- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
FTP connections jumping rule
- LIVEcommunity
- Discussions
- General Topics
- FTP connections jumping rule
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
FTP connections jumping rule
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 04:46 AM - edited 06-14-2016 04:53 AM
Hi,
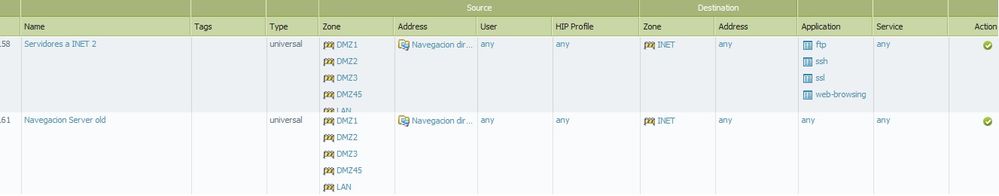
we have 2 rules. the first one filtering by application FTP
and the second one with the same source/destination like the rule above and using any/any permit.
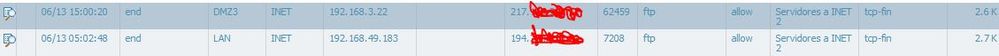
We run ftp connections. all these FTP connections should match in the first rule filtering by FTP, but we see matches in the any/any rule too.
In this rule should be match all the ftp connections (filter by FTP app, services any):
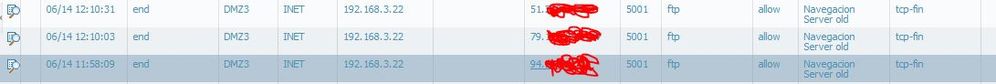
but we see connections in this rule too (any/any)
Why all the connections FTP not using the same rule (first one)???
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 05:35 AM
Hi,
Can you run the PCAP on the PA? Use filters to specify a particular host /IP and post the result.
Cheers,
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 06:22 AM
If during session application changes then unless you log at session start you see in log only last application identified.
For troubleshooting period can you open both of those policies and on the last tab (Actions) check both boxes "log at session start" and "log at session end"
Do you see only FTP in application field or Palo identifies it something else in the mean time?
After application shift rules are evaluated again and top rule should match again so strange issu but worth to try.
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 06:34 AM
The app is FTP, but i dont know why the second rule is matching if all the connections should go through first rule...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 06:45 AM
Can you take a screensot of the 2 FTP rules so we can see them please. Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 06:49 AM
Any chance you're running into an issue with the FTP rule not catching FTPs?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 06:56 AM
I attach both rules. Connections shoyuld only go through first rule, but we see FTP tries in the last one. Why?
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-14-2016 11:19 AM
From the rule screenshot, FTP should match 1st rule and not the 2nd rule as you pointed out.
Did you happen to add/modify the FTP rules during the time period in question? If so, it may be that the FTP session matched 1 rule and a rule change occurred afterward which would not take effect on the existing FTP session.
If you're still seeing this behavior where FTP is matching rule2, I recommend opening a Support cast to have it diagnose. Thanks.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2016 04:11 AM
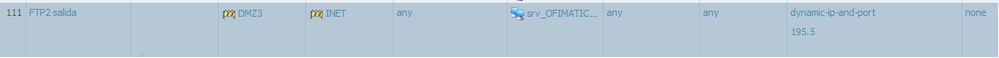
I checked the NAT rule for this FTP server and its weird this NAT rule.
It should be a static NAT??? currently its configured with dynamic ip and port... maybe this can caused problems?? The connections take different source ip nat to go to internet.....
Maybe this could cause the problem?? i think for this FTP use we should use a static ftp ...
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2016 04:27 AM
Is 195.5 address object?
Palo Alto Networks certified from 2011
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2016 05:45 AM
No, its the IP iwth no object created. I think NAT is not well created.
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2016 06:06 AM - edited 06-15-2016 06:07 AM
Hiya,
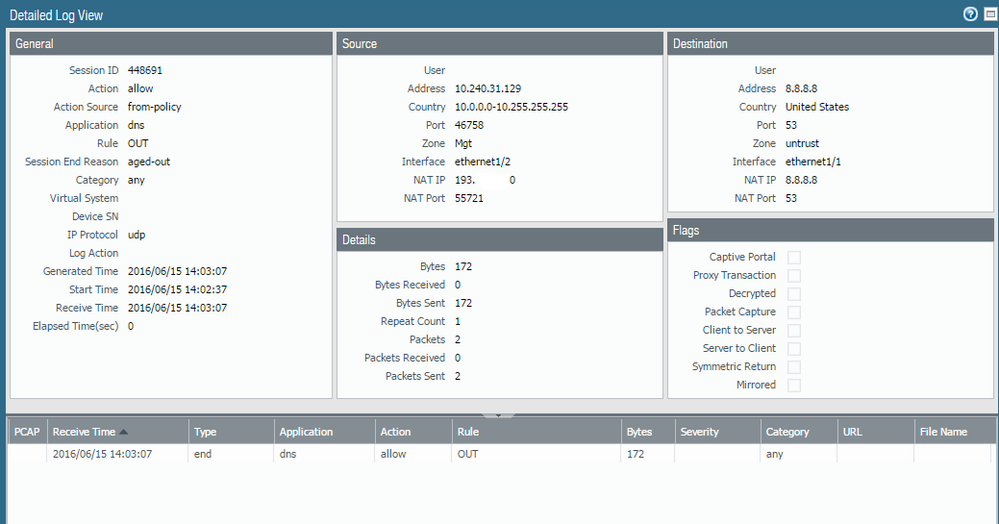
Kindly could you provide screenshots of the FTP sessions that hitting a correct policy and "any" "any" policy.
Example below:
- Mark as New
- Subscribe to RSS Feed
- Permalink
06-15-2016 07:20 AM
Can you also send screenshot of the session from session table.
Monitor > Session table
Click on the + sign to expand the view.
Session table view includes NAT policy used but traffic log screenshot does not.
Palo Alto Networks certified from 2011
- 6249 Views
- 12 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Prisma Access and Microsoft Tenant Restrictions in General Topics
- Stealth Rule Question in Next-Generation Firewall Discussions
- BIOC not supported in Cortex XDR Discussions
- Slow Download and Uploads From Various Cloud Providers in Next-Generation Firewall Discussions
- PA-VM in AWS with Decryption Rule - server side connection kept open in VM-Series in the Public Cloud