- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to decode palo alto netflow app-id from hex value
- LIVEcommunity
- Discussions
- Network Security
- Next-Generation Firewall Discussions
- How to decode palo alto netflow app-id from hex value
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
How to decode palo alto netflow app-id from hex value
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-07-2023 08:45 PM
Hi,
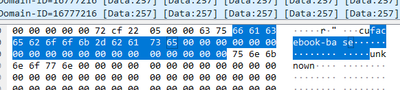
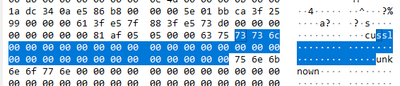
I am sending Palo alto netflow to a Linux server. While I capture NetFlow from the server and open it on Wireshark I cannot see appid in plain text format. I only see the hex code. I have attached some screenshot below here.
Is there any way to decode this hex code to a plain text app-id?
- Mark as New
- Subscribe to RSS Feed
- Permalink
12-21-2023 05:51 AM
Hi @ssovee ,
As mentioned here https://docs.paloaltonetworks.com/pan-os/9-1/pan-os-admin/monitoring/netflow-monitoring/configure-ne... PAN firewall will refresh NetFlow template based on the time interval you specified in the NetFlow server profile.
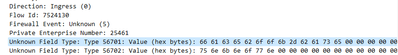
From your screenshare it looks like PAN firewall is already configured to send PAN-OS specific fields, which include App-ID. However wireshark is unable to recognize this field, and suspect the reason for that is your capture didn't capture NetFlow Template packet sent from the firewall.
You can see example here, how WireShark is able to identify all fields when template is being captured - https://helpdesk.kaseya.com/hc/en-gb/articles/115003522631-How-to-view-NetFlow-in-WireShark
- 2194 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Palo Alto 3410 Firewall 100% DP CPU spike in Next-Generation Firewall Discussions
- Security Profile Evaluation in Next-Generation Firewall Discussions
- Byte swapping needed on packet captures taken from tunnel interfaces in Next-Generation Firewall Discussions
- Log messages in ikemgr.log that were present in PAN-OS 11.1 are missing in PAN-OS 11.2 in Next-Generation Firewall Discussions
- Settings from global-template stack not showing on local pan-template but are showing in the template-stack. in Panorama Discussions