- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
AWS x PAN 2 tunnels PBF backhaul internet static routes?
- LIVEcommunity
- Discussions
- General Topics
- AWS x PAN 2 tunnels PBF backhaul internet static routes?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
AWS x PAN 2 tunnels PBF backhaul internet static routes?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-31-2021 01:13 PM - edited 03-31-2021 01:26 PM
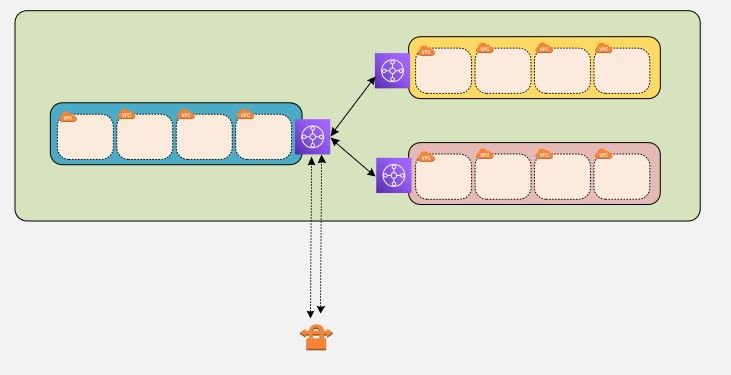
Anyone run into this before? I have 2 x AWS tunnels (No BGP) and I want failover to occur and I want to backhaul internet traffic from AWS out through the PAN. I have connectivity between AWS and on-prem with no static routes configured. However, if I try to backhaul internet traffic from AWS across the s2s vpn tunnel (attached to TGW) it fails. The only way I can get it to work is by adding a static route back to the AWS subnets in my VR. But in doing so that won't allow the traffic to failover via PBF as far as I know. Is that right and if not can someone explain how the correct way to make this work?
Note I use PBF for dual ISP failover to the internet and am wondering if its in the same vein? IE a static route to the backup path and PBF for the primary? So what I am wondering do I need static routes configured in my VR? And if I do does PBF still trump the routing table?
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-01-2021 05:10 AM - edited 04-01-2021 05:11 AM
pbf takes precedence over the routing table of the firewall, but it will not override any routes you added to the VPC
could you include a little drawing or some more info of what you're trying to accomplish ?
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-01-2021 06:31 AM - edited 04-01-2021 06:38 AM
Ok so even if I have static routes for the AWS subnets pointing to tunnel-A and PBF failing over to tunnel-B it should work? Basically I want all traffic to traverse tunnel-A and when that goes down switch over to tunnel-B. Not worried about the AWS side, just the right configuration on the PAN side.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-01-2021 01:54 PM
Hello,
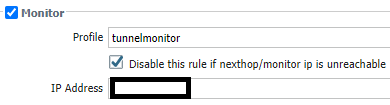
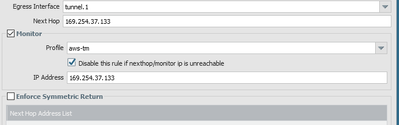
There are several ways to do this. I chose to use PBF and put the tunnels in over. Even PBF reads top to bottom so the first one that is a match, thats where it sends traffic. Also make sure to enable the monitor so the policy is disabled if the tunnel is down, etc.
So for me it was two policies base forwarding policies. The other way would be one PBF and the second a static route down the second tunnel.
Hope that helps.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-01-2021 03:26 PM
correct, but make sure to set a monitor as @OtakarKlier mentioned so the PBF rule can be disabled if the monitor fails, else you will keep hitting the PBF even if it's "broken"
PANgurus - Strata & Prisma Access specialist
- Mark as New
- Subscribe to RSS Feed
- Permalink
07-16-2021 09:58 AM - edited 07-16-2021 10:01 AM
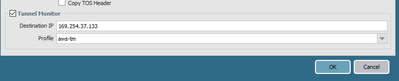
Are you running TM on the IPSec Tunnels themselves as well on the PBF rules? I was just doing it on the PBF rules but added them to the actual tunnel interfaces as well. Hoping that will solve my problem of having to manually restart both tunnels when one goes down and all traffic stops passing. I have no STATIC routes for any of the CIDRs on the other ends of both tunnels, can anyone tell me if this is right?
IPSec Tunnel:
PBF:
- 5636 Views
- 6 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- PA1420 IKE packet disappear between receive (ingress) and firewall session state in General Topics
- Dynamic IP at Spoke site in PAN-OS SD-WAN Hub/Spoke topology in Next-Generation Firewall Discussions
- Backup Internet with Ipsec VPN doing BGP in General Topics
- Validating Branch-to-branch IPv6 Connectivity in Prisma SD-WAN Discussions
- IPSec tunnel over IPSec tunnel not working in General Topics