- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Exclude all Zoom traffic from GlobalProtect VPN
- LIVEcommunity
- Discussions
- General Topics
- Re: Exclude all Zoom traffic from GlobalProtect VPN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-17-2020 03:24 AM
We have been trying to exclude all Zoom-related traffic from the GlobalProtect VPN tunnel.
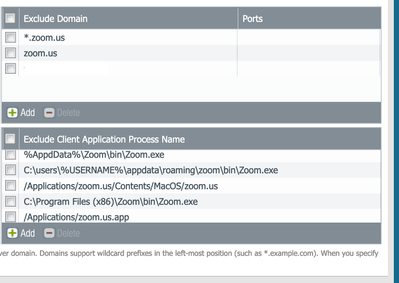
So far we have tried with: "*.zoom.us" exclusion configured directly on the GP gateway as a domain in:
Network --> GlobalProtect --> Gateways --> GW NAME --> Agent --> CLient Settings --> Split tunnel --> Domain and Application
But this seems to not completely do the trick as Zoom use some AWS default domains, not under *.zoom.us.
What approaches will work that does not involve having to manually exclude all the IP ranges as defined here?
The Zoom binary path seems to be this one, but I'm not sure PA supports wildcards on the path like this:
C:\Users\*\AppData\Roaming\Zoom\bin\Zoom.exe
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2020 01:43 AM
I finally found the solution. On our case, having the Zoom binary in %AppData% was making the split tunnel not working correctly and Zoom UDP/8801 traffic was sent through the tunnel.
We end up deploying the Zoom package centrally with SCCM to al laptops. Now, with Zoom on C:\Prgoram Files x86 the Zoom exclusion by Process is doing the trick finally.
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-07-2020 07:04 AM
thank you for sharing the solution. It really helps
~ Sai Srivastava Tumuluri ~
- Mark as New
- Subscribe to RSS Feed
- Permalink
04-27-2020 03:09 AM
Hi I resolved this setting as follows: We need to add CptHost.exe to offload UDP 8801.
%USERPROFILE%\AppData\Roaming\Zoom\bin\Zoom.exe
%USERPROFILE%\AppData\Roaming\Zoom\bin\CptHost.exe
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-05-2020 09:26 AM - edited 05-05-2020 09:49 AM
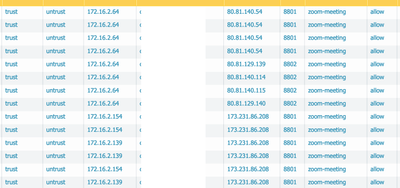
We are still having traffic flowing through even after excluding everything suggested in this thread. Seeing 8801/8802 in logs.
Also excluded the below per @togase's suggestion.
%USERPROFILE%\AppData\Roaming\Zoom\bin\Zoom.exe
%USERPROFILE%\AppData\Roaming\Zoom\bin\CptHost.exe
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-05-2020 09:35 AM
HI!
For Zoom domain excluded. So far it is not working. Symptom is not stable some client works and then stopped when they go zoom from Browser. It will not display. Case is on engineering team. If anyone got excluded domain working and stable. Please share your comments
Thank you
Daniel
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-06-2020 03:51 PM
Appreciate the information. Using this I was finally able to fully split both tcp 443 and udp 8801 traffic for Windows users. For Mac users I have 443 traffic split but 8801 will not and I can't figure out why. Anyone have any suggestions for Macs?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-06-2020 04:03 PM
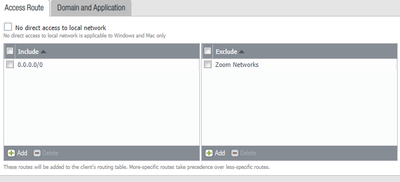
The only way we got it to work was to create an address group with all the zoom networks ( about 85 at the last count) and then monitor and add networks as they bring more online and exclude them in the access route tab
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-06-2020 08:28 PM
my recommendation is to start a zoom meeting with video and run the netstat command to see the what application is using the port
https://www.tecmint.com/find-out-which-process-listening-on-a-particular-port/
https://helpdeskgeek.com/how-to/use-netstat-to-see-listening-ports-and-pid-in-windows/
~ Sai Srivastava Tumuluri ~
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-08-2020 04:09 PM
Thank you Sai. It is very useful link. Actually we are not able to get the excluded domain (zooom or www.cisco.com ) working. Ticket was in engineering escalation
Daniel
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-18-2020 04:11 AM
what zoom networks did you use for this objects?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-18-2020 07:30 AM
We added all ranges but we are still seeing sessions to these zoom ips reaching the Palo Alto. Did you do any more action?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-18-2020 08:40 AM
When we looked at the network ranges last week, we saw 75 of them (I know @Jason_Mills mentioned 85 to his count but we only saw 75). This week (5/18/20) there are 88 IP ranges. We had to add these to our list:
69.174.108.0/22
140.238.128.0/24
152.67.20.0/24
152.67.118.0/24
152.67.180.0/24
158.101.64.0/24
168.138.16.0/24
168.138.48.0/24
168.138.72.0/24
168.138.244.0/24
193.122.32.0/22
193.123.0.0/19
193.123.40.0/22
193.123.128.0/19
Check to make sure you aren't missing any.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-18-2020 08:42 AM
We add all IPs in the excluded but if i go to monitor session i can see traffic to these IPs in PA.
Its like GPclient is not taking the routes added properly.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-18-2020 02:03 PM
It seems to be that there are new ranges coming on faster than they are updating the list of ranges.
- 72463 Views
- 59 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Restrict access via GlobalProtect to permit access to only a specific Google Drive Account/Folder in GlobalProtect Discussions
- Firwall is uable to send logs to the Panorma (Log collector is showing inactive) in Next-Generation Firewall Discussions
- Global Protect Internal Detection in GlobalProtect Discussions
- Rollout Strategy: GlobalProtect Disconnect Comments + 12-Hour Auto-Reconnect in GlobalProtect Discussions
- Stealth Rule Question in Next-Generation Firewall Discussions