- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
external captive portal
- LIVEcommunity
- Discussions
- General Topics
- external captive portal
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
external captive portal
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-27-2014 06:23 PM
I'm thinking about trying something a little out of the square with user-id and captive portal. Let me start with the context and business goal:
- The PAN is deployed as a data centre firewall.
- I'd like to use some policies that permit clients access to an application only if the user is known.
- I'd like to use some policies that permit clients access to an application for specific users only if they have used strong authentication, specifically a Yubico one time password.
- Clients platforms are a mixed environment, BYOD, some active directory but not universal.
Here is how I propose solving the problem:
- use XML-API for the user-id stuff, gather user to IP associations from various authentication logs in close enough to real time.
- Build an authentication portal with business logic to know when to prompt for a one time password in addition to username and password.
- Have the PAN redirect HTTP(S) to this portal when necessary.
So far I've proved the following can work:
- The XML-API user-id stuff.
- Set the 'Redirect Host' parameter in Captive Portal Settings to an IP of a web server.
- Use an appropriate Captive Portal and Security policies to redirect the client and permit the traffic to the web server.
I have not yet coded the user authentication and subsequent redirection back to the intended web page but will be pretty straight forward.
It seems Paloalto have not intended (thought about) captive portal being used in this way. Has anyone else attempted this?
What do you think of this idea? Can you think of a better way to achieve the same goal?
thanks,
Scott
- Labels:
-
User-ID
- Mark as New
- Subscribe to RSS Feed
- Permalink
02-27-2014 06:31 PM
A follow-up question.
It's not clear to me how to configure the PAN so it redirects the client to the captive portal only when the user is not known. Is this possible?
Scott
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-06-2014 03:15 AM
Hi Scott
In regards to your followup question. A session should only be redirected to captive portal if there is no user/IP mapping yet, if such mapping exists CP should not get triggered. are you seeing the opposite ?
your first post should work just fine if you are able to write the redirect after authentication to the original host to facilitate the user and make the authentication trigger the API which should add a user/IP mapping near instantaneously, it should go beautifully
PANgurus - Strata specialist; config reviews, policy optimization
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-06-2014 05:46 PM
Scott,
You also define a Captive portal rule to identify what source and destination address space you want captive portal to be applied to. Remembering that the traffic needs to traverse a firewall interface and only kicks in if there is no user-id to IP address mapping already in the firewall (as tpiens mentions). It works quite well.
Phil
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-19-2014 02:16 PM
Hi Scott,
You could use a PBF rule for "unknown" users. (just not mapped IP with any user) to IP where CP is configured.
Then "your captive portal" have to redirect all incomming traffic to destination 80/tcp or 443/tcp to local address.
The CP shall be in DMZ (traffic to CP shall pass over firewall) - only then PBF works.
Also CP shall be connected to the different L3 interface than LAN and External.
ex. I have:
e1/1 - Internet/External
e1/2 - LAN
e1/3 - CP
PBF have to change a routing for unknown users from default:
User->PAN->Internet
to:
User->PAN->Captive Portal
Rule on PAN:
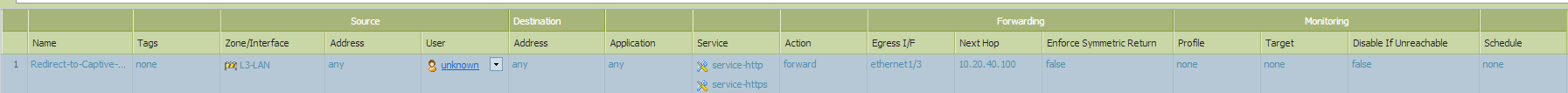
IPtables redirect/DNAT on Linux:
iptables -t nat -A PREROUTING -i eth0 -p tcp --dport 80 -j DNAT --to-destination <IP of Captive Portal>:80
iptables -t nat -A PREROUTING -i eth0 -p tcp --dport 80 -j DNAT --to-destination <IP of Captive Portal>:443
Note: HTTPS redirect could generate SSL warning.
After this you could user XML-API to adding users with timeout value.
There is no idle time as in generic PAN CP, only a timeout.
Setting the Timeout for User to IP mapping Created Using User-ID XML-API
T.
- 4090 Views
- 4 replies
- 1 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Intregate Captive Portal Palo Alto with Aruba clearpass in General Topics
- Issues with Captive Portal / Continue URL Filtering Response page on 10.1.12 in Next-Generation Firewall Discussions
- GP Connection Failed - gateway could not verify the server certiticate of the gateway. in GlobalProtect Discussions
- Problem Using New Digitally Signed Certificate in GlobalProtect Discussions
- Connect Before Logon + Enforce GlobalProtect for Network Access + Captive portal in General Topics



