- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Alert for each time a usb device is plugged
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Re: Alert for each time a usb device is plugged
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Alert for each time a usb device is plugged
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2022 06:42 AM
Hello,
Is there any way to set up an alert for each time a USB device is plugged into a host?
Even if it's not malicious.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-28-2022 02:10 PM
Hi,
Are you looking for USB device plugin alert or alert on activity such as File operation, execution operation via removable media?
USB Device plugin alert may not be possible but definitely you should be able to create a BIOC rule for USB/RemovableMedia file operation, process operation activity with a low severity priority which will only trigger an alert in Alerts Table but not create an Incident.
Will be keen to know if someone has other idea.
KS
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2022 02:19 PM
Hi JoaoSantos20,
In the Restrictions Profile you have the option to configure notifications for Removable Media for file executions launched from external drives attached to endpoints in your network. To configure:
- From Cortex XDR, select Endpoints > Policy Management > Prevention Profiles > + New Profile.
- Select the OS to which the profile applies and Restrictions as the profile type.
- Click Next.
- Enter a Profile Name to identify the profile and Description
- Uncheck Use Default
- Select which option best fits your use case
Notify—Allow the file to execute but notify the user that the file is attempting to run from a suspicious location. The Cortex XDR agent also reports the event to Cortex XDR.
Report—Allow the file to execute but report it to Cortex XDR.
**You may add files or folders to an allow list or block list as well.
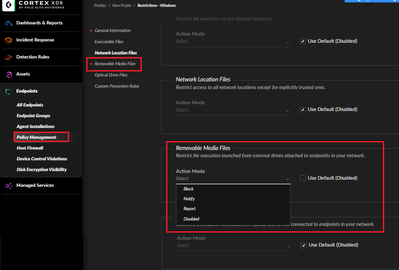
Save and then apply the Restrictions profile to the Security Profiles to Endpoints.
If you already have a Restrictions Profile configured, you may edit and follow steps 5 - 8
You may also create an alert via a BIOC rule from an XQL Query for event logs for Windows and Linux system. For example, an XQL query for the Windows event ID 6416: A new external device was recognized by the system. To build the BIOC rule query through a specific entity:
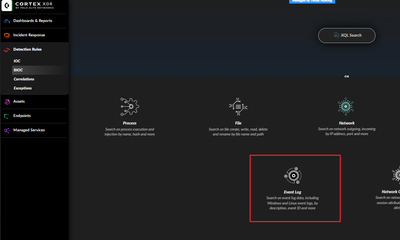
Navigate to Detection Rules > BIOC > + Add BIOC > Select the Event Log Icon
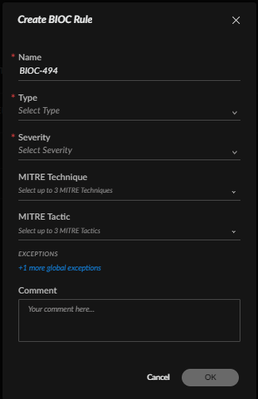
Enter EVENT_ID = 6416 (optional to enter other parameters), Save
Select the Type, Severity, Optional select a MITRE Technique or Tactic to associate with the event, such as Technique - T1092 Removal Media and Tactic - TA0010 - Exfiltration. Enter a comment for tracking, then OK.
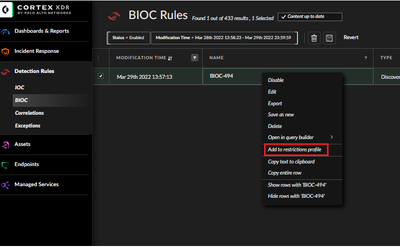
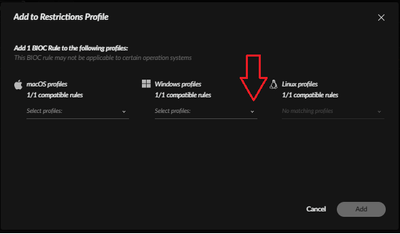
The rule will be displayed in the BIOC Rules table. Right-Click on the Rule to add it to the appropriate Restrictions Profile shown in the sub menu for the endpoints you would like monitored.
Reference
Add a New Restrictions Security Profile (paloaltonetworks.com)
Create a BIOC Rule (paloaltonetworks.com)
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2022 02:42 PM
Hi @jtalton
Pretty cool way of monitoring of removable media activity, i think the only thing which will be required from the endpoint side will be enable event logging for Removable media?
