- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Cortex xdr did not detect malware, what good is it?
- LIVEcommunity
- Discussions
- Security Operations
- Cortex XDR Discussions
- Re: Cortex xdr did not detect malware, what good is it?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Cortex xdr did not detect malware, what good is it?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-17-2020 02:41 PM
Cortex XDR did not detect malware, what good is it?
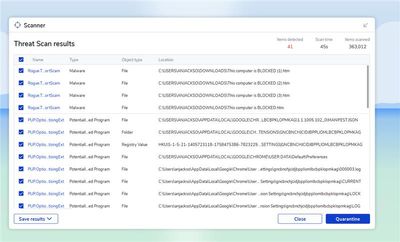
I got this scan with mal warebytes. 41 detected.
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-17-2020 03:13 PM
Hi @SimonTan-
Just curious, did you try to run these binaries or leverage a scan. What enforcement did you specify in your profiles / policy rules? On the malware side there are several checks:
WildFire
- WF Static Analysis
- Machine Learning
- Dynamic Analysis
- Bare Metal
for unknown, the local analysis should do the examination at the point of execution.
In addition to the malware prevention, Cortex XDR includes behavior threat protection, anti-ransomware, password theft protection, child process protection, and approximately 30 ways to exploitation.
If you are using a scan for dormant malware, it is not the same as having all of the different protection levels that are leveraged during point of execution. Are you able to share any hash / artifact info for verification?
David Falcon
Senior Solutions Architect, Cortex
Palo Alto Networks®
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2020 08:50 AM
Hi @SimonTan-
I would actually be happy to set up a Zoom with you to look over your configuration. Based on your screenshot from MB, I believe that you may not have Cortex XDR configured to your needs. For instance, in your screenshot, I see a large number of Potentially Unwanted Applications. These are not malware. Cortex XDR can be configured to treat these the same as malware. On the malware side, I'd be very interested in checking into these as well.
Please let me know if you would like to set up a session.
David Falcon
Senior Solutions Architect, Cortex
Palo Alto Networks®
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2020 10:17 AM
how to retrieve a support file and malware scan log?
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2020 12:26 PM
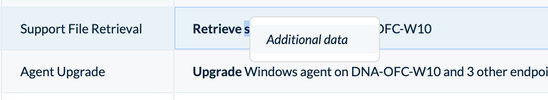
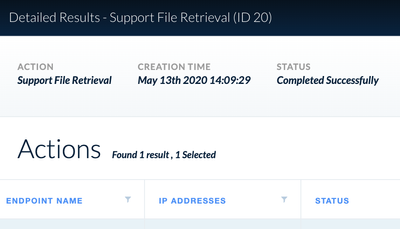
Right click on that entry and select Additional Data.
Once in the details screen, right click on the entry in the list to download the TSF.
David Falcon
Senior Solutions Architect, Cortex
Palo Alto Networks®
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2020 12:28 PM
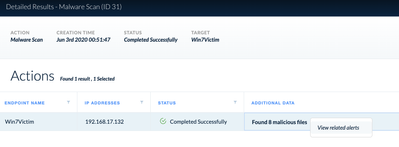
On the malware scan log. Same thing. Right click on the entry within the All Actions interface and select additional data.
From there, locate the entry, right-click and select View Related Alerts.
David Falcon
Senior Solutions Architect, Cortex
Palo Alto Networks®
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-21-2020 12:48 PM
got it, send file to the tech and see what they say.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2022 10:16 AM
Hello , Is there any document or link which can summarise all the protection capabilities of Cortex XDR ? There seem to be many modules/techniques but what is lacking is not all are listed at one place and its difficult to understand how it all works in real world and deliver protection , so list all protection capabilities/modules and give a brief of what each of them achieve .
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2022 10:38 AM
Please take a look at: https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/endpoint-security/endpoint-... and https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-pro-admin/endpoint-security/endpoint-...
Let me know if this helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-18-2022 10:49 AM
Thanks for quick reply , I will refer this surely .
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-19-2022 07:55 AM
Hi @SimonTan,
do not think of CXDR as a regular AV non stop scanning everything, we are not doing that. Even though you can schedule periodic scans we do not recommend to do then daily or frequently. This consumes a huge amount of resources to discover the known malicious files which wont be able to run anyways due to WF, local analysis at exec time, BTP, ... Dangerous attacks usually never come from known hashes
We do check files when the users is going to execute because then, is when the file can turn into a real threat and at this time we discover and stop the unknown as well as the known threats. And at that time we will stop them, and report it to alerts and incidents. Additionally you have a number of actions to do with files afterwards treating them as malware and delete them, quarantine them, allow them if they happen to be benign even the initial behavior was triggered as malicious...
Be confident that with CXDR you will be protected from the known and even much better "from the unknown".
These detections that you showed that were not discovered by CXDR is because the were not scanned by CXDR ? or nobody tried to execute them.
Realize that even if you try a file that goes unknown from a hash check in any AV (CXDR included) when you try to execute it we will analyse at pre-execution and execution time, putting it in context with parent and child processes it might try to create. And whenever we detect something suspicious we will stop/block it and report it on the form of alerts and group them (the related alerts) within incidents for further investigation and incident response.
KR,
Luis
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-02-2022 01:01 PM
How would you setup CXDR to treat PUA as malwares?
KS
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-03-2022 07:36 AM
Hi @KanwarSingh01 ,
Im just thinking fast and on the fly you might think of doing several things:
- adding hashses to block list
- tweaking WF verdicts to malicious if they are triggered to bening or unknown. You might even ask for suex through TAC cases if needed
- If you know or suspect that they are usually dropped at user download folders, ban the execution from that folder (you might even do such with AD GPO)
- Treat unknown as malware
- Check howtos here: https://docs.paloaltonetworks.com/cortex/cortex-xdr/cortex-xdr-prevent-admin/endpoint-security/endpo...
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-03-2022 09:05 PM
Alot of the PUA are considered grayware, there is an option on malware profile
- Grayware—The sample does not pose a direct security threat, but might display otherwise obtrusive behavior. Grayware typically includes adware, spyware, and Browser Helper Objects (BHOs).
As @eluis mentioned, you can manually add the hashes to the block list.
Also you can do restriction profile as an option
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-03-2022 09:48 PM
@eluis and @jcandelaria
I though there might be some other way which i might be missing out for catching PUAs, hence the question. I think I am fine with the discussion, PUAs are never ending topics i.e. every SecOps guy has its own terminology for PUAs and they are not threat to orgs directly and also can never be full proof prevention in stopping all PUAs.
Good example: NSSM.exe (A service wrapper on Windows) is used for service installation of services like ELK on windows but can also be used in an attack for persistence.🙂
Thanks @eluis @jcandelaria
KS
- 14878 Views
- 15 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- How to add exception for known macros detection by cortex XDR in Cortex XDR Discussions
- Cannot add BIOC rule to restriction profiles in Cortex XDR Discussions
- Cortex XDR Pro – Does it scan USB devices upon insertion? in Cortex XDR Discussions
- USB SCANING in Cortex XDR Discussions
- Cortex XDR FIM in Cortex XDR Discussions