- Access exclusive content
- Connect with peers
- Share your expertise
- Find support resources
Click Preferences to customize your cookie settings.
Unlock your full community experience!
GP prompts for internal gw connectivity
- LIVEcommunity
- Discussions
- General Topics
- GP prompts for internal gw connectivity
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
GP prompts for internal gw connectivity
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2020 03:08 AM
Hi all,
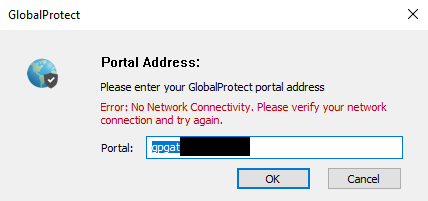
I've deployed a GlobalProtect installation solely for the purpose of User-ID. The GP agent connects to the internal portal/GW (one box) upon login with Kerberos SSO. However, when the internal gateway is not reachable (user has no network, user isn't on-prem), the GlobalProtect Agent notifies the user about this (no network / can't reach GW). Does anyone know how I can supress this warning?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2020 04:40 AM
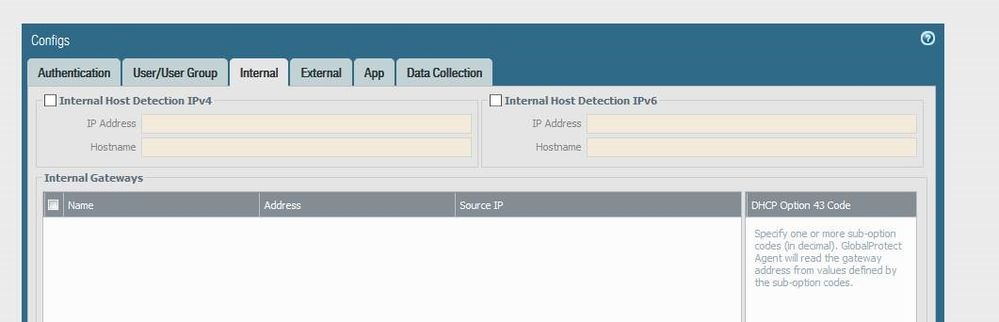
Internal host detection IPv4 is set to an internal on-prem IP and the hostname for it does not publicly resolve, plus internal gateways are configured..
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2020 04:57 AM
Have you tried making the portal external, the gateway internal with host detection and allowing access to the portal from internal network.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2020 05:05 AM
No, if possible we highly prefer not to have the portal externally available.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2020 05:12 AM
Sure, i understand, but how is the client going to know about the internal host detection if they cant get to the portal.
Portal info is cached but it does not include internal host detection. I know this much because we use it to prevent users connecting to gateways when on the LAN but if the portal cannot be contacted the internal host detection does not kick in and user attempts to connect to a cached portal.
So... I dont think you have much choice here...
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2020 05:49 AM
I actually don't mind if it can't get to the portal, I just don't want users to see the message -so it's more, can I suppress the message on the client itself or not?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-04-2020 06:15 AM
Yep, got it... it does say that in the first post.
I am not aware of message suppression.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2020 01:25 PM
I'm not quite sure on this, as I have not tried doing solely an internal gateway. However, why not try configuring the gateway as an internal gateway, and use the internal host detection, and list no external gateways?
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2020 01:59 PM
That is pretty much exactly the configuration at the moment.. 😞
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2020 02:17 PM - edited 03-09-2020 02:19 PM
Gotcha. You could change the connection method to on-demand, but I'm guessing that will mess with things when the users are on network.
While I know you said you prefer not to run the portal on a public interface, I'll offer this as one option to consider. You could configure the portal w/ a different authentication method (LDAP, local, SAML, whatever), and set a long cookie timeout (365 days for example). This would essentially let your machines authenticate with the portal once, and be done with it for a year (or longer, if you also allow the gateway logins to generate a cookie). If you wish, you could further secure this accdss using a certificate profile, and requiring machines to have a cert trusted by the firewall. Then, you could run your internal gateway on an internal interface w/ the kerberos SSO authentication. Then the machines will only attempt kerberos auth via SSO to the gateway when they detect that they are inside your corporate network using internal host detection.
Sorry, I know that isn't quite what you're looking for, but I don't know of a way to suppress the notifications other than these two suggestions. If GlobalProtect doesn't meet your needs in this area, captive portal might be a good way to capture user-id. We do this for some of our Mac users.
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-09-2020 02:54 PM
Well the whole idea is to keep it transparant and not have users authenticate to anything. I do suppose that if I were to use cookies it wouldn't pick up users logging in or out, and on-demand is exactly what we're trying to avoid (with captive portals on top of the list :-)). The agent should be invisible to the end users, but if no one knows an alternative I'm guessing it will be support to confirm or a feature request...
- Mark as New
- Subscribe to RSS Feed
- Permalink
03-10-2020 06:49 AM
@Arne-VDH wrote:Well the whole idea is to keep it transparant and not have users authenticate to anything. I do suppose that if I were to use cookies it wouldn't pick up users logging in or out
Yes, definitely don't want it more complicated than needing. In my experience, it's not the connection to the portal which registers user-id, but the gateway. If you accepted cookies for portal auth, but only accepted Kerberos SSO for the gateway, I wonder if this would still give you what you need. Again, your deployment is a bit different than the ones I've done, so just trying to throw ideas out there.
- 10002 Views
- 12 replies
- 0 Likes
Show your appreciation!
Click Accept as Solution to acknowledge that the answer to your question has been provided.
The button appears next to the replies on topics you’ve started. The member who gave the solution and all future visitors to this topic will appreciate it!
These simple actions take just seconds of your time, but go a long way in showing appreciation for community members and the LIVEcommunity as a whole!
The LIVEcommunity thanks you for your participation!
- Global Protect Internal Detection in GlobalProtect Discussions
- Strata Cloud Manager with NGFW in Strata Cloud Manager
- NATing Question in General Topics
- Firewalls in Active Active using Azure Internal Load balancer in VM-Series in the Public Cloud
- GlobalProtect prelogon and internal gateway detection in General Topics