- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
Firewall intercepts Virus between networks. False Positive???
- LIVEcommunity
- Discussions
- General Topics
- Re: Firewall intercepts Virus between networks. False Positive???
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 01:46 AM
Dear Palo Alto experts...,
We have various systems in our LAN seperated by our Palo Alto firewall.
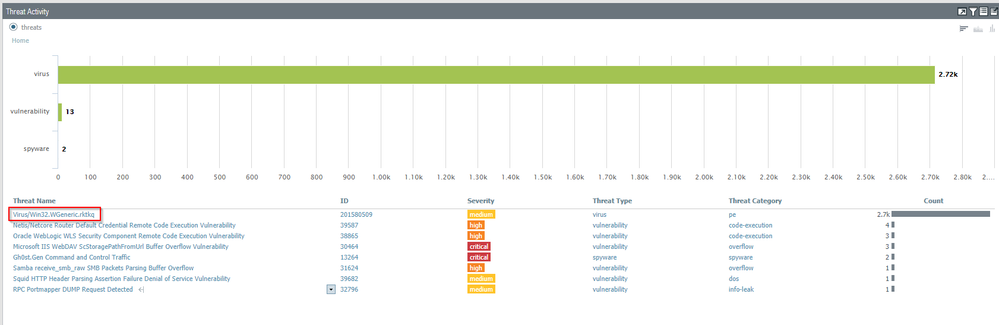
In the last 24 hours the firewall detected 2.7K times the virus "Virus/Win32.WGeneric.rktkq"
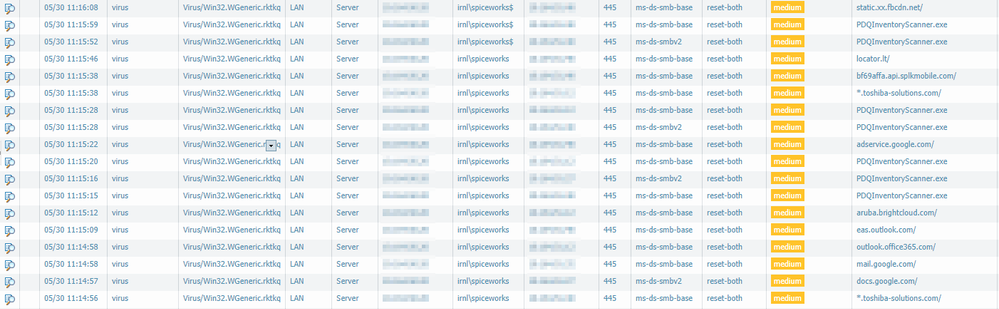
The systems are scanned for inventory by two programs. Spiceworks and PDQ inventory. The scan server is on one side of the firewall. The other servers are on the other side of the firewall.
The "Spiceworks" server has been scanned by our Kasperksy AntiVirus solution. No detections here.
What could be causing this? And if it is a false positive, what would the next path forward to solve this problem?
Any thoughts you might have are very welcome.
Remko
Accepted Solutions
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-06-2018 11:19 PM
I do not believe you do. This is the latest reply from Palo Alto
we've had a wave of few days last month where our static analysis caused a number of false positives due to an artifact that wasn't such a sure indicator of compromise yet it has had high value in our detectors; once we reviewed that IOC and adjusted it's weight in the static analysis algorithm, everything was fixed (regarding high false-positive rate). However, we still have few hashes to fix verdict on (such as few of those you shared).
I reviewed all the samples and they were flipped due to overly aggressive IOC weight.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 02:16 AM
Configure the firewall to gather a PCAP for the threat. Then you can send the PCAP to TAC for analysis.
If it's a false positive then likely a content update will fix it.
Cheers,
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 02:25 AM
Thanks... My apologies for being a bit blond here.. Bit of a newbie I guess. 🙂
How would I go about sending the PCAP to TAC for analysis.
Never done this. Have no idea were to go and where to begin.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 02:33 AM
I may have found something
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 02:34 AM
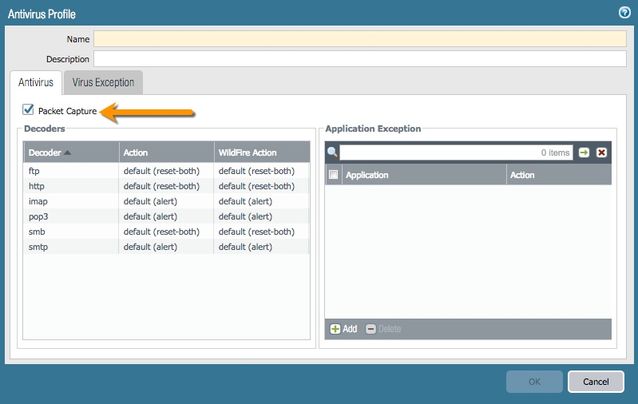
Enable packet capture in your Antivirus threat profile :
This setting will create a PCAP that you can download for analysis on the Monitor > Threat log page.
Cheers !
