- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Does Palo Alto IOT include known FQDN domains or Ip addresses for the detected IOT devices?
- LIVEcommunity
- Discussions
- Cloud Delivered Security Services
- IoT Security Discussions
- Does Palo Alto IOT include known FQDN domains or Ip addresses for the detected IOT devices?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-22-2022 05:48 AM
When Palo Alto detects for example the SONOFF devices connect to a known cloud so that the user can manage them as seen in https://sonoff.tech/ewelink/ . In this case when the cloud IoT security detects the sonoff devices will it also load the known list of the FQDN/IP addresses for the SONOFF eWink cloud, so that the IoT admin to know that this is good traffic?
- Labels:
-
IoT
-
IoT Security
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-22-2022 11:47 AM
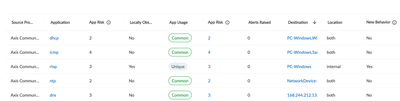
That is a good feedback. We kind of show that under the device profiles section with the intel we gather from the crowdsourced telemetry. Here is a sample where you can see the common/trusted applications used along with the unique applications which are unique to your environment. This ML based behavior verdict helps NetSec in policy creation.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-22-2022 11:24 AM
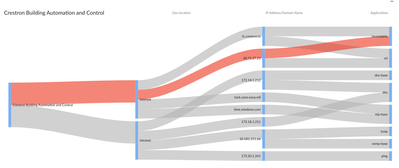
Very good question. Whenever SONOFF devices communicates with the external destinations (FQDN/IP) related to SONOFF eWINK cloud, IoT security shows those device connections part of network usage chart. It helps the admins to visualize and see the destinations and the applications and further helps in creating the least privilege access policies. Sample one for a building automation device for your reference.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-22-2022 11:28 AM - edited 11-22-2022 11:29 AM
Nice! Still maybe for known good ip addresses/fqdn domains there could be detection in the IoT Security portal mentioning that this destination is recommended to be allowed and not blocked as to help admins not block something by mistake 🙂 As this is new product I see this as a possible feature as I thought it will be cool to have it.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-22-2022 11:47 AM
That is a good feedback. We kind of show that under the device profiles section with the intel we gather from the crowdsourced telemetry. Here is a sample where you can see the common/trusted applications used along with the unique applications which are unique to your environment. This ML based behavior verdict helps NetSec in policy creation.
- 1 accepted solution
- 8549 Views
- 3 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!