- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
How to address CVE-2022-37026 vulnerability in Expedition
- LIVEcommunity
- Tools
- Expedition
- Expedition Articles
- How to address CVE-2022-37026 vulnerability in Expedition
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
on 12-14-2022 10:20 AM - edited on 04-23-2024 06:25 AM by dpuigdomenec
Updated April 23, 2024: adding new repository to get erlang > 25+ packages
Symptoms
Expedition is vulnerable to CVE-2022-37026, below are the Detail about the vulnerability :In Erlang/OTP before 23.3.4.15, 24.x before 24.3.4.2, and 25.x before 25.0.2, there is a Client Authentication Bypass in certain client-certification situations for SSL, TLS, and DTLS.
Diagnosis
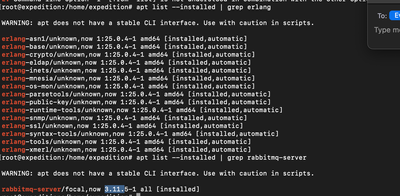
Issue below command in Expedition CLI:
$apt list --installed | grep erlang
the result will show erlang package is v22.x which is vulnerable to the CVE
Solution
Summary: Run below commands in Expedition CLI to add new repositories and upgrade the two packages to the stated version:
rabbitmq-server: 3.11.4-1
erlang: 25.0.4
-------------------------------------------------------------------------------------
// execute below commands as root
sudo -su root
// stop mysql service so Expedition is not available
service mysql stop
// remove any potential version installed
apt-get remove rabbitmq-server && apt-get purge rabbitmq-server
apt-get remove erlang && apt-get purge erlang
apt autoremove
// disable the legacy repository for erlang > 25+ packages
echo "#deb https://packages.erlang-solutions.com/ubuntu focal contrib" | sudo tee /etc/apt/sources.list.d/erlang-solution.list
echo "#deb [trusted=yes] http://www.rabbitmq.com/debian/ testing main" | sudo tee /etc/apt/sources.list.d/rabbitmq.list
// update the apt list
apt update
// add the new repository storing erlang > 25+ packages
add-apt-repository -y ppa:rabbitmq/rabbitmq-erlang-25
// update the apt list
apt update
// add the rabbitmq repository
$curl -s https://packagecloud.io/install/repositories/rabbitmq/rabbitmq-server/script.deb.sh | sudo bash
// update the apt list
apt update
// fix any broken dependency
sudo apt --fix-broken install
// install the rabbitmq-server
$apt-get install rabbitmq-server=3.11.4-1
// remove any unneeded package
$apt autoremove
$apt purge
// start the mysql service to make Expedition available
$service mysql start
Verify the two packages are updated with the required version with below commands:
$apt list --installed | grep erlang
$apt list --installed | grep rabbitmq-server
- 6899 Views
- 0 comments
- 0 Likes
-
address to ip address
1 -
addressgroups
1 -
Administrator's Guide
1 -
App-ID
1 -
attach device
1 -
Authentication
1 -
Best Practice Assessment
1 -
Best Practices
1 -
BPA
1 -
caveats
1 -
checkpoint R80
1 -
connection
1 -
CVE-2021-44790
1 -
Dashboard
1 -
database
1 -
devices
1 -
DNS
1 -
documentation
1 -
edit
1 -
Expedition
31 -
export
1 -
Filtering
1 -
filters
1 -
Gaia
1 -
Google Chrome
1 -
How to
1 -
import
3 -
installer
1 -
Iron Skillet
1 -
IronSkillet
1 -
LDAP
1 -
Logs
1 -
Machine Learning
2 -
migrate
1 -
Migration
2 -
Migration Tool
3 -
Objects & Security Profiles
1 -
one member
1 -
optimization
3 -
panreadorders
1 -
permissions
1 -
php
1 -
policies
1 -
policy
1 -
predefined filters
1 -
project
1 -
queue
1 -
rbac
1 -
roles
1 -
Rule
1 -
search and replace
1 -
settings
2 -
sharing
1 -
srx
1 -
task manager
2 -
Tools
1 -
Ubuntu 16.04 LTS
1 -
Ubuntu 20.04
1 -
users
1 -
Zones
1
- Previous
- Next