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 02:53 AM
I got my self a PCAP file. Thanks for pointing me in the right direction.
Now need to find where to upload it for analysis.
Not been able to find this yet.
I noticed I can also exclude this particular finding but perhaps better to wait for the verdict of Palo Alto
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 04:18 AM
For PCAP analysis, you can create a support case and upload the file to the case.
Cheers !
-Kiwi.
Cheers,
Kiwi
Please help out other users and “Accept as Solution” if a post helps solve your problem !
Read more about how and why to accept solutions.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 04:28 AM
Thanks, it appears I need to go through a local reseller in the Netherlands. I cannot create a case directly. This is cumbersome for just submitting a sample.
Thanks for helping me out here. Much appreciated!
Remko
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 05:01 AM - edited 05-31-2018 05:14 AM
Do you have a wildfire subscription? In yes, you could upload the proplematic executable (as it looks like in your logs the virus is detected the smb transfer of this executable) to wildfire as it will maybe show malicious (this signature was initially created by wildfire). Then you could report an incorrect verdict there without the need to create a case at your reseller.
But the "best" is probably still if you create a case at your reseller (and ask for premium support at next renewal so you will be able to create cases directly 😉
Regards,
Remo
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 05:22 AM
Yes we do.
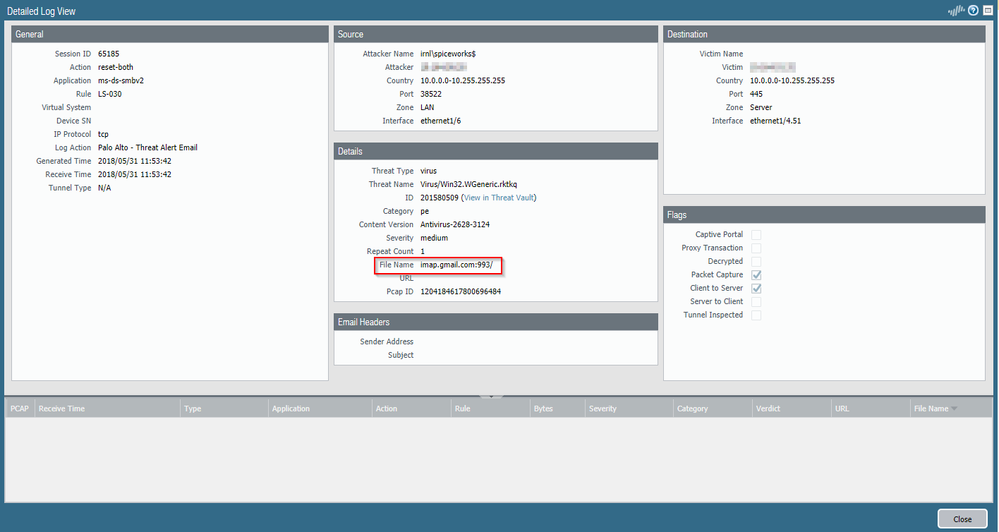
The file (PDQInventoryScanner.exe) as shown in the screenshot is classified as benign. So not sure why it is triggered.
In the screenshot it also shows certain URL's as the same virus.
Most likely the inventory scanner also checks cloud services for things like warrenty, etc.
I just do not understand why I have all of a sudden 2.7 K of virusses detected 🙂
I have submitted a case now with the local reseller.
Will keep you posted...
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 05:32 AM
Since when exactly do you have these in the logs? The signature was initially released by wildfire on 2018-05-21 and in normal threat updates on 2018-05-22. So depending when you have installed these updates, you probably have these alerts in the log since then... if this scanner runs continuously to do something.
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 05:52 AM
I started noticing these warnings yesterday. Prior to this, this particular "virus" was not found.
The report runs at night for the last 24 hours.
Yesterday the count was 1973.
For today (last 24 hours ) the count is 2040
It is hard to tell when exactly a scan is triggered. When the scan is > 7 days old. When a new application is installed a scanned is performed, etc.
Strange thing is that is also triggers on URL's
I am not sure why I am seeing these messages?
- Mark as New
- Subscribe to RSS Feed
- Permalink
05-31-2018 06:53 AM
Make sure that you also add a packet capture of one of these logs (SMB traffic with an URL as filename) to the case. This either is a very special attack in your network or - probably more likely - a bug.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-06-2018 12:53 PM
We also have this very same problem. Also running PDQ Inventory and Spiceworks. Do we need to upload a packet capture too?
Leo
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-06-2018 11:19 PM
I do not believe you do. This is the latest reply from Palo Alto
we've had a wave of few days last month where our static analysis caused a number of false positives due to an artifact that wasn't such a sure indicator of compromise yet it has had high value in our detectors; once we reviewed that IOC and adjusted it's weight in the static analysis algorithm, everything was fixed (regarding high false-positive rate). However, we still have few hashes to fix verdict on (such as few of those you shared).
I reviewed all the samples and they were flipped due to overly aggressive IOC weight.
- 1 accepted solution
- 10658 Views
- 16 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!