- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Clarification on Web-browsing App
- LIVEcommunity
- Discussions
- General Topics
- Clarification on Web-browsing App
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2023 08:43 PM - edited 11-16-2023 08:53 PM
Thanks
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-17-2023 05:58 AM
Hi @SDon ,
The correct answer heavily depends on the fact if the traffic you are allowing will be decrypted or not.
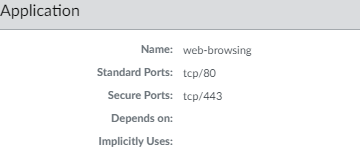
Any http-based traffic, for which PAN FW doesn't have specific application will be categorized as "web-browsing". So basically it is generic application for any http-based traffic.
"ssl" application can also be considered "generic", because it will match any traffic is encrypted with TLS/SSL, but no decryption is applied for it. Because traffic passing over the FW is not being decrypted firewall cannot tell which specific application is being used, or if it is some generic HTTP-based traffic.
"Application default" ports define which ports firewall will allow when you add this application to the rule. As you can imagine, firewall can identify applications, only when some real data has passed. But for any TCP-based application TCP session needs to be established first. Which means firewall will first need to match and allow traffic on Layer4 - source/dest IP and ports.
When you create rule matching only application "web-browsing", firewall will open both port tcp/80 and tcp/443.
TCP session will be allowed to establish so client will try to send some data.
If firewall detect clear-text HTTP-based traffic it will identify it as "web-browsing" and continue allowing the session.
If firewall detect TLS/SSL encryption and traffic match decryption rule, traffic will be decrypted and inspected again (for identification), if decrypted traffic is again clear-text generic HTTP-based traffic it will be again mapped to "web-browsing" application
If firewall detect non-HTTP-based traffic, it will perform another policy lookup to see if other rule is now matching and if not will deny the session, effectively closing the TCP session.
If firewall detect TLS/SSL encryption and traffic does not match decryption rule, traffic will be mapped/identified as "ssl" application (because FW cannot look futher). If your rule allow web-browsing application, traffic will stop matching this rule (because the app is identified as ssl) and effectively deny the rest of the session.
If you are trying to move from port-based to application-based policy, my suggestion would be to:
- Create rule with "any" application and service tcp/80 and tcp/443 at the bottom
- Utilize logs, ACC tab, Reports and Policy optimizer to periodically check what application have been identified by your firewall passing over this rule.
- Create rule above adding all the applications you want to allow.
However the effectiveness of the above approach again heavily depens on what traffic your firewall is configured to decrypt.
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-16-2023 08:54 PM
It looks like it would allow only "web-browsing" type of traffic on either port 80(clear text) or 443(encrypted).
Safely Enable Applications on Default Ports (paloaltonetworks.com)
- Mark as New
- Subscribe to RSS Feed
- Permalink
11-17-2023 05:58 AM
Hi @SDon ,
The correct answer heavily depends on the fact if the traffic you are allowing will be decrypted or not.
Any http-based traffic, for which PAN FW doesn't have specific application will be categorized as "web-browsing". So basically it is generic application for any http-based traffic.
"ssl" application can also be considered "generic", because it will match any traffic is encrypted with TLS/SSL, but no decryption is applied for it. Because traffic passing over the FW is not being decrypted firewall cannot tell which specific application is being used, or if it is some generic HTTP-based traffic.
"Application default" ports define which ports firewall will allow when you add this application to the rule. As you can imagine, firewall can identify applications, only when some real data has passed. But for any TCP-based application TCP session needs to be established first. Which means firewall will first need to match and allow traffic on Layer4 - source/dest IP and ports.
When you create rule matching only application "web-browsing", firewall will open both port tcp/80 and tcp/443.
TCP session will be allowed to establish so client will try to send some data.
If firewall detect clear-text HTTP-based traffic it will identify it as "web-browsing" and continue allowing the session.
If firewall detect TLS/SSL encryption and traffic match decryption rule, traffic will be decrypted and inspected again (for identification), if decrypted traffic is again clear-text generic HTTP-based traffic it will be again mapped to "web-browsing" application
If firewall detect non-HTTP-based traffic, it will perform another policy lookup to see if other rule is now matching and if not will deny the session, effectively closing the TCP session.
If firewall detect TLS/SSL encryption and traffic does not match decryption rule, traffic will be mapped/identified as "ssl" application (because FW cannot look futher). If your rule allow web-browsing application, traffic will stop matching this rule (because the app is identified as ssl) and effectively deny the rest of the session.
If you are trying to move from port-based to application-based policy, my suggestion would be to:
- Create rule with "any" application and service tcp/80 and tcp/443 at the bottom
- Utilize logs, ACC tab, Reports and Policy optimizer to periodically check what application have been identified by your firewall passing over this rule.
- Create rule above adding all the applications you want to allow.
However the effectiveness of the above approach again heavily depens on what traffic your firewall is configured to decrypt.
- 1 accepted solution
- 5584 Views
- 2 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- XFF IP Address Logging clarification and impact in General Topics
- Cortex XDR Pro – Does it scan USB devices upon insertion? in Cortex XDR Discussions
- EDL Scalability & Platform Limits – Best Practices in Next-Generation Firewall Discussions
- What PAN‑OS version should we choose as the recommended release today? in General Topics
- Panoarama M-300 Log Storage in Panorama Discussions




