- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Digium Asterisk WebSocket Frame Empty Payload Denial-of-Service Vulnerabi
- LIVEcommunity
- Discussions
- Cloud Delivered Security Services
- Threat & Vulnerability
- Digium Asterisk WebSocket Frame Empty Payload Denial-of-Service Vulnerabi
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-06-2020 01:22 PM
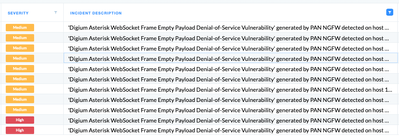
How do I report or provide feedback regarding the Cortex Alert named "Digium Asterisk WebSocket Frame Empty Payload Denial-of-Service Vulnerability" that are being generated by the PAN NGFW, with the Initiator CMD of:
"C:\Program Files\WindowsApps\Microsoft.Office.OneNote_16001.12827.20182.0_x64__8wekyb3d8bbwe\onenoteim.exe" -ServerName:microsoft.onenoteim.AppXxqb9ypsz6cs1w07e1pmjy4ww4dy9tpqr.mca"
We have had this alert generate 9 times since 7 May 2020. Always with the same category of "Vulnerability", same Description "Vulnerability Exploit Detection" and most every time the same CGO of sihost.exe (or possibly another MS Office app such as Excel)
I believe it to be a false positive
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-06-2020 04:16 PM
You will need a packet capture of the traffic in question. Please open a Support case.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-06-2020 04:16 PM
You will need a packet capture of the traffic in question. Please open a Support case.
- 1 accepted solution
- 8618 Views
- 1 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!