:43 AM - edited 12-03-2021 02:47 AM
Hi,
We have a PaloAlto firewall which is connected to a Cisco switch and on this Cisco swtich an AP is connected.
On the firewall I use ethernet 1/2 port to handle the free wifi clients. This port is in Layer 3 mode.
This port is connected with the Cisco switch. The port on the Cisco switch is configured in access mode and in vlan 5.
On my AP I set the option that the free wifi is connected with vlan 5.
On the firewall my ISP is connected on port 1/3.
On the firewall I have configured the following:
- Ethernet 1/2 is in mode Layer 3 and has IP address 192.168.128.1/24
- This interface is in virtual router internal and in security zone FREE_WIFI
- DHCP server configured on Ethernet 1/2 with these options:
IP pool: 192.168.128.2-192.168.128.254
GW: 192.168.128.1
DNS: 1.1.1.1
I configured the following security rules:
- Deny from zone Free_WiFi to zone Internal_Network
- Allow from zone Free_WiFi to zone Free_WiFi
- Allow from zone Free_WiFi to zone Extern
I configured NAT:
- From zone Free_WiFi to zone Extern
I configured PBF:
- NO PBF for zone FREE_WIFI
I configured the virtual routers:
Internal:
Interfaces: Ethernet 1/2
Static route: 0.0.0.0/0 to ISP and 192.168.128.0/24 next hop 192.168.128.1
Extern:
Interaces: Ethernet 1/3
Static route: 0.0.0.0/0 to ISP and 192.168.128.0./24 next-vr is Internal
The users get an ip address but they don't have internet access.
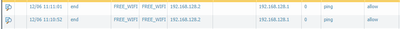
The only rule that is getting hit is Allow from zone Free_WiFi to zone Free_WiFi.
The client always do a ping to 192.168.128.1 and that's it.
When they want to access the internet I see the following in the monitoring:
Source 192.168.128.x to Destination 192.168.128.1 Port 80.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-05-2021 12:16 AM
@ZEBIT wrote:I configured the virtual routers:
Internal:
Interfaces: Ethernet 1/2
Static route: 0.0.0.0/0 to ISP and 192.168.128.0/24 next hop 192.168.128.1
Extern:
Interaces: Ethernet 1/3
Static route: 0.0.0.0/0 to ISP and 192.168.128.0./24 next-vr is Internal
Hi @ZEBIT
You are using 2 virtual routers, on Extern VR you configured 'next-vr' static route from Extern to Internal- this is fine.
But on Internal VR you configured (marked in bold above) an IP next hop of 192.168.128.1 - this is wrong because you are 'trapping' them in their network segment and not telling the firewall where to send packets. This should be:
VR = Internal -> Static Route for 0.0.0.0/0 -> 'next-vr' -> 'Extern'
192.168.128.0/24 is directly connected - no need for a static route.
Shai
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-06-2021 02:13 AM
Hi Shai,
I have changed this, but the only thing that happens when a user get's an ip address is a ping to the default gateway.
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-06-2021 02:41 AM
Hi
All firewalls have 2 default rules - intrazone-default and interzone-default. These are catch all rules at the bottom of the rulebase.
Select one then click 'override' and enable log at session end. Click OK and repeat for the other rule then commit. By default any hit on either rule will not be logged at all.
Try ping & traceroute from a user to 8.8.8.8 to see how the packet flows.
Source-NAT should be happening only when packets egress from ethernet1/3 to the ISP.
If you see more logs now, click the magnifier glass on the left and check the log-details - this will show more info like NAT, ingress & egress interfaces and packet count on the session.
Shai
- 5171 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PAC File for Prisma Access China in Prisma Access Discussions
- How to add Wildcard Domains as a destination for Firewall policy PA1420 in General Topics
- Source and destination is APIPA or Soure is Legit machine and destination to Internet(zone) is APIPA in Next-Generation Firewall Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- pa-450 issues and going down 2 days in a row in General Topics