KS
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2022 02:44 PM
Isnt it enabled in windows by default ?
Really good and creative solution from Jtalton.
That deserves likes, isnt it ?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2022 02:50 PM
Thanks... Microsoft TechDoc doesn't specify if its enabled by default Monitor the use of removable storage devices (Windows 10) - Windows security | Microsoft Docs
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2022 03:08 PM - edited 03-30-2022 01:10 AM
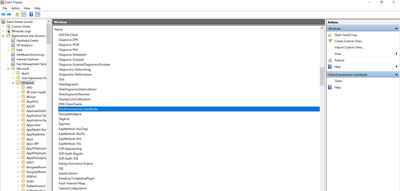
Open windows event viewer and go to
Applications and Service Logs > Microsoft > Windows > DriverFrameworks-UserMode
as shown in the pic1
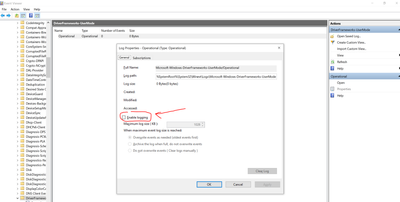
Double click there and you will see the value is 0
Right click on it and select properties. You will find enable logging check box empty. See pic2
I believe it should be possible to propagate this setting through all your endpoints using GPO instead of manually configuring each endpoint.
KR,
Luis
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2022 03:19 PM
Additionally in the registry we see that the enable value is 0 for the registry key
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\WINEVT\Channels\Microsoft-Windows-DriverFrameworks-UserMode/Operational
Changing the value to 1 should also work
KR,
Luis
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-29-2022 11:15 PM
Very interesting solution @eluis @jtalton
I'm referencing this Cortex XDR documentation: https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/endpoint-security/customiza...
Will those Events (6416 & 4719) be collected automatically or would it be necessary to use the Broker VM to collect this additional IDs?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-30-2022 06:26 AM
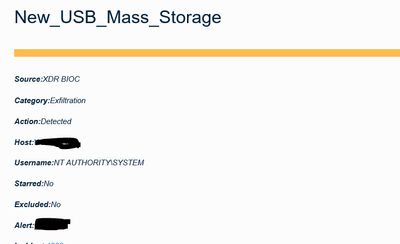
Multiple analytics alerts track USB activities that do not require BrokerVM
A user connected a USB storage device to a host for the first time
A user connected a new USB storage device to a host
A user connected a new USB storage device to multiple hosts
But you are correct, configuring the BrokerVM Windows Event Collector would allow you to specify collection for event IDs 6416 & 4719
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2022 07:25 AM
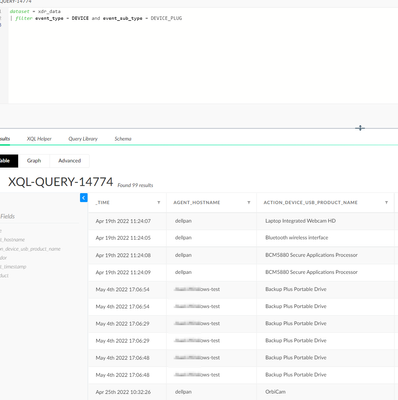
We created a bioc using a reg key
Seems to work
preset = xdr_registry
| filter (action_registry_key_name contains "HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\USBSTOR\Enum" and event_sub_type = REGISTRY_CREATE_KEY)
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-12-2022 07:21 PM
Hi All,
You can also consider using the following BIOC to raise alerts when a USB device is plugged in.
You can play around with the filters to whitelist allowed device IDs/vendors.
- Mark as New
- Subscribe to RSS Feed
- Permalink
08-06-2025 10:43 AM
Hey Bb,
I tried the XQL query as it looked super easy but there are no results. Is something else required to make this work?
- 18083 Views
- 14 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Sending USB Alerts via syslog (Cortex XDR) in Cortex XDR Discussions
- Cortex XDR Device Control Violation Alerts in Cortex XDR Discussions
- Email alert when a device checks in? in Cortex XDR Discussions
- Rare Admin Login in Environment in Cortex XDR Discussions
- Device connection alert in Cortex XDR Discussions